
What Is Cybersecurity Framework: Why You Need It
Think of a cybersecurity framework not just as a document, but as the master blueprint for building a resilient digital 'house.' For IT professionals aiming to build robust security postures and advance their careers, understanding these frameworks is paramount. It’s not a single piece of software you can install, but a structured guide packed with best practices, standards, and solid recommendations for managing digital risk across an organization. At MindMesh Academy, we believe this foundational knowledge is critical for anyone pursuing certifications like CompTIA Security+, CISSP, or even cloud-specific security specializations.
Demystifying the Digital Blueprint
 A visual representation of a cybersecurity framework as a comprehensive digital blueprint.
A visual representation of a cybersecurity framework as a comprehensive digital blueprint.
Could you imagine building a house without a blueprint? You might end up with a sturdy front door but completely forget to put locks on the windows, leaving critical vulnerabilities. A cybersecurity framework prevents this exact kind of disjointed, ineffective security by providing a complete, organized plan from the outset. For IT professionals, this means moving beyond reactive "firefighting" to proactive, strategic defense.
Just as a construction blueprint lays out everything from the foundation and plumbing to the electrical wiring and alarm systems, a framework offers a clear roadmap for protecting your organization's most valuable digital assets. It ensures every piece of your security is considered and implemented in a coordinated, logical way, making it easier to prepare for and recover from incidents.
From Chaos to Cohesion
Without a framework, security efforts can feel chaotic and reactive. An IT team might rush to install a new firewall after hearing about one type of threat, while another department is focused on phishing training for a different one. Both are good ideas, but without a unified strategy, you're merely plugging holes as they appear, leaving other gaps wide open for attackers. This uncoordinated approach often leads to compliance headaches and increased risk exposure, a scenario many IT professionals grapple with daily.
A framework changes the game by creating a common language and a shared set of goals. It gets everyone on the same page, from the network engineers in the data center to the executives in the boardroom, about what needs protecting and the most effective way to do it. This strategic alignment is the bedrock of a truly resilient security posture, vital for certifications that cover governance, risk, and compliance (GRC) like CISM or CRISC.
A cybersecurity framework isn’t about buying more tools. It’s about using a structured methodology to make smarter, risk-based decisions about the people, processes, and technology you already have. It shifts the focus from "what products do we need?" to "what outcomes do we need to achieve?"
This structured approach gives you a repeatable and measurable way to manage security. Instead of guessing where your weaknesses might be, the framework guides you through a systematic process of identifying, assessing, and improving your defenses. It helps you answer the tough but essential questions that frequently appear on certification exams:
- What are our most critical digital assets and data (e.g., customer PII, intellectual property, cloud infrastructure)?
- What are the biggest threats we face (e.g., ransomware, insider threats, zero-day exploits impacting our AWS or Azure environments)?
- Are the security controls we have in place actually working effectively?
- How will we react and recover when—not if—a breach happens, minimizing downtime and data loss?
Core Functions of a Cybersecurity Framework Explained
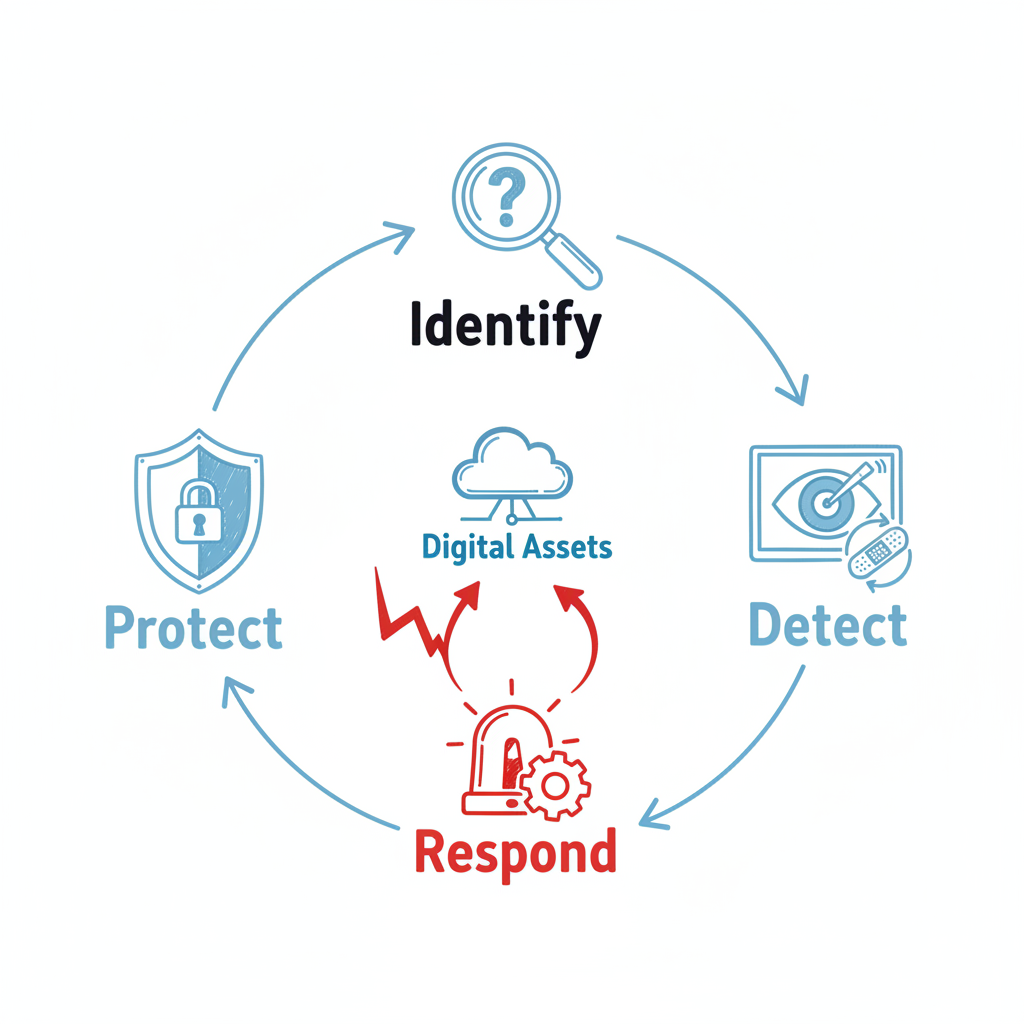
Most major frameworks, like the one from NIST, are built around five core functions. These functions provide a high-level, strategic view of the entire lifecycle of managing cybersecurity risk, a concept crucial for understanding almost any IT security certification. Here’s a quick breakdown using our house blueprint analogy, with a focus on real-world IT implications.
| Core Function | What It Means | House Blueprint Analogy | IT Professional's Focus (Example) |
|---|---|---|---|
| Identify | Understanding your digital assets, risks, and business environment. | Knowing what valuables are inside the house and identifying potential entry points for a burglar. | Performing asset inventories, risk assessments, vulnerability scanning, understanding business impact (e.g., data classification for a PMP project). |
| Protect | Implementing safeguards to prevent or limit the impact of a security event. | Installing strong locks, a security fence, and reinforced windows. | Implementing access controls (IAM in AWS/Azure), encryption, firewalls, security awareness training, patch management. |
| Detect | Putting systems in place to quickly identify when a security breach occurs. | Setting up motion detectors and security cameras that alert you to an intruder. | Deploying SIEM (Security Information and Event Management) systems, intrusion detection systems (IDS), log analysis, continuous monitoring. |
| Respond | Having a plan to take action once a security incident is detected. | Calling the police, containing the intruder, and assessing the immediate damage. | Developing incident response plans, activating playbooks, isolating compromised systems, communicating with stakeholders. |
| Recover | Developing plans for resilience and restoring capabilities after an incident. | Filing an insurance claim, repairing damages, and improving security for the future. | Data backups and restoration, disaster recovery plans, business continuity planning, post-incident reviews, forensic analysis. |
These five functions work together to create a continuous cycle of improvement, ensuring that your security posture evolves right alongside the threat landscape. Understanding this cycle is fundamental for certifications like CompTIA CySA+ or EC-Council CEH, which delve into practical security operations.
A Foundation for Modern Defense
This idea of a structured, risk-based approach has become fundamental to protecting digital operations around the world. One of the most influential examples is the NIST Cybersecurity Framework (CSF), first released back in 2014. It provides a voluntary system that helps organizations of any size manage their security risks through its five core functions: Identify, Protect, Detect, Respond, and Recover. Its design is particularly appealing to professionals seeking a flexible yet comprehensive model.
The CSF’s flexibility and common-sense structure have led to its widespread adoption, making it a foundational guide for countless businesses looking to build a more defensible and resilient organization. Many government contractors and organizations dealing with sensitive data in the U.S. often align their security programs with NIST.
The Building Blocks of a Strong Cybersecurity Framework
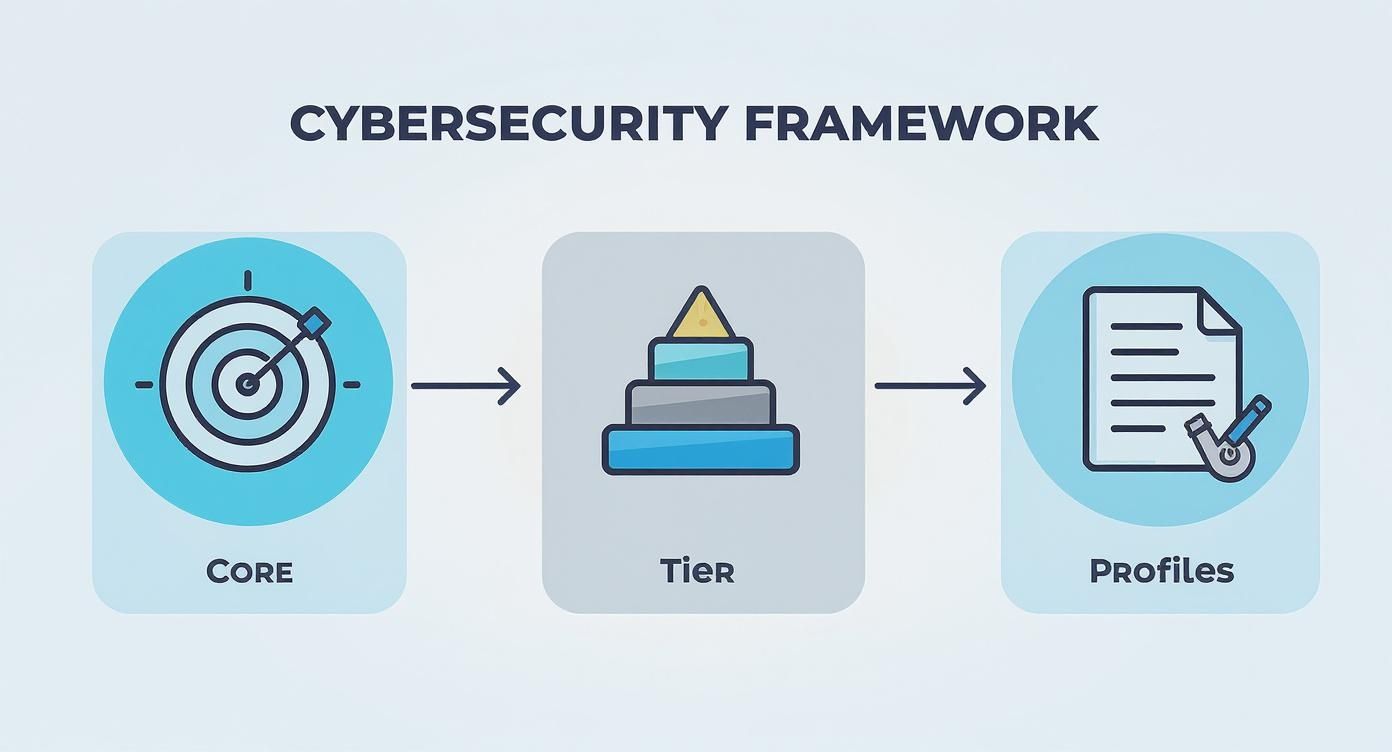
To truly grasp what a cybersecurity framework entails, you need to look under the hood. While the terminology might vary, almost all of them are built from three key parts: the Core, Implementation Tiers, and Profiles. These pieces work together to transform a big-picture security strategy into a practical, customized, and measurable action plan for any business.
Think of it like an architect's blueprint for a house. The Core is the list of standard features every safe building needs (like locks, alarms, and fire exits). The Tiers help you decide on the quality of those features—are you using a simple padlock or a high-tech biometric scanner, perhaps multi-factor authentication for cloud accounts? And the Profile is your personalized floor plan, tailored to your family's specific needs. Each part is separate but essential for building a solid defense.
The Framework Core: The "What"
The Core is the heart of the whole operation. It’s a detailed catalog of all the cybersecurity activities and desired outcomes your organization should be aiming for, all laid out in a logical, structured way. In short, it tells you what you should be doing to manage cyber risk. For an IT professional, the Core acts as a comprehensive checklist of best practices often covered in detail by certification objectives.
A great example is the NIST Cybersecurity Framework, which organizes its Core around five key functions: Identify, Protect, Detect, Respond, and Recover. These big ideas are then broken down into smaller, more specific categories and subcategories, giving you granular guidance on everything from access control to incident response. The Core answers the most basic question: What activities are absolutely critical for our security program?
Implementation Tiers: The "How Well"
Once you know what you need to do, the next obvious question is, how well are we actually doing it? This is where Implementation Tiers come in. They act as a sort of maturity scale, giving you a straightforward way to gauge how sophisticated and thorough your company's risk management practices truly are. This concept is vital for anyone taking exams focused on governance and organizational security.
Tiers usually move from a reactive, informal approach to a highly proactive and adaptive one. This scale helps organizations take an honest look at where they stand, much like a project manager (PMP-certified or otherwise) assesses project maturity.
- Tier 1: Partial – Risk management is mostly ad-hoc, and you're often just reacting to problems as they pop up. Security is not integrated into overall risk management.
- Tier 2: Risk-Informed – You're aware of the risks, but your security practices might not be consistent across the whole company. Some risk management processes are in place.
- Tier 3: Repeatable – You have formal security policies and procedures in place, and your teams actually follow them consistently. Risk management processes are standardized.
- Tier 4: Adaptive – Your organization is constantly learning and improving, using past incidents and future predictions to fine-tune its defenses. Security is fully integrated into strategic risk management.
These tiers aren't just for a report card. They create a clear roadmap for improvement, showing leadership exactly where to invest time and money to beef up their security posture. For example, moving from Tier 2 to Tier 3 might involve formalizing an ITIL-based incident management process.
Reflection Prompt: Consider your current organization or a past one. Which Implementation Tier would you assign to its cybersecurity practices? What specific evidence supports your assessment?
Profiles: The "Custom Fit"
This is where the framework becomes truly yours. A Profile takes the generic best practices from the Core and aligns them with your organization’s unique business needs, risk appetite, and available resources. A solid grasp of the underlying principles of risk management is vital here, as it helps you create a Profile that zeroes in on your biggest threats, whether they're compliance risks for HIPAA-regulated data or securing a complex AWS cloud environment.
A Profile bridges the gap between the generic best practices of the Framework Core and the unique operational reality of your organization. It makes the framework relevant and actionable for you, enabling a targeted approach to security.
Typically, you'll create two kinds of Profiles:
- A Current Profile: This is an honest snapshot of where your cybersecurity stands right now, mapping your existing activities back to the framework's Core. It answers: "Where are we today?"
- A Target Profile: This is your goal. It outlines your desired security outcomes and defines where you want your organization to be, considering future threats and business objectives. It answers: "Where do we want to be?"
The gap between your "Current" and "Target" profiles instantly gives you a prioritized action plan. It helps you focus your budget and effort on the changes that will make the biggest difference in reducing risk. For anyone looking to get this right, digging into the complete risk management process can provide the deeper context needed to build truly effective profiles, a skill highly valued in CISSP and CISM roles.
Comparing Major Frameworks: NIST vs. ISO and Others
Picking a cybersecurity framework is a bit like choosing a training plan. A marathon runner's plan won't work for a powerlifter, and a beginner's routine isn't right for a seasoned athlete. The best framework depends entirely on your company's industry, size, regulatory pressures, and what you’re ultimately trying to achieve with your security program. For IT professionals, understanding these distinctions is key to advising organizations and passing scenario-based certification questions.
Not all frameworks are built the same. Some are flexible guides meant for continuous improvement, while others are strict, auditable standards needed for compliance. Let's break down three of the heavyweights—NIST CSF, ISO/IEC 27001, and the CIS Controls—to see which might be the right fit for your organization or a particular client.
The NIST Cybersecurity Framework: The Flexible Guide
The NIST Cybersecurity Framework (CSF) is easily one of the most popular and adaptable frameworks out there, especially in the United States. It was developed by the U.S. National Institute of Standards and Technology to protect critical infrastructure, but it's so practical that companies of all shapes and sizes have adopted it. It's often referenced in certifications like CompTIA Security+ and CySA+.
Think of the NIST CSF less like a rigid rulebook and more like a collection of best practices from seasoned experts. It’s completely voluntary and designed to be flexible, helping you manage risk through its five core functions: Identify, Protect, Detect, Respond, and Recover. The goal is to create a common language for security and a clear, repeatable process for getting better over time, making it excellent for organizations prioritizing continuous improvement.
Because it isn't a formal standard, you can't get "NIST Certified." Instead, it’s a powerful tool for self-assessment that helps you build a strategic roadmap for your security goals, guiding the implementation of technical controls and security policies.
This screenshot from NIST shows how these five core functions create a complete cycle for managing security.
 The NIST Cybersecurity Framework's core functions illustrating a continuous risk management cycle.
The NIST Cybersecurity Framework's core functions illustrating a continuous risk management cycle.
This visual really drives home how the framework covers everything from preparing for an incident to cleaning up afterward, providing a holistic view of cybersecurity.
ISO/IEC 27001: The International Standard
If NIST is a flexible guide, ISO/IEC 27001 is the official, globally recognized standard for building an Information Security Management System (ISMS). An ISMS is just a formal way of saying you have a system in place to manage and protect sensitive company information. This standard is particularly relevant for IT professionals in governance, risk, and compliance (GRC) roles, or those aiming for certifications like CISM.
Unlike NIST, ISO 27001 is a benchmark that an organization can be audited and certified against. For companies doing business internationally, or those needing to prove adherence to strict security standards, this certification is often a must-have. It’s a signal to partners and customers that your security program is mature, verified, and trustworthy. It's less of a "what to do" list and more of a "how to manage it all" system, focusing on continuous improvement of the ISMS itself.
ISO 27001 certification acts as a global seal of approval. It demonstrates a formal commitment to information security management, which can be a powerful competitive advantage in the international market, instilling confidence in stakeholders.
Getting certified is no small feat. It involves rigorous documentation, internal audits, and a final review by an accredited third-party auditor. As you explore global standards, it’s interesting to see how companies are combining Global Standards like ISO 27001 with AI-powered risk detection to keep up with evolving threats.
The CIS Controls: The Hands-On Action Plan
While NIST and ISO operate at a high, strategic level, the Center for Internet Security (CIS) Controls get right down to the tactical details. The CIS Controls are a prioritized list of defensive actions—concrete steps you can take to block the most common and damaging cyberattacks. For a cybersecurity engineer or security analyst, these controls offer immediate, actionable guidance, often serving as practical implementation steps for broader frameworks.
Think of it as the "get it done" checklist for your security team, directly impacting daily operations and tool selection (e.g., configuring endpoint protection, securing cloud configurations in Azure). The controls are cleverly organized into Implementation Groups (IGs), which helps organizations focus on the most critical safeguards first, based on their resources and risk profile.
- Implementation Group 1 (IG1): This is your "basic cyber hygiene." These are the essential safeguards every single organization should have in place, often addressing 80% of common attacks.
- Implementation Group 2 (IG2): This builds on IG1 for companies with more digital assets and a greater risk of being targeted, requiring more advanced technical controls.
- Implementation Group 3 (IG3): This is for mature organizations that handle sensitive data and need to defend against sophisticated, determined attackers, often involving advanced security architectures.
Many organizations actually use the CIS Controls as the practical "how-to" guide for achieving the high-level goals outlined in NIST or ISO. They provide the specific actions needed to fulfill the broader strategic vision, making them excellent companions for implementing a security program. The structured nature of these controls shares some DNA with other operational methodologies. To see how this compares with other frameworks, you might want to check out our guide on what is ITIL service management.
At a Glance: NIST vs. ISO 27001 vs. CIS Controls
To make the choice clearer, here’s a quick side-by-side comparison of these three major frameworks, a table you might find useful for quick reference during exam preparation.
| Feature | NIST Cybersecurity Framework (CSF) | ISO/IEC 27001 | CIS Controls |
|---|---|---|---|
| Primary Goal | Provides a flexible, risk-based approach to improve overall cybersecurity posture. | Establishes, implements, and maintains a formal Information Security Management System (ISMS). | Offers a prioritized, actionable set of cyber defenses to stop common attacks. |
| Compliance | Voluntary. Used for self-assessment and program improvement. No formal certification. | Auditable. Leads to a formal, internationally recognized certification. | Voluntary. Used as a practical implementation guide. No formal certification. |
| Best For | U.S. organizations (public & private) of all sizes looking for a flexible starting point. | Organizations needing to prove compliance to international partners, clients, or regulations. | Organizations of any size needing a prioritized, hands-on action plan for technical controls. |
Ultimately, there's no single "best" framework. Many organizations find success by blending them—using NIST for overall strategy, ISO for management and compliance, and CIS for the day-to-day technical implementation. The right mix depends entirely on your unique needs, business context, and regulatory landscape.
Why Adopting a Framework Is a Smart Business Move
*Video: The Business Value of Cybersecurity Frameworks.*Thinking of a cybersecurity framework as just another IT checklist is a huge mistake. It's actually a strategic business decision that pays off in real-world resilience, a stronger reputation, and even a healthier bottom line. When you step back from the technical details, you see that a good framework provides a clear roadmap to turn security from a drain on resources into a genuine business asset. It's all about making smarter, more defensible choices about risk, a perspective valued by IT leaders and project managers.
Let's face it: security conversations between IT experts and company leaders can get lost in translation. A framework fixes that by giving everyone a common language. When a security chief can map their needs to a recognized standard like NIST, budget talks suddenly become much more productive. The conversation shifts from a vague "we need a new firewall" to a specific "we need to invest in this control to fulfill the 'Protect' function of our framework, which will lower our overall risk score by 15%." That's a language everyone understands, making it easier for IT professionals to advocate for resources.
Strengthening Risk Management and Resilience
At its heart, a cybersecurity framework is a powerful tool for managing risk. It forces an organization to take a hard look at its most critical assets, understand the specific threats they face, and put the right protections in place. This systematic approach gets you out of the reactive, "whack-a-mole" security game and into a proactive strategy focused on building true resilience, a core tenet of modern security operations.
This isn't just about preventing attacks; it's about being ready to respond and recover when one inevitably gets through. A well-implemented framework ensures that incident response plans are not just written down, but are tested and understood by everyone, from cloud engineers to help desk staff. The result is a tougher, more adaptable organization that can handle security incidents and bounce back with minimal disruption, protecting business continuity.
Simplifying Regulatory Compliance and Building Trust
Navigating the alphabet soup of regulations like GDPR, HIPAA, and CCPA can feel like an impossible challenge. A framework gives you a structured path to meet these complex demands. Many standards, such as ISO 27001, are specifically designed to align with various legal requirements, helping you tackle multiple mandates with one cohesive effort. For IT professionals, understanding how frameworks map to compliance is a valuable skill in regulated industries.
Adopting a framework sends a powerful signal to your customers, partners, and regulators: you take security seriously. It’s an act of due diligence that builds trust and can easily become a major competitive advantage, particularly when demonstrating adherence to international standards.
This commitment to due diligence also speaks volumes to investors and insurers. Being able to demonstrate that your security program is built on a recognized standard doesn't just build confidence in the boardroom—it can also lead to better cyber insurance premiums. Insurers are increasingly looking for mature, framework-based security programs before they'll write a policy, highlighting the direct financial benefits.
The Clear Financial Upside
If you're still on the fence, the financial argument should seal the deal. Proactive, structured security is simply cheaper than a chaotic, reactive cleanup after a breach. Following a framework to implement solid controls drastically reduces both the likelihood and the potential cost of a security incident. The data is clear on this. For instance, organizations that use a zero-trust architecture—a core concept in many modern frameworks—see breach costs that are, on average, $1.76 million lower than companies without one.
With the global cost of cybercrime expected to reach a staggering $10.5 trillion by 2025, the motivation to manage this risk systematically is undeniable. You can discover more insights about these cybersecurity statistics at AppseCure. Adopting a framework isn't an expense; it's a critical investment in your company's financial stability and future, underscoring the business value IT professionals bring by implementing such strategies.
Your Step-by-Step Guide to Implementing a Framework
 A team collaborates to plan and implement a cybersecurity framework, symbolizing a strategic roadmap.
A team collaborates to plan and implement a cybersecurity framework, symbolizing a strategic roadmap.
Knowing what a cybersecurity framework is and why you need one is the first major hurdle. Now for the real work: actually putting it into practice. Rolling out a framework can feel like a massive undertaking, but when you break it down into logical steps, it becomes entirely manageable. For IT professionals, this implementation roadmap translates theoretical knowledge into tangible security improvements.
Think of it this way: you wouldn't just show up at the gym and try to lift the heaviest weights on day one. You'd start by setting goals, figuring out your current fitness level, and then building a realistic workout plan. Implementing a security framework follows that same thoughtful, step-by-step progression. This isn't a one-and-done project; it’s the start of a continuous cycle of security improvement.
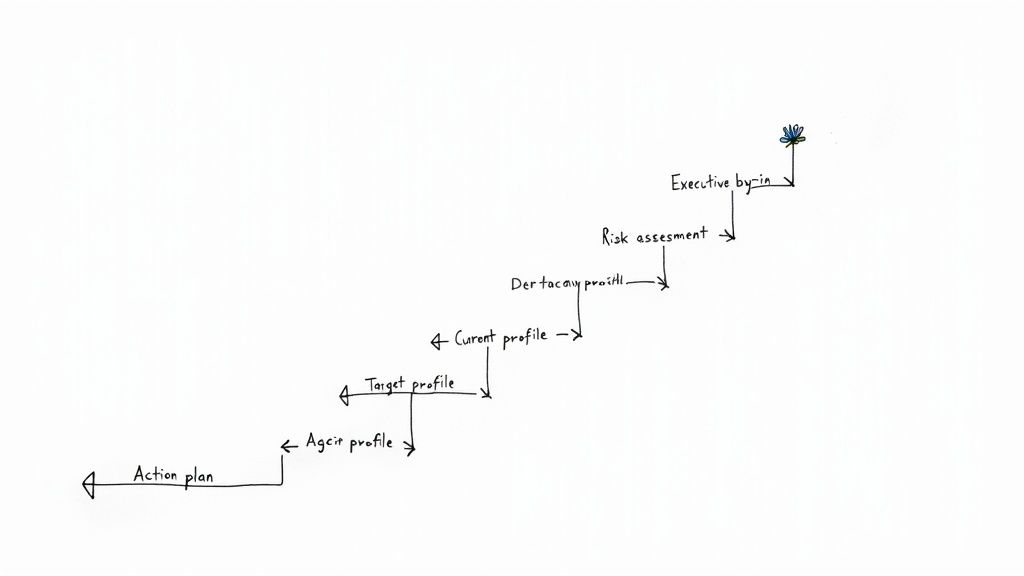
Phase 1: Prioritize and Define Scope
Before you write a single policy or buy any new software, you need to lay the groundwork. This means getting the right people in the room and drawing clear lines around what you want to accomplish first. Without this initial alignment, even the best plans can go off the rails, a common pitfall in large IT projects.
Your first move is to secure executive buy-in. A cybersecurity framework isn't just an IT issue—it touches every part of the business. Leadership needs to understand its value, champion the cause, and put real resources behind it. Once they're on board, pull together a cross-functional team with people from IT, security, legal, HR, and other key departments. This ensures you're looking at the problem from all angles, a strategy often taught in PMP or ITIL Foundation courses.
Next, you have to define the scope. Are you starting with one critical system (e.g., your customer database in Azure), a specific business unit, or the entire company? Kicking things off with a smaller, well-defined scope is a great way to score an early win and build momentum for a wider rollout.
Phase 2: Assess and Set Goals
With your team and scope locked in, it’s time to figure out where you stand today and where you need to be tomorrow. This calls for a brutally honest look at your current security posture, leveraging your expertise in areas like network security, cloud security, or data privacy. You can't draw a map to your destination if you don't know where you're starting from.
The heart of this phase is a comprehensive risk assessment. This process is all about identifying your most valuable assets, understanding the threats and vulnerabilities they face, and calculating the potential business impact if something goes wrong. This isn't just a technical checklist; it's a vital business analysis often covered extensively in CISSP or CISM exam objectives.
From this assessment, you'll create two critical profiles:
- Your Current Profile: A detailed snapshot of your security capabilities as they exist right now, mapped to the functions of your chosen framework (like the NIST CSF). It answers the question, "Where are we today?"
- Your Target Profile: This is your North Star. It outlines the security outcomes you're aiming for and defines the specific framework controls you need to implement to get there. It answers, "Where do we want to be?"
Phase 3: Analyze Gaps and Create an Action Plan
Now the real work begins. By comparing your Current Profile to your Target Profile, you'll uncover your security gaps—the specific areas where your defenses fall short of your goals. This gap analysis is the blueprint for your entire implementation strategy, allowing you to prioritize efforts effectively.
Once you know where the gaps are, you can build a prioritized action plan. Don't try to fix everything at once. That's a recipe for burnout. Instead, prioritize based on risk. Which vulnerabilities pose the greatest threat to your most critical assets (e.g., a critical web application vulnerable to SQL injection)? Tackle those first for the biggest and fastest return on your security investment.
The action plan is your bridge from theory to practice. It should break down large goals into smaller, manageable tasks with clear owners, timelines, and measurable success metrics, much like any well-structured IT project plan.
This plan has to be realistic. A major hurdle for many organizations is having the right people to execute the plan. As of 2025, about two-thirds of organizations report facing moderate-to-critical cyber skills shortages, which directly impacts their ability to implement a comprehensive framework. As the global cybersecurity outlook from the World Economic Forum shows, this means a framework must do more than guide technology; it must also shape policy, training, and hiring to build a truly resilient team.
Phase 4: Implement, Monitor, and Improve
At last, it's time to put your action plan into motion. This is an ongoing cycle of implementing new controls, updating policies, and training your people. Solid project management and clear communication are absolutely essential here to keep everyone on the same page, from cloud security engineers deploying new solutions to help desk staff understanding new procedures. Making these changes stick often requires a thoughtful approach to organizational change, and for a deeper dive on that, our guide on change management in IT processes provides some great strategies.
Remember, implementation isn’t the finish line. A cybersecurity framework is a living program that demands constant attention. You need to regularly review your progress, conduct periodic risk assessments, and update your profiles as your business and the threat landscape inevitably change. This continuous loop—assess, act, and improve—is what transforms your security from a static defense into a dynamic and resilient capability, a core principle of DevOps and SecOps methodologies.
Reflection Prompt: If you were leading the implementation of a new security control (e.g., multi-factor authentication for all cloud accounts), what specific steps would you take in Phase 4 to ensure successful adoption and continuous improvement?
Your Top Questions About Cybersecurity Frameworks Answered
Even after getting the hang of the basics, some practical questions always pop up when it's time to apply a cybersecurity framework to a real business. Let's tackle a few of the most common ones to help connect the dots between theory and practice for IT professionals.
Think of this as the FAQ section you'd get from a seasoned consultant or a security architect.
Is a Framework the Same as Compliance?
Great question, and the answer is no—but they are closely related. The easiest way to think about it is like this: a framework is your training plan, while compliance is the official rulebook for the race.
A framework, like the one from NIST, is a collection of best practices you choose to follow to get your security program in shape and manage risk effectively. It provides guidance on how to build strong security. Compliance, on the other hand, is about following mandatory rules set by an external authority, like HIPAA for healthcare data or GDPR for customer privacy. You don't have a choice in the matter; these are legal or contractual obligations.
A solid framework gives you a clear roadmap to hitting your compliance targets and staying there. But just having the map doesn't mean you've finished the journey. The framework guides your strategy; compliance is about meeting the specific, tactical demands and proving it.
Following a framework makes proving you're doing the right thing much easier during an audit. It organizes all your security efforts and shows you're serious about protecting your data, which is invaluable for GRC professionals.
How Often Should We Review Our Framework?
Your cybersecurity framework isn't a document you create once and then file away. It's a living, breathing part of your business that needs to adapt. The threats you face are constantly changing, new technologies (like generative AI) emerge, and so should your defenses. This dynamic approach is critical for maintaining an effective security posture.
As a baseline, you should conduct a full, formal review at least once a year. However, you'll want to revisit it immediately if certain things happen:
- You experience a major cyber incident (or a very close call), prompting a "lessons learned" review.
- Your business goes through a merger, acquisition, or a big operational shift (e.g., moving all infrastructure to AWS).
- You launch a new product or service, especially one that handles sensitive information.
- There's a major new threat or vulnerability that disproportionately affects your industry or technology stack.
- New regulations or compliance requirements are introduced.
The goal is continuous improvement, not a one-time check-in. This keeps your security posture relevant to the actual risks you face today, not the ones from last year.
Can a Small Business Really Use a Framework?
Absolutely. This is probably the biggest myth out there. Frameworks—especially flexible ones like the NIST CSF or the prioritized CIS Controls—are built to scale. They work just as well for a five-person startup as they do for a Fortune 500 company.
For a small business with a tight budget, a framework is a game-changer. It helps you make smart, risk-based decisions instead of trying to "boil the ocean" with limited resources. You can focus your limited time and money on protecting your most critical assets—your "crown jewels"—first, rather than reacting to every perceived threat.
It takes powerful, enterprise-level security concepts and makes them accessible and manageable. This ensures that even the smallest companies can build a strong defense against the threats they're most likely to face, protecting their reputation and future growth.
Ready to master the concepts behind industry-leading certifications like CompTIA Security+, CISSP, or AWS Certified Security - Specialty? MindMesh Academy provides expert-curated study materials and evidence-based learning techniques to help you not just pass your exams, but truly understand the material and apply it in real-world scenarios. Accelerate your career by visiting https://mindmeshacademy.com to explore our courses and elevate your cybersecurity expertise.

Written by
Alvin Varughese
Founder, MindMesh Academy
Alvin Varughese is the founder of MindMesh Academy and holds 15 professional certifications including AWS Solutions Architect Professional, Azure DevOps Engineer Expert, and ITIL 4. He's held senior engineering and architecture roles at Humana (Fortune 50) and GE Appliances. He built MindMesh Academy to share the study methods and first-principles approach that helped him pass each exam.