What is a Bastion Host? A Quick Guide to Secure Access
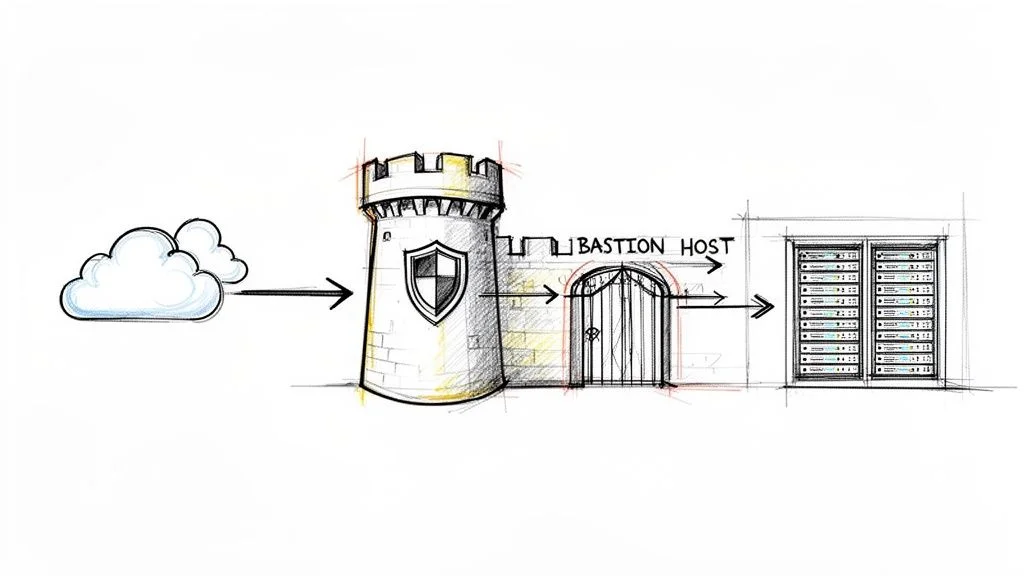
Think of your private network not just as a collection of servers, but as a high-security fortress safeguarding your most critical assets—databases, application servers, and sensitive customer data. You wouldn't leave a dozen entrances unsecured for anyone to wander through, would you? Instead, you'd funnel all access through a single, heavily fortified gatehouse, meticulously controlled and monitored. In the realm of IT infrastructure, this gatehouse is precisely what we call a bastion host.
A bastion host is a specialized server strategically deployed within a network, engineered from the ground up to withstand external attacks. It acts as the singular, secure bridge for administrators who need to manage internal systems residing in private network segments, effectively isolating sensitive resources from direct public internet exposure. For IT professionals pursuing certifications like AWS Certified Solutions Architect, Azure Administrator, or CompTIA Security+, understanding the bastion host concept is fundamental to designing and implementing secure network architectures. MindMesh Academy is committed to providing clear, actionable insights into such critical topics, preparing you for both exams and real-world challenges.
Understanding the Bastion Host
The core philosophy behind a bastion host is to establish a single, hardened entry point for administrative access. Rather than exposing numerous internal servers, each with its own potential vulnerabilities, to the public internet, you centralize all management connections through one intensely secured machine. This significantly reduces your network's attack surface—a key principle in modern cybersecurity and a recurring theme in certification exams.
Consider it the digital equivalent of a bank vault's massive, reinforced door. Before you can reach the safety deposit boxes (your private servers), you must pass through this secure entrance (the bastion host). This singular control point allows you to concentrate your most robust security measures, such as multi-factor authentication (MFA), comprehensive auditing, and stringent access controls, precisely where they matter most.
The Core Purpose of a Bastion Host
At its essence, a bastion host is a tactical tool for reducing your network's attack surface. By channeling all direct internet access for administrative purposes to a single, hardened server, you drastically simplify your security management challenge.
Here’s a breakdown of its primary objectives:
- Controlled Administrative Access: It acts as the exclusive gateway for administrative protocols such as SSH (Secure Shell for Linux/Unix systems) and RDP (Remote Desktop Protocol for Windows servers). This setup prevents direct SSH or RDP connections from the internet to your internal application or database servers.
- Centralized Auditing and Logging: Every connection and command executed through the bastion host can be meticulously logged. This creates an invaluable, chronological audit trail, providing a clear record of who accessed what, from where, and when. This capability is crucial for compliance, incident response, and forensic analysis, aligning with requirements for certifications that cover security operations (e.g., CySA+).
- Enhanced Security Posture (Defense in Depth): The bastion host serves as a formidable outer layer in a multi-layered security strategy. If an attacker breaches your perimeter, they must first compromise the bastion. This provides precious time for your security systems to detect the intrusion and for your team to respond before critical assets are reached. It acts as a "sacrificial lamb," designed to absorb initial attacks.
Why It Is a Foundational Security Component
The concept of using a hardened gateway isn't a recent innovation; it's a battle-tested principle that has underpinned network security for decades. Its importance surged in the early 1990s as networks became more interconnected and complex. Security professionals quickly recognized that defending a broad, porous perimeter was unsustainable.
The strategic shift was towards creating focused points of defense. This approach became so fundamental that by the mid-2000s, it was an established best practice across industries. It represented a crucial evolution from basic firewalling to a more sophisticated, access-centric security model that remains highly relevant today, especially in cloud environments where perimeter definitions can blur. For further reading, understanding the history of bastion hosts and their strategic importance in modern security can offer valuable context for your certification journey.
Reflection Prompt:
- How does the concept of a bastion host align with the "principle of least privilege" or "defense in depth" strategies commonly discussed in IT security certifications like Security+ or CISSP?
To put it simply, here are the key traits that define a robust bastion host:
Core Characteristics of a Bastion Host
| Characteristic | Description | Security Benefit |
|---|---|---|
| Public-Facing | Deliberately placed in a public subnet, it is the only server exposed to the internet for administrative access. | Isolates all other internal resources (application servers, databases) from direct public exposure, significantly reducing the attack surface. |
| Minimalist Design | Runs only the absolute essential services required for its administrative gateway function (e.g., SSH daemon, RDP service). | Eliminates unnecessary software, open ports, and services that could introduce vulnerabilities, making it harder to compromise. |
| Hardened OS | The underlying operating system is aggressively secured through custom configurations, regular patching, and specialized security tools. | Makes the bastion host itself highly resistant to common exploitation techniques and vulnerabilities. |
| Intensive Monitoring | Subject to continuous logging, auditing, and real-time alerts for any suspicious activity or configuration changes. | Provides immediate detection of potential breaches or unauthorized access attempts at the network's critical entry point. |
| Proxy/Gateway Role | It does not store sensitive data or run applications; its sole purpose is to broker secure connections to internal servers. | Limits the impact of a potential compromise, as an attacker gaining access to the bastion finds no valuable data or persistent foothold. |
These characteristics work in concert to establish a formidable security checkpoint for your entire infrastructure, a design pattern frequently tested in cloud certification exams.
How a Bastion Host Works in Your Network
To truly grasp the function of a bastion host, visualize its strategic placement within your network architecture. In any modern cloud environment (AWS VPC, Azure VNet, GCP VPC), your resources are segmented into distinct security zones. Your most valuable assets—such as private databases and application servers—are securely isolated within a private subnet, explicitly configured to be inaccessible from the public internet.
The bastion host, conversely, resides in a public subnet. This serves as a controlled "Demilitarized Zone" (DMZ) between the untamed public internet and your protected private network. This deliberate placement is central to its design. The bastion host becomes the secure conduit, the only approved pathway for administrators to traverse from the external world into your tightly controlled private zones. It efficiently funnels all administrative access, be it SSH for Linux or RDP for Windows, through a single, intensely monitored checkpoint. Crucially, no other machine within your private network ever directly exposes itself to the internet.
The Art of Hardening
A bastion host is far more than just a server with a public IP address; it's a meticulously crafted fortress. The process of transforming a standard server into this secure entity is known as hardening, and it is driven by the principle of minimalism. Imagine stripping a high-performance race car down to its absolute essentials—if a component doesn't directly contribute to speed or stability, it's removed.
For a bastion host, this translates to aggressively shrinking its attack surface. The objective is to eliminate every conceivable point of entry or vulnerability an attacker might exploit.
This diagram visually encapsulates the three fundamental concepts driving a bastion host: its function as a gateway, its hardened state, and its enablement of comprehensive auditing.

As depicted, its primary role is to act as a fortified, logging-enabled entry point for all administrative activities.
Hardening a bastion host isn't a one-time task; it's an ongoing, disciplined process. Typical steps include:
- Minimal Software Installation: The host should only run the absolute bare minimum software necessary for its function. If it’s solely for SSH access, then only the SSH daemon (SSHd) should be active. Avoid installing web servers, mail clients, development tools, or any other non-essential applications.
- Strict Firewall Rules: Configure the operating system's firewall (e.g.,
iptableson Linux, Windows Firewall) and associated cloud security groups (e.g., AWS Security Groups, Azure Network Security Groups) to block all inbound network ports except the one explicitly needed for administration (e.g., TCP port 22 for SSH, TCP port 3389 for RDP). Limit source IP addresses to known administrative networks. - Disabled Non-Essential Services: Any system service or background process not critical for the bastion's core gateway function must be disabled. This includes services like FTP, HTTP, database servers, or GUI desktops on headless Linux bastions.
- Aggressive Patch Management: The operating system and any remaining software (like the SSH daemon) must be obsessively kept up-to-date with the latest security patches. Automated patching tools are highly recommended.
- Secure Configuration: Implement strong password policies (even if using SSH keys), disable root login over SSH, use key-based authentication, and enforce strict file permissions.
By running only essential services, a properly hardened bastion host can reduce its potential attack surface by as much as 70-75% compared to a general-purpose server. It ceases to be a flexible, multi-purpose machine and transforms into a dedicated, specialized security appliance.
A Look at the Connection Flow
So, how does an administrator actually leverage this secure gateway? The process involves a two-step, "jump-host" approach that maintains strict separation between external networks and your private internal infrastructure.
- Initial Connection: The administrator first connects from their local machine (e.g., their workstation) directly to the bastion host's public IP address. This connection is heavily secured, often requiring a robust SSH key pair and multi-factor authentication (MFA).
- Internal Jump: Once securely authenticated and logged into the bastion host, the administrator then initiates a second connection, "jumping" from the bastion to the target server located in the private subnet. From the perspective of the private server, the connection appears to originate only from the bastion host's trusted internal IP address.
This two-hop process is foundational to many cloud network security designs, particularly in AWS Virtual Private Clouds (VPCs), Azure Virtual Networks (VNets), and Google Cloud VPCs. For anyone studying for a cloud certification, a solid grasp of how virtual networks and secure access patterns function is crucial. You can dig deeper into these advanced VPC concepts for AWS to truly master the topic and prepare for your exams.
Reflection Prompt:
- If an attacker managed to compromise an administrator's local machine, how does the two-hop bastion host connection flow still provide a layer of protection for your private servers?
Ultimately, this setup guarantees that an administrator's external machine never makes direct contact with sensitive internal servers. The bastion host vigilantly stands guard as a strict intermediary, inspecting, brokering, and logging every action that passes through it.
Comparing Bastion Hosts with Other Access Methods
In the complex landscape of network security, it's easy to encounter a lexicon of terms that seem to overlap. Bastion host, jump box, VPN—at first glance, they all appear to be methods for secure remote access. While they indeed share the overarching goal of protecting your infrastructure, they achieve this through fundamentally different mechanisms and are designed for distinct use cases. Thinking of them as specialized tools in a cybersecurity toolkit is helpful: you wouldn't use a wrench when a screwdriver is required. Understanding these nuances is critical for architects and security professionals, and often a key differentiator in certification questions.
Let's dissect their key differences.
Bastion Host Versus VPN
This comparison often leads to confusion, as both are synonymous with secure remote connections. However, they operate at vastly different scopes and grant fundamentally different levels of network access.
A Virtual Private Network (VPN) establishes an encrypted tunnel that essentially extends an administrator's or user's computer directly into the private network. Once connected, the user's machine behaves as if it's physically present on the internal LAN, granting broad network-level access to many internal resources. This is ideal for general employee access to office resources but represents a significant trust model. When considering various access methods, it's always helpful to understand how they compare against established solutions like Virtual Private Networks (VPNs).
A bastion host, in contrast, is far more surgical. It does not grant general network access. Instead, it provides session-level access to a specific target machine. It's akin to a security guard escorting you directly to a single server, supervising your work, and then escorting you out. It's purpose-built for precise, audited administrative tasks, not for providing broad network access.
The Nuance Between a Bastion Host and a Jump Box
Here's where terminology can be particularly misleading, as "bastion host" and "jump box" (or jump server) are often used interchangeably. This is a critical distinction that can have significant security implications.
A jump box is simply an intermediary server you connect to first before making a subsequent connection ("jumping") to your final destination. While it provides a basic layer of indirection, a standard jump box might not possess much more inherent security than any other server on your network. Its primary function is convenience or network segmentation.
A true bastion host is a jump box that has undergone meticulous hardening specifically for security. We're talking about a severely stripped-down operating system, all unnecessary services aggressively disabled, stringent firewall rules in place, and continuous, detailed monitoring. It's a jump box elevated to a highly secure, purpose-built security appliance.
To illustrate: any car can transport you from point A to B, but only a specially constructed armored vehicle is engineered to withstand an attack during the journey. A typical jump box is the car; a bastion host is the armored vehicle.
Mistakenly referring to a simple jump box as a "bastion host" without undertaking the rigorous hardening process creates a dangerous illusion of security, potentially exposing a vulnerable target at your network's perimeter.
Bastion Host Versus NAT Gateway
In the cloud computing paradigm, it's also common to conflate bastion hosts with NAT Gateways. While both are typically positioned at the edge of your private network, their functions are fundamentally different, and they handle traffic in opposing directions.
A bastion host is designed explicitly for controlling inbound traffic. Its entire purpose is to furnish a secure, monitored entry point for administrators attempting to connect into the private network to perform management tasks.
A NAT Gateway (Network Address Translation) is engineered exclusively for outbound traffic. It enables instances within your private subnets—such as web servers or databases without public IP addresses—to initiate connections out to the internet for activities like software updates, patch downloads, or accessing external APIs. Crucially, a NAT Gateway does not permit any external entity on the internet to initiate a connection back to those private instances; it's a one-way egress mechanism.
Putting It All Together
To synthesize these distinct access control options, it's helpful to view them side-by-side. Each serves a specific, vital role in a well-architected and secure network infrastructure, concepts frequently evaluated in certification exams.
Bastion Host vs VPN vs Jump Box vs NAT Gateway
| Technology | Primary Use Case | Access Level | Security Focus |
|---|---|---|---|
| Bastion Host | Secure, audited administrative access to internal servers | Session-level (e.g., SSH, RDP) | Hardened, single entry point for inbound admin traffic; reduces attack surface |
| VPN | General remote access for end-users or site-to-site connectivity | Network-level (full network segment access) | Encrypted tunnel for broad inbound user traffic; extends network securely |
| Jump Box | General-purpose intermediary server for indirect access | Session-level (e.g., SSH, RDP) | Basic access control; often lacks rigorous hardening and monitoring |
| NAT Gateway | Enabling controlled internet access for private resources | N/A (Outbound only, no inbound initiation) | Hiding private instances from inbound internet traffic; facilitates egress |
This table clearly delineates how each tool is purpose-built to address a specific security challenge.
It's also imperative to acknowledge the continuous evolution of cloud security. Modern cloud-native tools are increasingly offering alternatives that can reduce or even eliminate the need for a traditional bastion host. For example, many organizations now leverage services like AWS Systems Manager Session Manager for secure access. This approach provides audited shell access directly to instances without ever opening an inbound port or requiring you to manage a separate server, signifying a shift towards more integrated, identity-based security aligned with Zero Trust principles.
Deploying Bastion Hosts in the Cloud
Transitioning from theoretical concepts to practical implementation, setting up a bastion host in a major cloud environment is a fundamental skill for any cloud engineer prioritizing security. While the core tenets of hardening and isolation remain universal, each major cloud provider—AWS, Azure, and Google Cloud—offers its unique approach. You can opt for a traditional, self-managed virtual machine (VM) deployment or leverage slicker, fully managed services.
Knowing which deployment strategy to employ is crucial for constructing a secure and manageable access framework. When deploying a bastion, you are deeply engaging with the core components of cloud infrastructure. A strong understanding of basics like Infrastructure Cloud Services (IaaS) is indispensable. This foundational knowledge allows you to correctly configure virtual networking, security groups, and virtual instances, laying a robust and secure groundwork.
Reflection Prompt:
- Considering the varying approaches to bastions in AWS, Azure, and GCP, which method do you think best aligns with the "principle of least privilege" and why?
Let's examine how this looks across the "big three" cloud platforms.
Amazon Web Services: The Classic EC2 Bastion
The traditional, and still widely adopted, method for implementing a bastion host in AWS involves launching a dedicated Amazon EC2 (Elastic Compute Cloud) instance. This approach offers unparalleled control, allowing you to select the operating system, rigorously harden it to your organization's precise specifications, and install any custom security tools required.
Here’s the typical deployment strategy for an EC2 bastion:
- Launch an EC2 Instance: Provision a small, lightweight Linux instance (Amazon Linux 2 or Ubuntu Server are popular choices) and strategically place it within a public subnet inside your Virtual Private Cloud (VPC). Ensure it has a public IP address or is associated with an Elastic IP.
- Lock Down the Security Group: This is the most critical step. Configure the EC2 instance's Security Group (acting as a virtual firewall) to permit inbound SSH traffic (TCP port 22) only from a highly restricted and tightly controlled list of static IP addresses. This typically includes the IP ranges of your corporate VPN, specific administrative workstations, or your office network. All other inbound ports should be denied by default.
- Define Outbound Rules: Configure the outbound rules of the same Security Group to allow the bastion host to initiate SSH connections out to the private instances you intend to manage. This establishes a strictly controlled, unidirectional flow for administrative access from the bastion to your internal servers.
While this manual setup grants maximum flexibility, it also means you assume full responsibility for the operational overhead: regular patching, diligent monitoring, and general upkeep of the bastion host. This level of self-management is a common topic for AWS Certified SysOps Administrator and Solutions Architect Associate exams.
Microsoft Azure: Bastion as a Service
Microsoft offers a more streamlined approach with its fully managed service, Azure Bastion. This is a Platform-as-a-Service (PaaS) offering, meaning Azure abstracts away the complexities of managing the underlying VM, operating system, and patching. You simply focus on enabling secure access.

The significant advantage of Azure Bastion is that it allows you to connect to your private Azure VMs directly through the Azure portal via an HTML5-based web client. Crucially, your target VMs within the VNet do not require public IP addresses or jump boxes, which further shrinks your network's attack surface.
You deploy the Azure Bastion service into a dedicated subnet within your virtual network. It then facilitates secure RDP and SSH access over SSL directly from your web browser. This not only simplifies management but also integrates seamlessly with Azure's identity and security tools, such as Azure Active Directory (Azure AD). If you're studying for an Azure certification, particularly the AZ-104 Microsoft Azure Administrator exam, you absolutely need to know how to configure Azure Bastion—it's a high-priority topic.
Google Cloud: Secure Access with IAP
Google Cloud Platform (GCP) champions an even more modern, identity-centric approach with its Identity-Aware Proxy (IAP). Leveraging IAP for TCP forwarding often negates the need for a traditional bastion host altogether. Instead of relying on network perimeter defenses, IAP controls access to your virtual machines based on who the user is, rather than where they are connecting from.
IAP is a cornerstone of Google's Zero Trust security model, also known as BeyondCorp. It operates on the principle of "never trust, always verify." Every single request to connect is meticulously checked against identity and context-based rules (e.g., user identity, device posture, location) before access is granted. This represents a significant paradigm shift from traditional network firewalls to a smarter, user- and identity-focused security posture.
With IAP, administrators connect using the gcloud command-line tool, which securely tunnels their SSH traffic. Your GCP VMs do not require public IP addresses, and you can eliminate the need to manage inbound firewall rules for SSH ports. Access is managed through granular IAM (Identity and Access Management) roles, making it an exceptionally clean, flexible, and secure method for managing your instances, directly addressing concepts vital for GCP Professional Cloud Architect and Security Engineer certifications.
The impact of properly implemented bastion hosts or their modern alternatives is substantial. Studies consistently show that deploying a bastion host can reduce an organization's exposed attack surface by 70-75% by consolidating exposed services. Furthermore, layering multi-factor authentication on top of this can diminish unauthorized access attempts by an incredible 99.9%, underscoring their critical role in a robust security strategy.
Essential Security Best Practices for Your Bastion Host
Consider your bastion host as the most critical entry point to your entire network fortress. If this gatehouse has a weak lock or a careless guard, the entire castle is at risk. Therefore, ensuring the bastion itself is impeccably secure isn't merely a good idea—it's the fundamental purpose of its existence. Hardening a bastion host involves methodically transforming a standard server into a highly specialized security appliance.
These practices are not mere suggestions; they are non-negotiable requirements for constructing a bastion that can effectively withstand attacks and genuinely protect your critical internal systems. Each best practice serves to eliminate a potential vulnerability that an attacker might otherwise exploit.
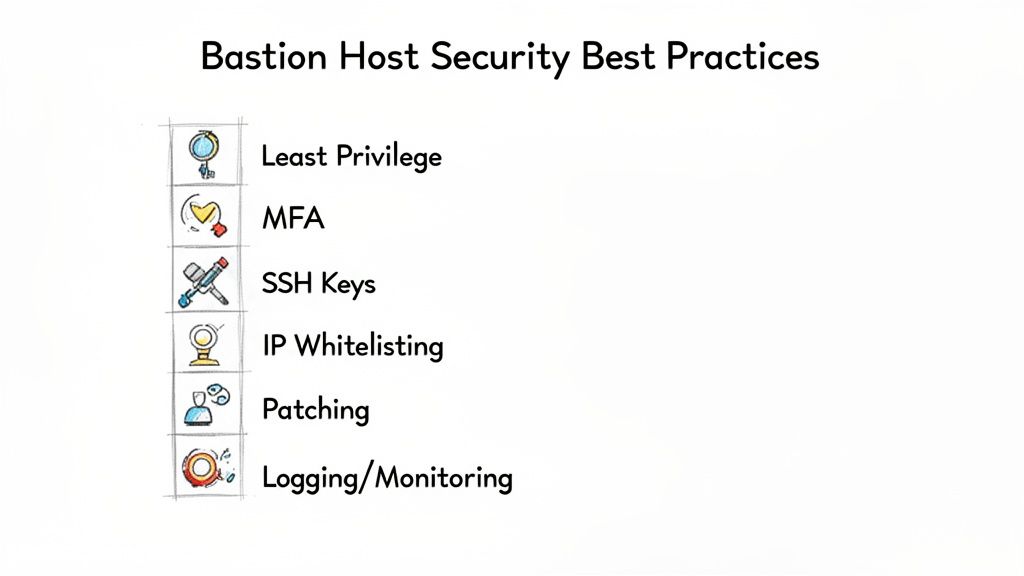
Apply the Principle of Least Privilege (PoLP)
The foundational philosophy underpinning every secure bastion host is the Principle of Least Privilege (PoLP). This simple yet profoundly powerful idea dictates that every user, every process, and every service should be granted only the absolute minimum permissions and access necessary to perform its intended function—and nothing more. This approach drastically constrains your attack surface and severely limits the potential damage if an account or process is ever compromised.
Instead of assigning broad administrative rights, implement granular access controls. An administrator whose role is merely to restart a web server on a private instance should not have any access to database servers or sensitive configuration files. This level of precision, often managed through Role-Based Access Control (RBAC) and IAM policies, is your most effective first line of defense, a concept emphasized in every major cloud and security certification.
Enforce Multi-Factor Authentication (MFA)
In today's threat landscape, traditional passwords alone are woefully inadequate, especially for a high-value target like a bastion host. Implementing Multi-Factor Authentication (MFA) is arguably the single most impactful security enhancement you can deploy. It's not an exaggeration: numerous studies consistently demonstrate that MFA can thwart over 99.9% of automated attacks that rely on stolen credentials.
MFA compels users to verify their identity using at least two distinct authentication factors:
- Something they know: A strong password or a complex passphrase.
- Something they have: A time-based one-time password (TOTP) from an authenticator app (e.g., Google Authenticator, Authy), a physical security key (e.g., YubiKey), or a hardware token.
- Something they are: Biometric data such as a fingerprint scan or facial recognition.
This layered authentication mechanism ensures that even if a password is compromised, the attacker is stopped cold without the second factor. For any system acting as a critical gateway into your network, MFA is an absolute imperative, a common requirement for certifications like CISSP and PCI DSS compliance.
Implement Robust Logging and Monitoring
If you aren't actively observing your network's front door, you'll never detect someone attempting to pick the lock. Your bastion host demands comprehensive logging capabilities to capture every single event that occurs on it. This generates a detailed, immutable audit trail that is invaluable for real-time threat detection and for meticulous post-incident forensic investigations.
As a minimum, you must capture:
- All successful and failed login attempts.
- The source IP address of every connection.
- The exact commands executed by each user during their session.
- Precise timestamps for the beginning and end of every session.
- Any configuration changes applied to the bastion host itself.
A critical security blunder is storing these vital logs directly on the bastion host. Never do this. An attacker who successfully breaches the bastion will almost immediately attempt to delete or alter these logs to erase their tracks. Instead, ensure all logs are streamed instantly and in real-time to a separate, centralized, and tamper-proof log management system. Examples include AWS CloudWatch Logs with cross-account logging, Azure Monitor Log Analytics, Google Cloud Logging, or a dedicated Security Information and Event Management (SIEM) platform (e.g., Splunk, ELK Stack, QRadar). This ensures log integrity and availability for compliance and security analysis.
Whitelist Static IPs and Use SSH Keys
Why merely react to threats when you can proactively block them from the outset? IP whitelisting is an excellent proactive security measure. You configure your cloud security groups or network firewalls to accept inbound connections only from a predefined, approved list of static IP addresses or CIDR blocks. This typically includes the IP ranges of your corporate offices, VPN endpoints, or specific trusted partner networks. All other inbound traffic is dropped by default, preventing reconnaissance and brute-force attacks from unknown sources.
Furthermore, you should completely disable password-based logins for SSH and transition exclusively to SSH keys. SSH keys leverage public-key cryptography, offering a significantly more secure authentication method than passwords, which can be guessed, brute-forced, or stolen. A user authenticates with their private key (stored securely on their local machine), which the server verifies against their corresponding public key. This cryptographic handshake is virtually impossible to brute-force and eliminates the risk associated with weak or reused passwords.
It's also crucial to remember that the SSH key pair is solely for authentication. The actual encryption of your session traffic is handled by separate, ephemeral session keys generated for each connection, further enhancing security. Effective key management strategies are also a vital part of this best practice.
Common Questions About Bastion Hosts
As you begin to integrate bastion hosts into your security architecture, or prepare for certification exams, a few practical questions invariably arise. Let's address the most common inquiries from IT professionals and certification candidates.
Are Bastion Hosts Still Relevant in a Zero Trust World?
Absolutely. In fact, a bastion host can be considered an excellent enabler for constructing a Zero Trust architecture. The fundamental premise of Zero Trust is "never trust, always verify," and a bastion host provides a perfect enforcement point for this policy, particularly for access to your most sensitive internal systems.
It is not an outdated concept; rather, it’s a tangible mechanism for putting Zero Trust principles into practice. A bastion host helps you to verify explicitly by enforcing strong identity checks (like MFA) and enables you to grant least privileged access by channeling all administrative traffic through one tightly controlled, fully audited checkpoint. The bastion host isn't an alternative to Zero Trust—it's a robust building block that supports and strengthens a Zero Trust security posture.
Can a Bastion Host Become a Single Point of Failure?
It certainly can, but only if you design and deploy it without considering high availability. This is a classic architectural risk, and just as you wouldn't run your entire business on a single firewall or router, the same critical thinking applies here. For any serious production environment, high availability for your bastion hosts is non-negotiable.
To mitigate the risk of a bastion host becoming a single point of failure (SPOF) and ensure continuous administrative access, you must build in resilience from the very beginning of your design:
- Deploy multiple bastion hosts: Distribute your bastion instances across different availability zones (or even separate geographical regions for disaster recovery) within your cloud provider's infrastructure.
- Utilize Auto-Scaling Groups: Place your bastion hosts within an auto-scaling group. This ensures that if an instance fails or becomes unhealthy, a new one is automatically launched to replace it, maintaining the required capacity and availability.
- Implement a Load Balancer: Position a network load balancer (e.g., AWS Network Load Balancer, Azure Load Balancer, GCP Internal Load Balancer) in front of your multiple bastion instances. The load balancer can intelligently route administrative traffic only to healthy, operational bastions, providing a single, resilient entry point.
Implementing these strategies transforms the bastion from a potential weak link into a highly available, resilient gateway, a design pattern frequently encountered in AWS Certified Solutions Architect and Azure Solutions Architect Expert exams.
What Information Should I Log on a Bastion Host?
The objective is to establish a comprehensive, tamper-proof audit trail. You need to capture sufficient detail to reconstruct precisely what occurred during any administrative session, whether for compliance audits (e.g., HIPAA, PCI DSS), security investigations, or forensic analysis after an incident.
As a minimum, you should be capturing and forwarding:
- All login attempts, both successful and failed, including the username, timestamp, and source IP address.
- The source IP address for every inbound connection to the bastion.
- The exact commands each user executes during their administrative session (often achieved via shell logging or specific monitoring tools).
- Timestamps for when every session started and ended.
- Any configuration changes made to the bastion host itself (e.g., changes to network settings, security groups, software installations).
Here's the golden rule repeated for emphasis: Never, ever store logs on the bastion host itself. If an attacker successfully compromises the bastion, the immediate priority will be to delete or modify logs to conceal their activities. All logs must be streamed in real-time to a separate, centralized, and tamper-proof system like AWS CloudWatch Logs, Azure Monitor Log Analytics, or a dedicated SIEM platform (e.g., Splunk, Elastic Stack). This ensures log integrity and availability even if the bastion itself is compromised, a critical concept for ITIL and security certifications.
Should I Install Security Tools on a Bastion Host?
Yes, but with extreme discernment and caution. A bastion host's primary strength derives from its minimalist design and tiny attack surface, so every single piece of software you add requires a rock-solid justification. The "less is more" philosophy is paramount here.
A few essential security tools are not just good ideas; they are pretty much required to maintain its hardened state and detect threats. Consider integrating:
- Intrusion Detection Systems (IDS) or Host-based IDS (HIDS): To monitor for and flag suspicious activity, unauthorized access attempts, or known attack signatures.
- File Integrity Monitoring (FIM): To alert administrators if critical system files, configuration files, or binaries are unexpectedly modified, deleted, or created.
- Antivirus/Anti-Malware Scanners: As a baseline defense against known threats, although the minimalist design should inherently reduce this risk.
- Security Information and Event Management (SIEM) Agents: To forward logs and security events to your centralized SIEM system for analysis.
What you absolutely must avoid is installing anything that isn't directly related to its core function of secure connection brokering or security monitoring. Every additional package, library, or service introduces another potential vulnerability that could be exploited. When it comes to bastion hosts, treat it as a dedicated, purpose-built security appliance, not a general-purpose server that can run other applications. This disciplined approach is a hallmark of secure system administration.
Ready to master these crucial concepts and pass your next certification exam with confidence? MindMesh Academy offers expertly crafted study guides, practice questions, and evidence-based learning tools designed to help you not just memorize, but truly understand complex technical material. Elevate your career and achieve certification success—start your journey today at AWS CloudOps Engineer Associate Practice Exams.

Written by
Alvin Varughese
Founder, MindMesh Academy
Alvin Varughese is the founder of MindMesh Academy and holds 15 professional certifications including AWS Solutions Architect Professional, Azure DevOps Engineer Expert, and ITIL 4. He's held senior engineering and architecture roles at Humana (Fortune 50) and GE Appliances. He built MindMesh Academy to share the study methods and first-principles approach that helped him pass each exam.