10 Vendor Management Best Practices for 2025
10 Vendor Management Best Practices for IT Professionals in 2025
In today's interconnected business world, effective vendor management is no longer a mere operational task—it's a strategic imperative that directly impacts an organization's agility, security, and profitability. For IT professionals, mastering vendor relationships is crucial for navigating complex projects, ensuring service continuity, and maintaining compliance, making it a vital skill often tested in certifications like PMP, ITIL, and various security credentials. Moving beyond basic transactional interactions towards strategic partnerships is key to unlocking innovation, building resilience, and optimizing costs. This shift is a fundamental pillar of a robust enterprise strategy. For a comprehensive understanding of how vendors fit into the broader operational landscape, exploring a complete international supply chain management guide can provide valuable context.
This guide outlines 10 essential vendor management best practices designed to transform your organization’s procurement processes into a powerful competitive advantage. By implementing these detailed, actionable strategies, IT professionals can mitigate risks, enhance service delivery, and unlock significant value from their entire supply chain. Each practice detailed below offers a clear roadmap, moving from foundational principles like vendor selection and contract management to advanced strategies involving strategic segmentation and collaborative innovation. Whether you're refining an existing framework or building one from scratch, these insights will provide a clear path to success and strengthen your profile as a knowledgeable IT leader. MindMesh Academy aims to equip you with the practical knowledge to excel in these areas.
1. Vendor Selection and Due Diligence: Building a Strong Foundation
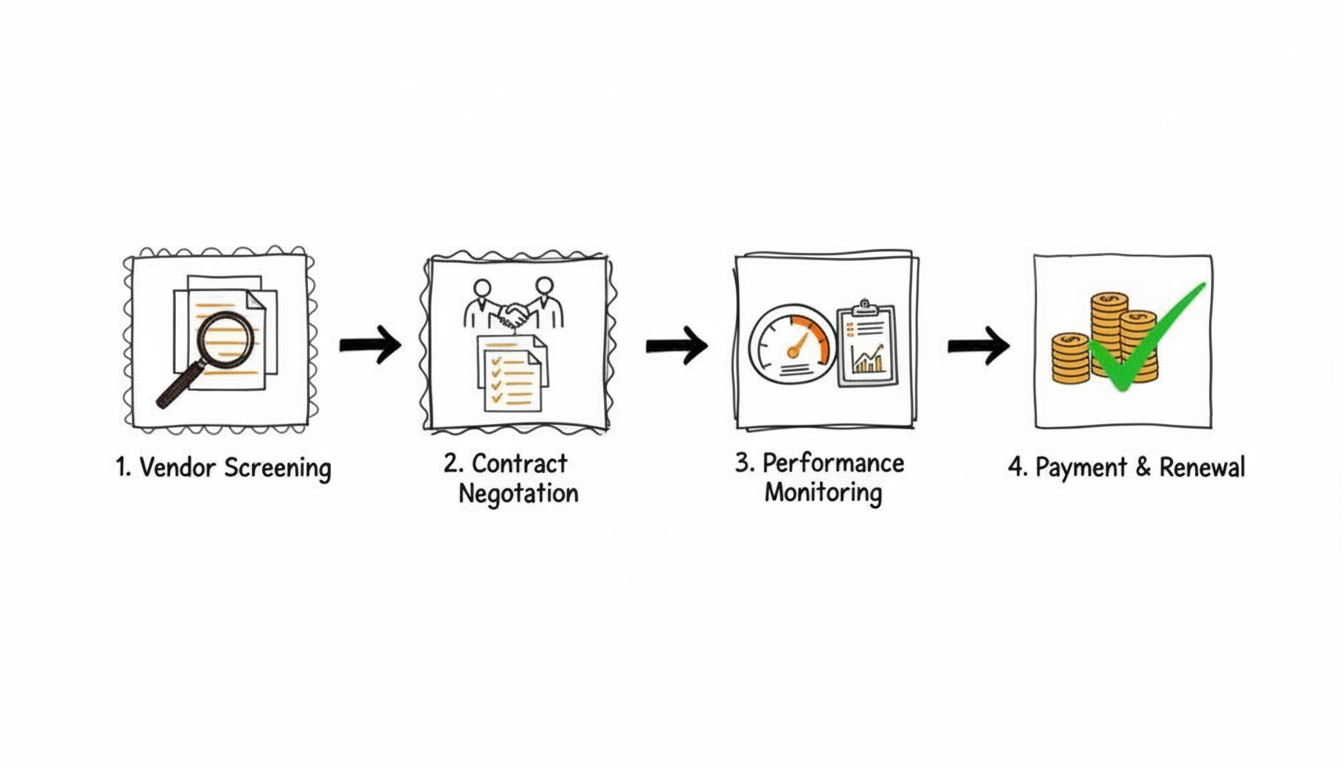
The bedrock of any successful vendor relationship is a rigorous and comprehensive selection process. For IT professionals, this initial phase, centered on robust due diligence, extends far beyond comparing price quotes. It involves a systematic evaluation of potential partners against a predefined set of criteria to ensure they not only meet immediate technical and operational needs but also align with your organization's long-term strategic goals, security postures, and compliance requirements. Effective vendor selection is a critical risk mitigation strategy, preventing costly disruptions and ensuring operational stability.
This practice is fundamental because partnering with an unstable, insecure, or non-compliant vendor can introduce significant financial, operational, and reputational risks. Consider an organization migrating to the cloud: thorough due diligence on a potential cloud service provider (CSP) like AWS or Azure would involve deep dives into their security certifications (e.g., ISO 27001, SOC 2), data residency policies, and disaster recovery capabilities. Similarly, in highly regulated sectors, healthcare organizations conducting stringent vendor credentialing to protect patient data and comply with HIPAA regulations is a non-negotiable. This structured approach is a cornerstone of effective vendor management best practices and crucial for professionals pursuing certifications like CompTIA Security+, CISSP, or CISM.
How to Implement Rigorous Due Diligence
To execute this effectively, your organization must establish a clear, repeatable process. Involving key stakeholders from different departments like finance, legal, IT, and cybersecurity is crucial for a holistic assessment.
- Develop Standardized Scorecards: Create a detailed evaluation scorecard with weighted criteria. Categories should include financial stability, technical capabilities (e.g., API integration, scalability), security protocols (e.g., encryption standards, incident response plans), quality control processes, and cultural fit. For IT, a strong emphasis should be on security and architectural alignment.
- Conduct Thorough Vetting: Go beyond the vendor's proposal. Independently verify all certifications (e.g., CCPA, GDPR readiness), check references, and conduct technical interviews or even proof-of-concept deployments when possible to see their operations and technology firsthand.
- Document Everything: Maintain a clear audit trail of all communications, evaluations, and decisions. This documentation is vital for compliance (e.g., for auditors reviewing PMP procurement processes) and internal governance.
Reflection Prompt:
- How does your organization currently assess the security posture of new IT vendors? What specific certifications or audit reports do you require?
By formalizing your selection and due diligence, you create a strategic advantage, ensuring every new partnership strengthens your organization's technical and operational integrity. To dive deeper into the initial stages of bringing vendors on board, explore our guide on the management of project procurement.
2. Establishing Clear Contracts and Service Level Agreements (SLAs)
Once an IT vendor is selected, the next critical step is to formalize the relationship with legally sound contracts and precisely defined Service Level Agreements (SLAs). This practice moves beyond a simple handshake agreement, creating a clear, legally enforceable framework that outlines every aspect of the partnership. It defines expectations, responsibilities, performance metrics, and consequences, serving as the definitive guide for the vendor relationship. Strong contracts are essential for preventing misunderstandings, protecting both parties from potential disputes, and laying the groundwork for effective ITIL service management.
This practice is a cornerstone of effective vendor management best practices because ambiguity is the root of most vendor-related conflicts, especially in complex IT environments. For instance, an IT outsourcing contract must have a detailed SLA specifying system uptime guarantees (e.g., 99.99% availability for mission-critical applications) and response times for technical support (e.g., "Resolve Priority 1 incidents within 30 minutes"). Similarly, a cloud service agreement with AWS or Azure will detail compute resources, data transfer limits, and data retention policies. Without these explicit terms, performance becomes subjective and unenforceable, leading to service degradation and financial loss, which could impact project timelines (PMP candidates should note this) and overall service quality (ITIL framework compliance).
How to Implement Clear Contracts and SLAs
Developing effective contracts requires collaboration between procurement, legal, technical, and operational teams to ensure all requirements are captured accurately. The goal is to create a document that is both comprehensive and easy to understand for all parties involved.
- Define Specific, Measurable Metrics: Avoid vague terms like "timely response." Instead, use quantifiable Key Performance Indicators (KPIs), such as "Resolve critical issues within four hours," "Maintain a product defect rate below 0.5%," or "Achieve 99.95% uptime for the SaaS platform." For IT, metrics like Mean Time To Repair (MTTR) or Mean Time Between Failures (MTBF) are crucial.
- Outline Remedies and Penalties: Clearly state the consequences for failing to meet SLA targets. This could include service credits, financial penalties, specific escalation paths for remediation, or even termination clauses for persistent non-performance.
- Include Clauses for Review and Renewal: The business and technological environment changes rapidly. Build in periodic review intervals (e.g., quarterly or annually) to assess performance, adjust terms as needed (e.g., reflecting new security standards or service requirements), and define the process for contract renewal or termination.
Certification Connection:
- The ITIL 4 Foundation certification emphasizes the importance of clear service level agreements and their role in defining and managing service expectations between providers and consumers, directly linking to this best practice.
By creating unambiguous contracts and SLAs, you establish a solid foundation for accountability and performance. To understand more about structuring service-based agreements, explore our insights on what ITIL service management is.
3. Vendor Performance Management and Monitoring
Once a vendor is onboarded, especially in IT, the focus shifts to ensuring they consistently deliver on their promises. This is where continuous performance management and monitoring become essential. This practice involves systematically tracking and evaluating vendor performance against predefined Key Performance Indicators (KPIs) and Service Level Agreements (SLAs). It is an ongoing, data-driven process that enables the early identification of potential issues, supports continuous improvement, and ensures you receive the value you contracted for, aligning with proactive project control in PMP methodology.

This practice is critical because a "set it and forget it" approach leads to value erosion, increased risk, and potential project delays. For example, a managed service provider (MSP) responsible for your network infrastructure needs continuous monitoring of network uptime, latency, and incident resolution times. Similarly, a software development vendor requires tracking of bug fix rates, feature delivery timelines, and code quality metrics. In cloud environments, monitoring cloud spend against budget and optimizing resource usage (a key skill for AWS Certified Solutions Architect or Azure Administrator Associate) is a form of vendor performance management. Proactive monitoring is a core component of effective vendor management best practices, transforming vendor relationships from transactional to strategic partnerships.
How to Implement Proactive Performance Monitoring
Establishing a transparent and consistent monitoring framework is key to managing vendor performance effectively. This requires clear communication and the right tools to turn data into actionable insights.
- Develop Comprehensive Scorecards: Create and share vendor scorecards that track metrics like quality of service, delivery timeliness, responsiveness to inquiries, adherence to security policies, and cost-effectiveness. Use a mix of leading indicators (e.g., training completion rates) and lagging indicators (e.g., number of incidents) for a predictive view.
- Schedule Regular Business Reviews (RBRs): Hold quarterly or semi-annual reviews to discuss performance data, address challenges, align on future goals, and identify opportunities for improvement. This fosters a collaborative, rather than confrontational, relationship, which is crucial for PMP stakeholder engagement.
- Utilize Automation and Dashboards: Implement vendor management software or dashboards (e.g., through an existing ERP or dedicated VRM system) to automate data collection and provide real-time visibility into performance. This allows IT teams to spot trends, identify anomalies, and act quickly to prevent minor issues from escalating.
Key Takeaway:
- Continuous monitoring isn't just about accountability; it's about fostering an environment of shared improvement, vital for long-term IT service reliability.
By consistently monitoring performance, you not only hold vendors accountable but also create opportunities for joint problem-solving and innovation. To learn more about setting clear expectations from the start, see our insights on creating a project management communication plan.
4. Implementing Vendor Relationship Management (VRM) Systems
To effectively manage a growing portfolio of suppliers, especially the diverse range of IT vendors (SaaS providers, hardware suppliers, consulting firms), organizations must move beyond spreadsheets and siloed data. Implementing a dedicated Vendor Relationship Management (VRM) system centralizes all vendor information, contracts, communications, and performance metrics into a single, accessible platform. This technology creates a single source of truth, enabling proactive risk management, streamlined collaboration, and data-driven strategic decision-making. VRM systems are a cornerstone of modern vendor management best practices.
This practice is essential for scaling IT vendor operations efficiently. For example, large enterprises leverage platforms like SAP Ariba or Coupa to unify their procurement processes, manage contracts, and gain real-time visibility into their IT supply chain, from software licensing to hardware sourcing and service delivery. These systems help consolidate vendor data, automate workflows (like invoice processing or performance reporting), and analyze spending patterns, turning administrative tasks into strategic opportunities. Adopting a VRM system transforms IT vendor management from a reactive function into a proactive, value-adding part of the business, supporting broader enterprise architecture goals (e.g., those found in TOGAF).
How to Implement a VRM System Effectively
A successful VRM implementation requires a strategic rollout plan that aligns technology with business processes and user needs. Involving vendors and internal stakeholders (especially IT and procurement) early is key to ensuring adoption and maximizing the return on investment.
- Integrate with Existing Systems: Ensure the VRM can seamlessly connect with your current ERP, CRM, IT Service Management (ITSM) platforms, and financial software to create a unified data ecosystem and avoid manual data entry. This is critical for data accuracy and efficiency.
- Prioritize Data Quality: Establish clear data validation rules and processes from the outset. High-quality data—including up-to-date contact information, contract terms, and performance scores—is the foundation for reliable reporting and analytics, crucial for strategic decision-making.
- Provide Comprehensive Training: Develop a thorough training program for all internal users (procurement, IT operations, legal) and key vendor contacts. This ensures everyone understands how to use the system effectively and consistently, fostering better communication and collaboration.
By methodically implementing a VRM system, you build a scalable framework that enhances visibility, improves efficiency, and strengthens strategic partnerships across your IT vendor ecosystem.
5. Strategic Vendor Segmentation and Tiering
Not all vendors hold the same level of importance to your business, and therefore, they shouldn't all be managed in the same way. Strategic vendor segmentation is the practice of classifying suppliers into distinct tiers based on their business impact, level of spend, associated risk, and innovation potential. This allows IT organizations to allocate management resources more effectively, focusing intense oversight on critical partners while streamlining interactions with transactional suppliers. This tailored approach is a cornerstone of advanced vendor management best practices, maximizing value and minimizing risk.
This practice is crucial because a one-size-fits-all management strategy is inefficient and risky, especially given the diverse nature of IT vendors. For example, a global technology firm might classify its primary cloud infrastructure provider (e.g., AWS, Azure, Google Cloud) as a Tier 1 strategic partner, engaging in joint innovation, deep technical integration, and executive-level reviews. In contrast, its office supply vendor or a generic software license provider might be a Tier 3 transactional supplier, managed primarily for cost efficiency and reliability. Similarly, a financial institution would tier its cybersecurity software vendors and data center providers as highly critical, applying the most rigorous due diligence and continuous monitoring.
How to Implement Vendor Segmentation
To apply this effectively, you must develop a clear, objective framework with input from key business units like procurement, finance, IT, and operations. This ensures the classification reflects true business value and strategic importance.
- Define Clear Segmentation Criteria: Establish transparent criteria for each tier. Factors should include annual spend, business impact if the service is disrupted (e.g., system downtime, data breach), innovation potential, and risk level (e.g., data security, regulatory compliance). For IT, criticality to core business functions and the level of data access are paramount.
- Develop Tier-Specific Engagement Models: Create distinct management playbooks for each tier. Strategic partners may require executive-level quarterly reviews, joint roadmaps, and dedicated account managers. Transactional vendors, on the other hand, might only need automated performance tracking and annual contract renewals.
- Review and Adjust Periodically: Vendor importance can change over time due to new projects, market shifts, or technological advancements. Re-evaluate your segmentation annually or after significant business events (e.g., a major digital transformation initiative) to ensure your classifications and resource allocation remain aligned with strategic IT priorities.
Reflection Prompt:
- Think about your current IT vendors. Which ones would you classify as strategic, and which as transactional? How would a tiered approach change your engagement with them?
By systematically segmenting your vendors, you transform your management efforts from a reactive, uniform process into a proactive, strategic function that optimizes resource allocation and strengthens critical IT relationships. Learn more about aligning vendor capabilities with business goals in our article on how to use skills mapping.
6. Risk Management and Business Continuity Planning
Effective vendor management is not just about onboarding and performance; it's about anticipating and mitigating potential disruptions, particularly in the ever-evolving threat landscape of IT. This practice involves proactively identifying, assessing, and neutralizing vendor-related risks, from supply chain failures and sophisticated cybersecurity threats to financial instability or geopolitical impacts. A robust vendor management strategy must include a comprehensive approach to managing the risks introduced by external partners, often referred to as third-party risk management. This ensures organizational resilience and the continuity of critical business operations.
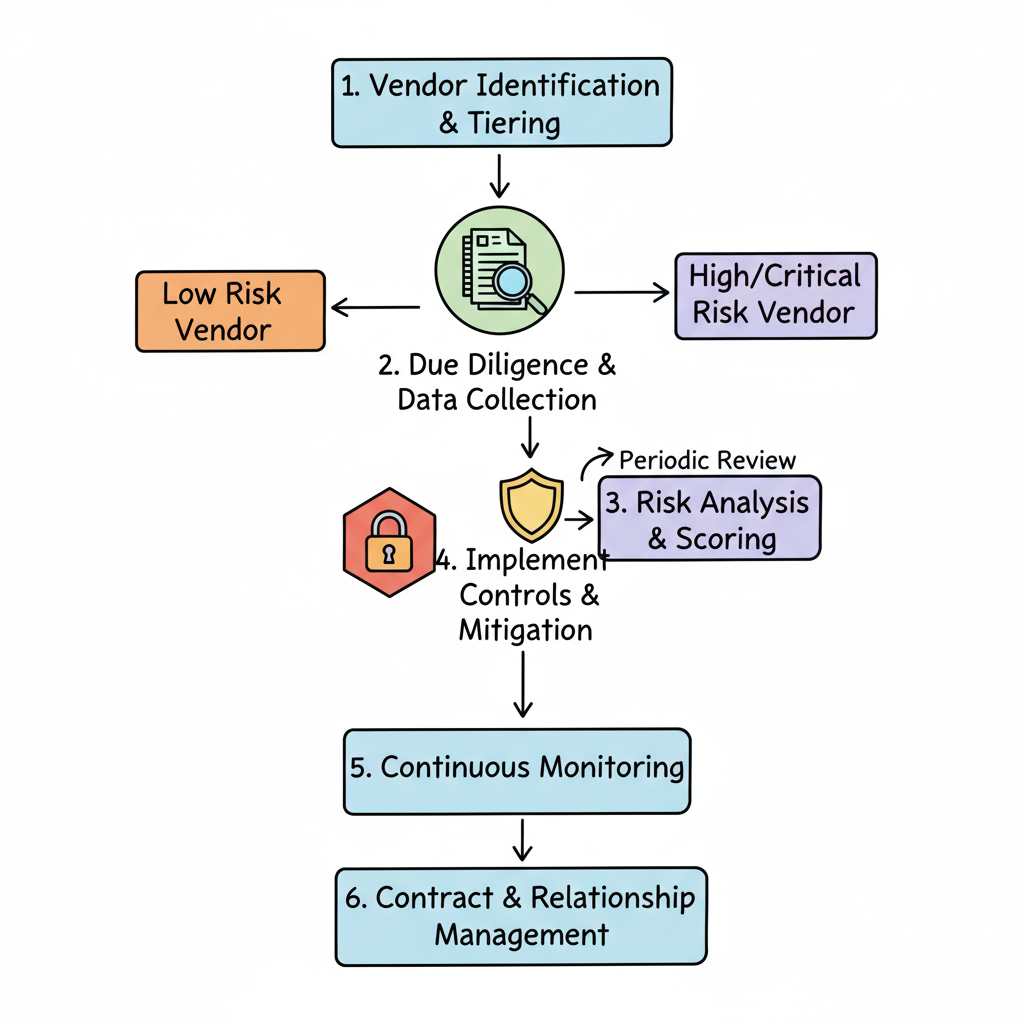
This best practice is crucial because a single point of failure within your IT supply chain can halt your entire operation or expose sensitive data. For instance, the SolarWinds supply chain attack highlighted the fragility of software supply chains, emphasizing the need for rigorous security assessments of all third-party software and service providers. Similarly, organizations relying on international suppliers for hardware or managed services must conduct ongoing geopolitical risk assessments. Cybersecurity assessments for any tech vendor with access to your systems or data are non-negotiable for protecting sensitive data and maintaining compliance with regulations like GDPR, HIPAA, or PCI DSS—skills central to certifications like CompTIA Security+, CISSP, and CISM. Failing to plan for these contingencies exposes your organization to severe operational, financial, and reputational damage.
How to Implement Proactive Risk Mitigation
To build a resilient IT vendor ecosystem, you must integrate risk assessment into every stage of the vendor lifecycle. This requires a dynamic and forward-thinking approach that goes beyond initial due diligence.
- Develop Vendor Risk Heat Maps: Categorize IT vendors based on their criticality to business operations and the potential impact (likelihood and severity) of their failure or compromise. This visual tool helps prioritize monitoring efforts on high-risk, high-impact partners, focusing security and audit resources where they are most needed.
- Establish Supplier Concentration Limits: Avoid over-reliance on a single vendor for critical IT goods or services (e.g., a sole cloud provider, a single software vendor for mission-critical applications). Set clear policies to diversify your supply base and build redundancy into your operations and architecture where feasible.
- Create Contingency and Exit Plans: For each critical IT supplier, develop a detailed contingency plan outlining immediate actions in case of disruption (e.g., a data breach, service outage, or vendor bankruptcy). This should include identifying alternative suppliers, defining data portability strategies, and outlining a clear exit strategy to minimize service interruption.
Certification Connection:
- Candidates for PMP will recognize the importance of comprehensive risk identification and response planning in project procurement, while CISSP and CISM certifications deeply cover third-party risk management and supply chain security.
By embedding robust risk management into your vendor processes, you transform potential IT crises into manageable events, protecting your organization's digital assets and operational continuity. To better understand the steps involved, review this comprehensive guide on what is the risk management process.
7. Cost Management and Spend Optimization
Effective vendor management extends beyond service delivery and into strategic financial oversight, particularly crucial for managing IT budgets. Cost management and spend optimization is a continuous process of analyzing and controlling vendor-related expenditures to maximize value. This practice is not simply about chasing the lowest price; it's a sophisticated approach that balances cost, quality, and risk to ensure every dollar spent contributes to strategic business objectives. This is a critical component of vendor management best practices, as it directly impacts profitability, operational efficiency, and the ability to fund new IT initiatives.
This practice is fundamental because unmanaged vendor spend can lead to significant budget overruns, resource waste, and missed opportunities for savings. For instance, in cloud environments (like AWS or Azure), proactive cost optimization involves monitoring resource utilization, identifying idle or over-provisioned instances, and leveraging reserved instances or spot instances to reduce expenditure without compromising performance. Similarly, consolidating software licenses with fewer vendors, or negotiating multi-year contracts based on projected growth, can yield substantial savings. A disciplined approach to spend ensures IT financial resources are used effectively, a key skill for IT managers and project leads (PMP certification relevant).
How to Implement Spend Optimization
To execute this effectively, your organization must adopt a proactive and analytical approach to procurement and vendor costs. This requires collaboration between procurement, finance, and operational IT teams to identify and act on savings opportunities.
- Focus on Total Cost of Ownership (TCO): Look beyond the initial purchase price of IT hardware, software, or services. Analyze the entire lifecycle cost, including implementation, ongoing maintenance, support, energy consumption, security overheads, and eventual decommissioning, to understand the true financial impact of a vendor partnership.
- Leverage Benchmarking and Negotiation: Regularly benchmark your IT vendor pricing against market rates, competitor offerings, and industry standards to ensure competitiveness. Use this data to enter negotiations with a clear understanding of fair value and to drive cost-effective agreements for new contracts or renewals.
- Consolidate and Streamline: Where possible, consolidate spend with fewer, high-performing strategic partners. This not only improves your negotiating power (leading to better volume discounts) but also simplifies management, reduces administrative overhead, and can lead to more integrated technical solutions.
Key Takeaway:
- Spend optimization in IT is not just about cutting costs; it's about strategic investment, ensuring every dollar spent delivers maximum value and supports future growth.
By embedding cost optimization into your vendor management framework, you transform IT procurement from a cost center into a strategic value driver, freeing up resources for innovation.
8. Vendor Collaboration and Partnership Development
Moving beyond purely transactional interactions, the most advanced vendor management best practices focus on building true strategic partnerships, especially critical for complex IT projects and digital transformation. This approach involves cultivating collaborative relationships with key vendors based on shared goals, joint planning, and mutual benefit. It transforms the vendor from a mere service provider into an integrated partner invested in your organization's success, fostering innovation and driving long-term value. This is a crucial step in maturing your vendor management capabilities.
This practice is essential for unlocking strategic advantages that a simple buyer-supplier dynamic cannot achieve. For instance, deep collaboration with a key software development vendor can lead to co-creation of unique features, giving your product a competitive edge. Similarly, partnering closely with a cloud provider's expert teams can help optimize architecture, accelerate migrations, and leverage cutting-edge services. This mirrors successful models like the Toyota Production System, where suppliers are integral to product design and continuous improvement processes, resulting in higher quality and efficiency. In IT, this collaborative approach creates a resilient, innovative, and rapidly evolving supply chain.
How to Foster Strategic Partnerships
Developing a partnership requires a deliberate shift in mindset and process, focusing on transparency and shared objectives. It’s about building trust and creating a framework where both parties can thrive together.
- Establish Joint Governance: Create joint steering committees or working groups with key IT vendors to regularly review performance, plan future initiatives (e.g., new technology adoption, platform upgrades), and resolve issues collaboratively. This ensures strategic alignment at the leadership and operational levels.
- Share Information Transparently: Provide strategic IT vendors with access to relevant data, such as demand forecasts, product roadmaps, technical specifications, and strategic business objectives. This allows them to plan more effectively, align their own development with your needs, and proactively offer solutions.
- Involve Vendors in Early-Stage Development: Integrate key suppliers into your product design, architecture planning, and development processes. Their specialized expertise can lead to more innovative, cost-effective, and robust solutions from the outset, reducing rework and accelerating time-to-market.
Reflection Prompt:
- Can you identify an IT vendor that, if treated as a strategic partner, could help drive significant innovation or efficiency in your organization? What would that partnership look like?
By investing in these partnerships, you build a powerful ecosystem that drives mutual growth and innovation, turning your IT supply chain into a significant competitive advantage. For more on creating these synergistic relationships, consider exploring resources on strategic alliance management.
9. Compliance, Ethics, and Sustainability Management
Modern vendor management extends beyond operational performance to encompass a vendor's ethical, legal, and social footprint. This practice involves rigorously assessing and monitoring vendor adherence to regulatory requirements, ethical standards, and sustainability criteria. It’s about ensuring your IT supply chain not only performs well but also acts responsibly. This comprehensive oversight protects your organization from legal penalties, reputational damage, and supply chain disruptions linked to non-compliance or unethical behavior. This is particularly critical for IT professionals who manage vendors handling sensitive data or operating in regulated industries.
This proactive approach is essential because a vendor's missteps can directly impact your brand and bottom line. For instance, a cloud service provider's failure to comply with data residency laws (like GDPR for European data) could lead to massive fines and loss of customer trust. Similarly, an IT hardware manufacturer found to be using unethical labor practices could spark public backlash, damaging your brand by association. Integrating these standards is a critical component of modern vendor management best practices, aligning IT procurement with corporate responsibility and skills emphasized in certifications like CISM and CISSP.
How to Implement Comprehensive Compliance Management
Effective implementation requires embedding these standards directly into your vendor lifecycle, from selection to offboarding. This creates a culture of accountability throughout your supply chain and requires collaboration between procurement, legal, IT security, and corporate social responsibility teams.
- Develop a Clear Vendor Code of Conduct: Establish a formal document outlining your non-negotiable standards for labor, ethics, environmental impact, data privacy, and legal compliance. Make acceptance of this code a prerequisite for partnership and integrate it into all contracts.
- Conduct Regular Compliance Audits: Don't just take a vendor's word for it. Perform scheduled and unscheduled audits, leveraging both internal teams (e.g., your security or compliance department) and objective third-party auditors (e.g., for SOC 2 or ISO 27001 assessments) to verify compliance on the ground.
- Integrate Compliance into Vendor Scorecards: Make adherence to ethical, security, and sustainability standards a weighted criterion in your vendor performance reviews. This ensures that compliance is treated with the same importance as cost and quality, driving continuous improvement in these critical areas.
Key Takeaway:
- In IT, a vendor's compliance with data protection laws (like GDPR, HIPAA) and cybersecurity standards is as critical as their technical performance. Non-compliance is a business continuity risk.
By proactively managing vendor compliance, ethics, and sustainability, you not only protect your organization but also contribute to a more responsible and resilient global IT ecosystem.
10. Communication and Escalation Protocols
Establishing clear communication and escalation protocols is essential for a healthy and efficient vendor relationship, especially in fast-paced IT environments. This practice involves creating structured channels, defining meeting cadences, and outlining a formal process for resolving issues when they arise. It moves beyond ad-hoc emails and phone calls to a systematic approach that ensures alignment, promotes transparency, and prevents minor problems from escalating into major crises. This is a foundational element for effective ITIL service operation and PMP communication management.
This systematic communication is a core component of effective vendor management best practices because it builds a foundation of trust and accountability. For instance, a software development firm might implement daily stand-ups with its offshore development team to track progress and identify blockers, while holding monthly business reviews with executive sponsors to discuss strategic alignment and budget. In IT service management, a retailer might have weekly operational calls with its MSP to review performance metrics and a clear escalation path to a regional manager if service-level agreements are breached, ensuring rapid response to critical incidents.
How to Implement Clear Protocols
To execute this effectively, you must define and document the rules of engagement before issues occur. This ensures both parties understand how to communicate and what to do when standard channels are not sufficient.
- Define Communication Cadences: Establish a schedule for regular interactions based on the vendor's role and criticality. This could include daily operational check-ins for critical support vendors, weekly performance reviews for project-based teams, and quarterly strategic meetings for key technology partners.
- Create an Escalation Matrix: Develop a clear, tiered escalation matrix that details who to contact for specific issues (e.g., technical support, billing, contract disputes), response time expectations for each tier, and the triggers for moving a problem up the chain of command (e.g., unresolved issue after 24 hours, impact on critical business function).
- Use a Centralized System: Document all significant communications, decisions, and action items in a centralized platform or system of record (e.g., a VRM system, project management tool, or ITSM platform). This creates a transparent audit trail, ensures all stakeholders have access to the same information, and prevents knowledge loss.
Certification Connection:
- For PMP certification holders, this practice directly applies to "Plan Communications Management" and "Manage Communications" processes, emphasizing structured, effective information flow with all stakeholders, including vendors.
By formalizing your communication framework, you create a predictable and efficient environment, enabling quick problem resolution and strengthening the partnership. For a deeper look at managing these interactions, explore our insights on how to build a strong supplier relationship.
Vendor Management: Top 10 Practices Comparison
| Item | Implementation complexity | Resource requirements | Expected outcomes | Ideal use cases | Key advantages |
|---|---|---|---|---|---|
| Vendor Selection and Due Diligence | Medium–High — comprehensive, time‑intensive | Cross‑functional teams, financial & compliance checks, site visits | Reliable vendor fit; lower onboarding risk | Selecting new/critical suppliers (e.g., cloud providers); regulated sectors (e.g., healthcare IT) | Reduces failure & compliance risk; ensures quality & security |
| Establishing Clear Contracts and SLAs | Medium — legal drafting and negotiation | Legal counsel, procurement, stakeholder time | Clear expectations; enforceable remedies | IT outsourcing, SaaS agreements, long‑term engagements | Legal protection; measurable performance standards for IT services |
| Vendor Performance Management and Monitoring | Medium — ongoing processes, data collection | Monitoring tools, analysts, regular reviews | Early issue detection; continuous improvement | High‑volume IT operations; mission‑critical services; cloud cost optimization | Data‑driven accountability; performance improvement in IT delivery |
| Implementing Vendor Relationship Management (VRM) Systems | High — technical implementation & change mgmt | Software licenses, IT integration, training | Centralized vendor data; faster decisions | Enterprises with many IT vendors or global procurement; complex IT ecosystems | Improved visibility; reduced admin; audit trails for IT spend |
| Strategic Vendor Segmentation and Tiering | Low–Medium — policy design and classification | Spend/risk analysis, stakeholder alignment | Focused resource allocation; prioritized management | Large IT supplier portfolios; strategic cloud sourcing | Targets resources to high‑impact IT vendors; efficiency |
| Risk Management and Business Continuity Planning | Medium–High — continuous assessment & planning | Risk tools, monitoring, contingency resources | Increased resilience; reduced disruption impact | Critical IT supply chains; cybersecurity/geopolitical risk areas (e.g., data breaches) | Prevents IT disruptions; enables rapid response to incidents |
| Cost Management and Spend Optimization | Medium — analytical and negotiation effort | Spend analytics, benchmarking, category managers | Lower total cost; better value delivery | High‑spend IT categories (e.g., cloud, software licenses); budget pressure situations | Reduces IT costs while preserving value; better forecasting |
| Vendor Collaboration and Partnership Development | Medium — relationship building and governance | Time for joint planning, executive involvement | Innovation, improved performance, loyalty | Strategic IT suppliers, product development partnerships, R&D vendors | Drives IT innovation; strengthens supplier commitment |
| Compliance, Ethics, and Sustainability Management | Medium — audits and standards enforcement | Audit programs, third‑party verifiers, training | Reduced legal/reputational risk; ESG alignment | Consumer brands, regulated industries (e.g., HIPAA, GDPR compliance in IT), global sourcing | Protects reputation; meets regulatory/ESG expectations for IT services |
| Communication and Escalation Protocols | Low–Medium — design and governance | Defined contacts, meeting cadences, documentation | Faster issue resolution; clearer accountability | Operational IT partnerships; crisis scenarios (e.g., service outages) | Prevents misunderstandings; speeds problem resolution |
Integrating Best Practices for a Future-Proof Vendor Ecosystem
Navigating the complexities of modern business demands more than just transactional relationships with suppliers—especially in the dynamic world of IT. As we've explored, a truly effective vendor management strategy is a dynamic, multi-faceted discipline. It’s about building a resilient ecosystem where your organization and its partners thrive together, creating mutual value that far exceeds the sum of individual contracts. The ten vendor management best practices detailed in this guide are not isolated tactics; they are interconnected pillars that support a cohesive and strategic framework for IT professionals.
From the foundational rigor of Vendor Selection and Due Diligence (critical for IT security and compliance) to the forward-thinking approach of Vendor Collaboration and Partnership Development (driving innovation), each practice builds upon the others. Strong contracts and clear SLAs are meaningless without consistent performance monitoring. Likewise, strategic segmentation is only effective when supported by robust risk management and clear communication protocols. Adopting these principles transforms vendor management from a reactive, administrative burden into a proactive, strategic advantage that directly impacts your IT budget, innovation capacity, and market reputation.
Shifting from Management to Strategic Partnership
The ultimate goal for IT professionals is to evolve beyond simple oversight. True mastery lies in fostering genuine partnerships where vendors are not just suppliers, but integral extensions of your team. This requires a cultural shift, supported by the right tools and processes. Implementing a dedicated Vendor Relationship Management (VRM) system and establishing clear escalation paths are crucial steps that empower this evolution. When you view your IT vendors as strategic allies, you unlock new opportunities for innovation, gain early access to new technologies, and build a supply chain that is resilient enough to withstand market volatility and cyber threats.
This strategic alignment is where the real value is created. It's the difference between merely managing IT costs and actively optimizing spend for long-term growth. It's the transition from enforcing compliance to co-creating sustainable and ethical business practices, ensuring your IT operations are both efficient and responsible.
Your Actionable Path Forward
Embarking on this journey can feel daunting, but progress begins with a single, focused step. Don't attempt to overhaul your entire system overnight. Instead, use these best practices as a diagnostic tool for your organization's IT vendor management.
- Conduct a Self-Assessment: Review your current vendor processes against the ten practices outlined. Where are your most significant gaps? Are your SLAs outdated for cloud services? Is your IT vendor risk assessment process informal or undocumented?
- Prioritize High-Impact Areas: Identify one or two practices that will deliver the most immediate value to your organization. For many IT teams, this might be formalizing performance reviews for key software vendors or implementing a tiered segmentation strategy to focus resources on critical technology partners.
- Create a Phased Rollout Plan: Develop a realistic timeline for implementing changes. Start with a pilot group of vendors or a specific IT project to test and refine your new processes before a company-wide deployment. This iterative approach ensures buy-in and minimizes disruption.
By systematically integrating these vendor management best practices, you create a cycle of continuous improvement. You build a vendor ecosystem that is not only efficient and cost-effective but also agile, innovative, and prepared for the future of IT. This strategic capability is a powerful competitive differentiator and a critical skill set for any professional in the technology and business operations space, enhancing your value in the job market and your pursuit of relevant certifications.
Ready to transform your theoretical knowledge into a recognized professional credential? The expert-led courses at MindMesh Academy provide in-depth training and certification preparation covering the strategic frameworks discussed here, equipping you to lead and optimize your organization's vendor relationships. Elevate your career by visiting MindMesh Academy to explore our comprehensive vendor management curriculum.

Written by
Alvin Varughese
Founder, MindMesh Academy
Alvin Varughese is the founder of MindMesh Academy and holds 15 professional certifications including AWS Solutions Architect Professional, Azure DevOps Engineer Expert, and ITIL 4. He's held senior engineering and architecture roles at Humana (Fortune 50) and GE Appliances. He built MindMesh Academy to share the study methods and first-principles approach that helped him pass each exam.