Your Cyber Security Cert Roadmap for Career Success
For IT professionals aiming to excel in the dynamic world of cybersecurity, a certification roadmap isn't merely a checklist of desired credentials. Instead, envision it as your definitive career blueprint—a meticulously planned strategy for acquiring the certifications essential to navigate your journey from an entry-level position to a highly specialized, senior leadership role. This purpose-driven path ensures every certification you pursue represents a deliberate, skill-building stride forward, consistently leveraging and expanding upon your existing expertise.
Charting Your Course in a High-Demand Field
Embarking on a cybersecurity career path, or even pivoting into it, can initially feel overwhelming. The sheer volume of available certifications—from foundational network security to advanced cloud forensics—can make choosing the right ones a daunting task. Without a strategic plan, IT professionals risk investing valuable time and resources into credentials that don't align with their long-term career aspirations. This is precisely where a meticulously crafted cybersecurity certification roadmap transitions from a helpful guide to an indispensable strategic asset. It shifts your approach from simply collecting badges to proactively and intentionally engineering your career trajectory.
Consider your roadmap as your unerring compass in this complex domain. It provides clear direction, whether your ultimate goal is to become a penetration tester, a cloud security engineer specializing in AWS or Azure, or a governance, risk, and compliance (GRC) analyst. With this robust plan in place, every exam successfully passed and every new skill acquired becomes a direct, impactful maneuver toward your target role, enabling you to make intelligent, strategic decisions from the outset of your journey.
Why a Roadmap Is Non-Negotiable
The demand for skilled cybersecurity professionals continues to escalate dramatically. The International Information System Security Certification Consortium (ISC)² recently highlighted a staggering global shortage of 3.4 million cybersecurity workers. For IT professionals, this substantial gap signifies immense career opportunities, yet it also underscores the intense competition for those highly coveted, top-tier roles. Simply put, proving your expertise is more critical than ever.
Furthermore, the same study revealed that an overwhelming 86% of security professionals regard certifications as pivotal for validating skills and serving as a crucial differentiator in a competitive job market. A well-defined roadmap ensures your study efforts are not just diligent, but strategically targeted. For instance, investing in an advanced digital forensics certification would be a misstep if your true ambition is to become a cloud security architect specializing in, say, AWS or GCP. A strategic plan acts as your navigation system, connecting the dots between your current skills, desired roles, and the most relevant certifications.
Reflection Point: Pause and consider your ideal cybersecurity role in the next 3-5 years. Does your current learning path and certification plan directly align with the specific skills and credentials required for that particular role? A roadmap helps solidify this alignment.
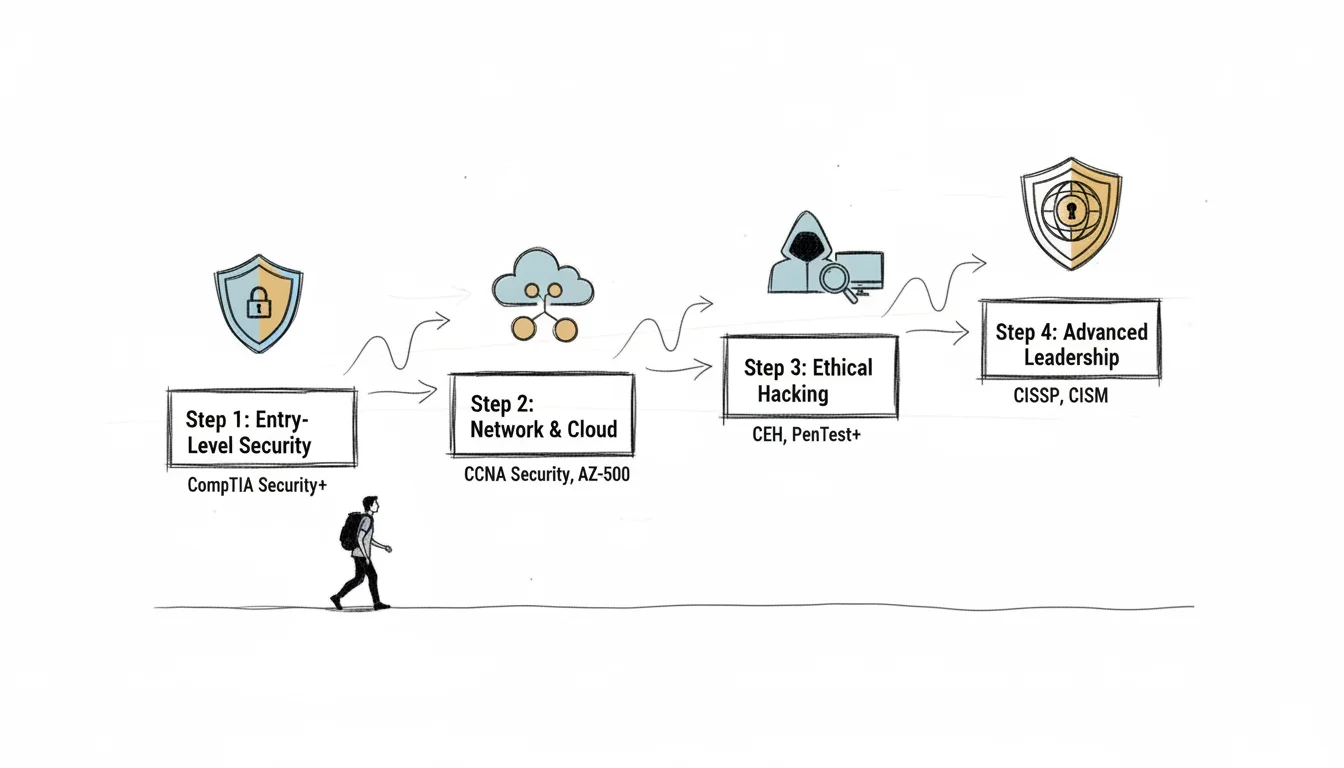
This accompanying visual succinctly illustrates the powerful, logical progression facilitated by a roadmap: clearly define your career aspirations, identify and pursue the certifications that cultivate the requisite skills, and ultimately secure the cybersecurity position you desire.

In essence, this process demonstrates how a thoughtfully constructed cyber security cert roadmap functions as an invaluable bridge, transforming your long-term professional ambitions into a tangible, actionable, and successful career trajectory.
To provide IT professionals with a clearer understanding of the progression and specialization within the certification landscape, here’s a concise overview of the distinct tiers you'll typically encounter.
Cybersecurity Certification Tiers at a Glance
| Certification Tier | Focus Area | Typical Experience Level | Example Certifications |
|---|---|---|---|
| Foundational | Core IT and security principles, networking, basic threat identification. | 0-1 years | CompTIA A+, Network+, Security+ |
| Intermediate | Vendor-specific skills, deeper security analysis, specialized domains. | 1-3 years | CySA+, PenTest+, CCNA |
| Advanced | In-depth expertise, security management, architecture, policy. | 3-5+ years | CISSP, CISM, CASP+ |
| Expert / Specialist | Highly specialized skills in niche areas like forensics or offensive security. | 5-10+ years | OSCP, GIAC, CISSP Concentrations |
This table visually maps the typical progression of cyber security certifications, making it easier to conceptualize how each level systematically builds upon the last, directly aligning with various stages of an IT professional's cybersecurity career development.
The Business Perspective on Certification
Understanding the profound value companies place on these credentials is equally crucial for your strategic planning. Recognizing the imperative of effective cyber security in today's business landscape allows IT professionals to view certifications from a hiring manager's perspective. Employers aren't simply seeking theoretical knowledge; they're actively looking for demonstrable proof of a candidate's commitment and capability to defend against complex, real-world threats.
A strategically placed certification on your resume serves as an immediate signal to hiring managers, confirming a verified baseline of industry-recognized knowledge and practical skills. This not only significantly de-risks the hiring process for organizations but also dramatically increases the likelihood of your application successfully navigating automated Applicant Tracking Systems (ATS) that are programmed to filter for essential keywords such as "Security+" or "CISSP."
It’s worth noting that this level of strategic planning isn't exclusive to cybersecurity; most successful IT careers across domains like project management (PMP) or IT service management (ITIL) are built upon similar foundational principles of targeted learning. If you're currently navigating the initial stages of your tech journey, our comprehensive guide on how to start an IT career offers broader principles equally relevant to establishing your cybersecurity path. Ultimately, your personalized cybersecurity certification roadmap is your indispensable blueprint for achieving sustained career success.
Building Your Foundation with Core Certifications
Just as a resilient skyscraper requires an unyielding foundation, a robust cybersecurity career demands mastery of fundamental principles. This initial phase of your cybersecurity certification roadmap is dedicated to unequivocally demonstrating you possess the core, non-negotiable knowledge baseline essential for every security professional. Consider it the bedrock upon which all subsequent specialized skills and advanced expertise will be securely constructed.
Certifications such as the CompTIA Security+ are universally recognized as the gold standard for IT professionals entering the cybersecurity domain. Their vendor-neutral nature ensures that the foundational skills acquired are not confined to a single company’s product ecosystem, providing broad applicability across diverse environments. This universal utility is profoundly significant—underscoring why a staggering 82% of DoD 8570 jobs explicitly mandate a certification requirement, with Security+ frequently specified by name.
Possessing this credential is akin to speaking the lingua franca of information security. It immediately communicates to hiring managers that you have a comprehensive grasp of essential principles, signaling readiness for real-world application. For a significant number of aspiring professionals, the CompTIA Security+ acts as the crucial key, unlocking the door to their inaugural security-focused interview and substantive career opportunities.
What Foundational Certs Actually Teach You
It’s imperative not to misunderstand these foundational certifications as mere vocabulary exercises. They are meticulously designed to validate that you possess the practical, hands-on skills and applied knowledge directly relevant to day-one job responsibilities. Consider this your essential basic training for navigating and securing the digital front lines.
The curriculum for these foundational certifications, particularly for a CompTIA Security+ exam, is rigorously framed around real-world scenarios. You won't merely memorize the theoretical definition of a firewall; you'll gain the understanding to actually implement firewall rules effectively to mitigate suspicious traffic, or configure secure access controls. This emphasis on practical application is precisely what makes these credentials so highly valued by employers seeking job-ready talent.
A certification like Security+ rigorously validates critical skill sets, including:
- Threats, Attacks, and Vulnerabilities: You'll develop the acumen to differentiate various malware types, recognize sophisticated social engineering ploys, and comprehend prevalent application-layer attacks.
- Network Security Operations: This domain encompasses securing network devices and data traffic, configuring robust access control lists (ACLs), and meticulously analyzing network logs to detect anomalies.
- Identity and Access Management (IAM): Focuses on implementing precise controls to ensure only authorized individuals and processes can access sensitive data and critical systems.
- Cryptography Basics: You'll master the fundamentals of encryption, hashing algorithms, and Public Key Infrastructure (PKI) to safeguard data both at rest on servers and in transit across networks.
A fundamental component of building a solid cybersecurity foundation involves understanding how to identify and remediate common network security vulnerabilities. These foundational certifications provide the essential framework to recognize such weak points and effectively deploy appropriate safeguards.
Proven Study Strategies for Success
Confronting your initial major certification exam, such as the CompTIA Security+, can undoubtedly feel intimidating. However, remember that countless IT professionals have successfully navigated this path before you. A common pitfall observed is the tendency to solely rely on passively reading a textbook from cover to cover—a method rarely yielding optimal results. Successful candidates almost universally employ a synergistic mix of diverse study strategies.
Initiate your preparation by integrating various learning modalities. A high-quality video course can demystify complex concepts, while a robust study guide effectively reinforces retention. Crucially, hands-on practice labs are non-negotiable. There is absolutely no substitute for actively configuring a virtual firewall, analyzing a packet capture using Wireshark, or hardening a simulated operating system environment yourself. This practical engagement solidifies theoretical knowledge into tangible skill.
A significant exam pitfall to avoid is overcomplicating performance-based questions (PBQs). Your strategy should be relentless practice. These questions are not designed as memory recall tests; rather, they are interactive simulations intended to assess your practical ability to perform critical tasks. Cultivate proficiency in command-line interfaces (CLIs) and confidently navigate typical security tool dashboards well in advance of your exam date.
Implementing a structured study plan is paramount. Dedicate specific, non-negotiable blocks of time each day or week, treating them as critical professional appointments. Leverage high-quality practice exams to precisely pinpoint your weaker knowledge areas, then intensively focus your efforts on mastering those topics. This targeted, iterative approach is far more efficient and effective than attempting to absorb or relearn the entire curriculum simultaneously.
Highlighting Foundational Certs on Your Resume
Upon successfully passing your certification exam, the next crucial step is to strategically leverage this new credential for career advancement. Avoid simply listing it obscurely at the bottom of your resume. Especially for IT professionals with limited prior experience, position your certification prominently as the centerpiece of your professional narrative—ideally within your resume's summary, highlights, or a dedicated 'Certifications' section placed near the top.
For example, a compelling resume summary might articulate your value proposition as follows:
- "CompTIA Security+ certified professional demonstrating a robust understanding of threat management, secure network operations, and proactive risk mitigation strategies. Eager to transition foundational knowledge into impactful contributions within a hands-on security analyst role."
This concise statement immediately signals to recruiters a verified, industry-aligned skill set. Furthermore, it significantly enhances your resume's ability to clear automated Applicant Tracking Systems (ATS), which are often configured to filter for these precise keywords. You transcend being merely 'another candidate'; you emerge as a certified candidate—a distinction that confers a tangible competitive advantage in the job market.
These initial credentials represent a pivotal step in your professional journey. For a deeper exploration of other excellent starting points, we invite you to consult our comprehensive guide on the top 5 entry-level IT certifications to launch your career. This resource contextualizes these certifications within the broader IT landscape, empowering you to make the most informed decision for your foundational career move with MindMesh Academy.
Advancing Your Career With Specialized Certs
Having successfully acquired foundational certifications, the next strategic phase in your cybersecurity cert roadmap involves deep specialization. This pivotal juncture marks a clear transition from accumulating general knowledge to rigorously honing a distinct, highly marketable expertise. It's at this stage that IT professionals can substantially elevate their professional value and earning potential.
To draw an analogy: your foundational certification acts like a general contractor's license, demonstrating your understanding of how a complex structure is built. Now, the decision arises: will you pursue mastery as a master electrician, a specialized network architect, or a structural engineer focused on cloud infrastructure? Each of these specialized trajectories necessitates a profoundly different skillset and is validated by specific, advanced certifications.

This is a critical career juncture, demanding careful deliberation. It's not about indiscriminately acquiring the next impressive-sounding credential, but rather about making a strategic, informed choice—selecting the precise certification that will definitively unlock the door to your desired specialized role.
Blue Team Versus Red Team Paths
A classic and pivotal crossroads for any aspiring cybersecurity professional involves selecting between defensive (blue team) and offensive (red team) specializations. The strategic choice made here will largely dictate your subsequent certification pursuits and career trajectory.
If your passion lies in proactive defense, meticulous threat hunting, and serving as the primary deterrent against malicious actors, then the CompTIA Cybersecurity Analyst (CySA+) presents an excellent and logical next step. This certification focuses on leveraging analytics and threat intelligence to actively monitor, detect, and protect network infrastructures, making it an ideal credential for those aspiring to roles such as SOC Analyst or Threat Intelligence Analyst.
Conversely, if you're invigorated by adopting an adversarial mindset to identify and exploit vulnerabilities, the CompTIA PenTest+ certification is likely your calling. This credential is specifically engineered to validate proficiency in advanced penetration testing techniques and comprehensive vulnerability management—skills absolutely central to roles like Penetration Tester, Ethical Hacker, or Vulnerability Analyst.
- Opt for CySA+ if you aspire to: Immerse yourself in security information and event management (SIEM) logs, proactively hunt for emerging threats within enterprise networks, and serve as a frontline incident responder.
- Choose PenTest+ if you are driven to: Ethically compromise systems, meticulously uncover security weaknesses before malicious actors can exploit them, and articulate findings in actionable remediation reports.
Reflection Point: Which team—blue or red—aligns more with your natural problem-solving style and career aspirations? Understanding this fundamental preference is key to charting your specialized path effectively.
Clearly defining this preference early in your journey can prevent considerable expenditure of time and effort on certifications that do not advance you toward your genuine career objectives.
The Rise of Vendor-Specific Cloud Certs
While vendor-neutral certifications, such as those from CompTIA, are invaluable for cultivating core analytical and conceptual security skills, the unprecedented corporate migration to cloud platforms has rendered vendor-specific certifications absolutely non-negotiable. Modern organizations are not merely seeking professionals who 'understand cloud security' in a generic sense; they require proven experts capable of securing their specific cloud infrastructure, whether deployed on AWS, Microsoft Azure, or Google Cloud Platform.
This trend makes your cyber security cert roadmap significantly more personalized and impactful. For instance, if your target organizations heavily leverage Amazon Web Services (AWS), then achieving the AWS Certified Security - Specialty becomes a pivotal differentiator. This credential validates your deep expertise in securing data and workloads within the AWS ecosystem. Correspondingly, the Microsoft Certified: Security Operations Analyst Associate (SC-200) is an indispensable asset for professionals immersed in the Microsoft security landscape.
A targeted vendor-specific certification sends a powerful signal to prospective employers: you possess the specialized knowledge to be immediately effective within their specific cloud or platform environment. This translates directly into reduced onboarding and training overhead for the organization, clearly demonstrating your proactive investment in the exact technologies critical to their operations.
This market-driven trend necessitates precise skill alignment. For IT professionals actively building out their cloud security expertise, our AWS Certified Security - Specialty Study Guide offers a meticulously curated path to confidently acing this high-value examination.
Mapping Certs to High-Demand Roles
The escalating demand for specialized talent represents a significant career opportunity for discerning IT professionals. Companies continue to grapple with protracted hiring timelines for cybersecurity roles; a recent ISACA survey revealed that 39% of organizations require three to six months to fill non-entry-level cyber positions, primarily due to a scarcity of candidates possessing the requisite specialized skills. This talent gap is further exacerbated by retention challenges, with approximately half of surveyed companies acknowledging difficulties in retaining skilled personnel. Comprehensive details on these trends are available in the full State of Cybersecurity 2025 report.
Below is a concise mapping illustrating how specific certifications directly align with some of today's most in-demand intermediate cybersecurity roles:
| Career Goal | Primary Certification Path | Why It's the Right Choice |
|---|---|---|
| Cybersecurity Analyst | CompTIA CySA+ | Focuses on defense, monitoring, and response—the core duties of a SOC analyst. |
| Penetration Tester | CompTIA PenTest+ | Validates offensive security skills and the ability to conduct ethical hacking engagements. |
| Cloud Security Engineer | AWS or Azure Security Cert | Proves expertise in securing the specific cloud platform an organization relies on. |
| Digital Forensics Investigator | GIAC Certified Forensic Analyst (GCFA) | Covers in-depth incident response and forensic analysis of network and system data. |
By strategically targeting certifications explicitly requested by hiring managers in job descriptions, you immediately elevate your candidacy. Your specialized cyber security cert roadmap transcends being merely a list of credentials; it becomes a clear, compelling professional narrative articulating precisely why you are the optimal candidate for the role.
Reaching the Summit with Expert-Level Credentials
Having diligently established a solid foundational skillset and successfully carved out your specialization, you are now poised for the apex of your professional journey: the expert certification tier. This echelon is home to the industry's senior leaders and preeminent technical minds—the Security Architects, Chief Information Security Officers (CISOs), and principal consultants who are instrumental in shaping and executing an entire organization's comprehensive security strategy.
At this advanced level, the focus of certifications significantly shifts away from proficiency in specific tools or granular technical tasks. Instead, the emphasis is on the strategic 'big picture': encompassing security management, robust governance frameworks, comprehensive risk assessment, and holistic security architecture design.
Achieving an expert-level certification represents a profound professional declaration. It unequivocally signals to the broader industry that you possess not only exceptionally deep technical skills but also the indispensable business acumen and strategic leadership mindset required to guide and protect an enterprise. Credentials such as the CISSP, CISM, and CISA stand as the undisputed heavyweights in this elite tier.
CISSP: The Gold Standard for Leaders
If a single certification stands as the universally recognized pinnacle in the cybersecurity industry, it is undeniably the Certified Information Systems Security Professional (CISSP) from (ISC)². For a multitude of senior leadership and technical roles—including Security Architect, Senior Security Engineer, and notably, Chief Information Security Officer (CISO)—the CISSP is regarded as an essential, often prerequisite, credential.
The CISSP examination is notoriously comprehensive, spanning eight critical security domains that extend from enterprise risk management to secure software development practices. However, what truly distinguishes the CISSP is its unique ability to fuse deep technical leadership with executive-level management principles. A CISSP holder is expected to possess the strategic vision and practical acumen to design, engineer, implement, and manage an organization's entire security program holistically.
Crucially, the CISSP is not an exam one can simply 'walk in' to take. Candidates must possess a minimum of five years of cumulative, paid, full-time professional experience across at least two of the eight official CISSP domains. This rigorous experience requirement is precisely why the certification commands such immense respect—it fundamentally guarantees that every individual holding the CISSP has unequivocally proven their strategic and technical capabilities in real-world operational environments.
CISM and CISA: The Management and Audit Powerhouses
While the CISSP remains an undisputed cornerstone for technical leaders, ISACA provides two additional elite-tier certifications specifically tailored to critical, high-level functions: information security management and IT auditing.
-
Certified Information Security Manager (CISM): This certification is meticulously focused on information security management. It was specifically developed for professionals tasked with designing, implementing, and overseeing an enterprise's comprehensive information security program. For those whose career aspirations target roles such as CISO or Director of Information Security, the CISM provides a definitive roadmap. Its curriculum deeply explores security governance, program development, and incident management from a clear, executive leadership perspective.
-
Certified Information Systems Auditor (CISA): This credential is internationally recognized as the global standard for professionals engaged in information systems audit, control, and security. If your career trajectory leans towards IT audit, regulatory compliance, or enterprise risk management, the CISA is an indispensable asset. It conclusively demonstrates your capability to assess system vulnerabilities, conduct thorough compliance reporting, and institute robust control mechanisms within complex organizational structures.
When strategizing this advanced phase of your cyber security cert roadmap, it is highly beneficial to analyze prevailing market demand. A CyberSeek analysis, for instance, indicated that in the U.S., the CISSP was explicitly required in 70,082 job openings. In comparison, the CISA was cited in 45,775 positions, and the CISM in 36,232.
This compelling data offers invaluable insights into industry hiring patterns. While the CISSP often serves as a crucial credential for high-level Department of Defense (DoD) roles, financial services organizations, for example, frequently seek CISA and CISM holders due to their specialized focus on robust information security management and rigorous auditing practices. IT professionals can delve deeper into these trends and strategically align them with their personal career aspirations by exploring comprehensive resources on the top cybersecurity certifications.
Navigating the Experience Requirements
For many aspiring professionals, the most significant hurdle at this expert level is often not the demanding exam itself, but rather the meticulous process of accurately documenting and getting the requisite work experience approved. This process extends far beyond merely submitting a resume; it is a detailed, auditable validation of your professional tenure.
To ensure your experience is successfully validated, a meticulous approach is indispensable. Begin by thoroughly reviewing the official domains for your target certification (e.g., the eight domains for CISSP, the four for CISM). Subsequently, meticulously review your professional work history, carefully mapping specific projects, duties, and accomplishments directly to these defined domains.
Expert Insight: Avoid simply listing job titles and dates. Instead, you must articulate your specific actions and impact using the precise language and terminology of the certification's official domains. For example, rather than stating "Managed firewalls," reframe it as: "Engineered, deployed, and managed enterprise firewall solutions to enforce stringent security policies and meticulously control network traffic, directly aligning with the Security Architecture and Engineering domain." This strategic articulation significantly streamlines the endorsement and review process.
Follow this streamlined process for experience documentation:
- Identify Relevant Roles: Review your professional history and pinpoint roles or projects that directly contribute to meeting the certification's experience criteria.
- Map Duties to Domains: For each identified role, meticulously enumerate the specific responsibilities and tasks you performed. Explicitly connect each one to its corresponding certification domain.
- Quantify Your Impact: Wherever possible, leverage measurable data and metrics. Instead of a generic "Managed a team of five security analysts," a more impactful statement would be: "Led a team of five security analysts, successfully reducing security incidents by 15% year-over-year through proactive threat detection and incident response initiatives."
- Secure an Endorser: For prestigious certifications like the CISSP, a peer who is already certified must endorse your application. Cultivate professional relationships within your network well in advance of your application to identify and secure a suitable endorser.
These top-tier certifications represent the culmination of years of dedicated professional effort and strategic learning. They are profoundly more than merely a passed examination—they serve to definitively validate your profound expertise, unlock unparalleled opportunities at the highest echelons of the profession, and stand as the ultimate capstone to a meticulously planned cybersecurity career.
Keeping Your Certifications and Skills Current

While successfully passing a certification exam might feel like crossing the finish line, in the relentless world of cybersecurity, it is merely the starting gun for an ongoing race. The threat landscape is in perpetual motion, constantly evolving, which means your skills cannot remain static. This inherent dynamism is precisely why virtually every reputable certification program is not a 'one-and-done' achievement; rather, it represents an enduring commitment to continuous professional engagement and mastery.
This isn't simply an informal industry expectation; it's a formalized mandate. Leading certifying bodies such as CompTIA, (ISC)², and ISACA codify this requirement through Continuing Professional Education (CPE) credits (also known as Continuing Education Units or CEUs). Professionals are mandated to accrue a specific number of credits, typically over a three-year cycle, to prevent their hard-earned credentials from expiring. Failing to meet this deadline can necessitate re-sitting the entire examination.
Creative Ways to Earn CPE Credits
Let's be frank: the prospect of passively accumulating hours of webinars purely for compliance can feel uninspiring. The excellent news is that your cyber security cert roadmap should strategically encompass more than just exam success; it ought to integrate proactive methods for earning CPEs that genuinely enhance your professional capabilities and expertise.
The fundamental purpose of CPEs extends beyond merely demonstrating ongoing attentiveness; it unequivocally proves your sustained active engagement and relevance within the dynamic cybersecurity field.
Here are several impactful approaches to earning CPE credits that transcend passive learning:
- Engage at Industry Conferences: Premier events like Black Hat, DEF CON, or even local BSides chapters are invaluable CPE sources. Attending these conferences allows you to learn from industry leaders, discover cutting-edge research, and accrue credits for each educational session.
- Contribute to Open-Source Initiatives: If you utilize a particular security tool hosted on platforms like GitHub, consider contributing to its project. Earning credits through documentation updates, vulnerability hunting, or even code contributions provides an exceptional avenue for hands-on, practical experience.
- Mentor and Educate: Numerous professional organizations, including (ISC)², award CPEs for mentoring activities. Guiding a junior analyst not only fosters their growth but also compels you to rigorously review and articulate your understanding of core cybersecurity concepts, thereby sharpening your own expertise.
- Disseminate Knowledge: Authoring a comprehensive blog post, a detailed white paper, or an article for a reputable security publication is an excellent strategy to earn credits while simultaneously establishing and enhancing your professional reputation within the industry.
A Simple System for Tracking Your Credits
The certification renewal deadline has a notorious tendency to approach rapidly. Receiving an email indicating a deficit of 40 CPEs with only three months remaining can induce a particular kind of professional anxiety. Fortunately, this scenario is entirely preventable. The solution lies in implementing a straightforward, consistent system for tracking your progress.
Avoid sole reliance on the certification body's designated portal. I strongly advise maintaining your personal, independent log, whether in a simple spreadsheet or a dedicated digital or physical notebook.
Implement a clear tracker featuring columns for the date, a concise description of the activity, the CPE type (e.g., "conference," "webinar," "mentoring"), the number of credits earned, and a direct link or path to verifiable proof of completion. Develop the habit of logging each activity immediately upon completion. This minor, 30-second effort will preempt significant future administrative burdens and stress.
A basic tracker might look something like this:
| Date | Activity Description | CPE Type | Credits Earned | Proof of Completion |
|---|---|---|---|---|
| 10/15/2024 | Attended "Cloud Security Summit" | Conference | 8 | link-to-certificate.pdf |
| 11/02/2024 | Published blog post on "Log4j Mitigation" | Writing | 5 | link-to-article.com |
| 11/20/2024 | Completed CompTIA webinar | Training | 1 | link-to-email-confirm.png |
Cultivating this small but disciplined habit transforms the renewal process into a smooth, ongoing management task rather than a stressful, last-minute scramble.
The Real Value of Staying Current
Ultimately, maintaining your cybersecurity certifications extends far beyond merely preserving a valid credential. It powerfully communicates a clear, unambiguous signal to your current leadership, team members, and prospective employers: that you are deeply committed to continuous professional development and mastery of your craft.
In a domain where outdated knowledge can quickly become a significant liability, unequivocally demonstrating your commitment to continuous learning is precisely what distinguishes you as an elite professional. An actively maintained certification is far more than a mere resume entry—it is irrefutable evidence that you are prepared for, and capable of addressing, today’s complex and evolving cybersecurity challenges.
Got Questions About Cybersecurity Certs? We’ve Got Answers.
Navigating the intricate landscape of cybersecurity certifications can often feel akin to traversing a complex maze. As IT professionals meticulously sketch out their own cyber security cert roadmap, a multitude of questions inevitably arise: Which credential offers the optimal starting point? Is a traditional academic degree truly indispensable? What realistic timeframe should one anticipate for achieving certification?
Obtaining clear, authoritative answers is the critical first step toward building genuine momentum. It is all too easy to succumb to 'analysis paralysis' when confronted with an array of seemingly endless options. Let's cut through the informational noise and guide you onto the most effective path forward.
Which Cybersecurity Certification Should I Get First?
For virtually every IT professional embarking on a cybersecurity career, the resounding answer is the CompTIA Security+. Consider this certification the foundational bedrock of your entire professional journey. Its vendor-neutral curriculum ensures that the essential skills acquired are broadly applicable and not confined to proprietary products, thereby furnishing you with a flexible, robust foundation adaptable to any future career trajectory.
The CompTIA Security+ comprehensively covers essential security concepts and is globally acknowledged as the de facto standard for entry-level cybersecurity professionals. It is frequently listed as a baseline requirement for a significant number of government, military (DoD), and corporate positions. Securing this credential on your resume represents one of the most strategically powerful initial career moves you can make.
Do I Need a Degree to Get Into Cybersecurity?
While a traditional college degree can certainly serve as a valuable asset, it is unequivocally not a prerequisite for entry into or success within cybersecurity. I have personally encountered countless top-tier security professionals who forged exceptional careers based largely on targeted certifications and demonstrable real-world experience. Cybersecurity operates as a genuine meritocracy—your proven capabilities and practical contributions frequently resonate far more powerfully than any academic diploma.
Indeed, many discerning hiring managers, especially for hands-on technical roles, often perceive targeted, industry-recognized certifications as possessing greater immediate value than a broad, general academic degree.
A focused certification, such as CompTIA Security+ or CySA+, provides concrete, verifiable proof of your mastery over a specific, job-ready skill set. It effectively communicates to an employer that you possess the immediate capability to 'hit the ground running,' a proposition often far more persuasive than a general four-year degree that may only superficially address the practical applications of cybersecurity.
Bottom line: Do not permit the absence of a traditional degree to impede your ambition in this field.
How Long Does It Take to Get a Certification?
This is indeed the quintessential 'it depends' question. The actual timeline for achieving certification fundamentally hinges on two primary factors: the inherent difficulty and breadth of the credential, and your existing professional experience level. While there's no singular 'magic number,' here is a realistic breakdown based on extensive industry observation:
- Foundational Certifications (e.g., CompTIA Security+): For IT professionals possessing some prior IT experience, a focused study period of 2-4 months can be sufficient. For those entering the field with no prior IT background, allocate closer to six months for comprehensive preparation.
- Intermediate Certifications (e.g., CompTIA CySA+, PenTest+): Progressing to credentials at this level typically requires a similar 3-5 month dedicated study window, predicated on having thoroughly mastered foundational knowledge.
- Expert-Level Certifications (e.g., CISSP, CISM, CISA): Advanced certifications like the CISSP represent a fundamentally different challenge. While the exam itself is rigorously challenging, the primary barrier is often the stringent experience requirement—typically demanding five years of verifiable professional work within the field. These are not quick study achievements but rather the culmination of years of dedicated, strategic career development.
Ultimately, your personal timeline is a function of your disciplined commitment. It is directly correlated to the consistency with which you can allocate dedicated time for focused study and hands-on practice.
Remember: in the marathon of certification, consistency and deliberate effort invariably lead to success.
Ready to meticulously build your personal cyber security cert roadmap and confidently conquer your next certification exam? MindMesh Academy is dedicated to empowering IT professionals with expert-curated study guides, evidence-based learning tools, and a supportive community to help you master challenging material and pass with unwavering confidence. Begin your strategic certification journey today by exploring our resources at CompTIA Security+ Practice Exams.

Written by
Alvin Varughese
Founder, MindMesh Academy
Alvin Varughese is the founder of MindMesh Academy and holds 15 professional certifications including AWS Solutions Architect Professional, Azure DevOps Engineer Expert, and ITIL 4. He's held senior engineering and architecture roles at Humana (Fortune 50) and GE Appliances. He built MindMesh Academy to share the study methods and first-principles approach that helped him pass each exam.