8 CISSP Exam Sample Questions to Master the Test
Mastering the CISSP Exam: A Strategic Approach Through 8 Sample Questions
The Certified Information Systems Security Professional (CISSP) exam is more than a test of your knowledge; it's a profound evaluation of your strategic thinking as a senior cybersecurity leader. Many IT professionals preparing for this credential dedicate countless hours to studying facts and figures, only to find the actual exam demands a different kind of intelligence. Unlike typical certification tests that often focus on rote memorization, the CISSP assesses your ability to apply a managerial and risk-based mindset to complex scenarios. It challenges you to analyze situations from the perspective of an experienced security architect or CISO, rather than just recalling definitions.
At MindMesh Academy, we believe effective preparation goes beyond rote learning. This guide is designed to elevate your study strategy. We'll meticulously dissect eight high-quality sample questions, one from each of the core CISSP domains. For each question, you won't just get the correct answer; you'll receive a detailed breakdown of the scenario, an in-depth analysis of why certain distractors are incorrect, and actionable insights to sharpen your critical thinking.
Our objective is to equip you with the analytical framework necessary to deconstruct intricate scenarios under pressure. You will learn to identify subtle keywords, evaluate options through a comprehensive risk management lens, and select the best possible answer – which isn't always the most technically obvious one. This strategic approach fosters the confidence needed to tackle the real exam, transforming your preparation from a simple memorization drill into a genuine development of advanced professional judgment. Let's begin breaking down the exam's logic, domain by domain.
1. CISSP Domain 1: Security and Risk Management Sample Question
Domain 1, Security and Risk Management, is the foundational cornerstone of the CISSP certification. It encompasses the overarching principles of information security governance, enterprise risk management, and regulatory compliance. For IT professionals, mastering this domain means understanding how to align security initiatives with business objectives, manage organizational risk, and navigate the complex landscape of legal and regulatory requirements. Questions in this domain invariably test your ability to think like a seasoned manager, prioritizing strategic decisions that balance security posture with operational and financial realities. They rarely ask for simple definitions; instead, they present multi-faceted scenarios requiring you to choose the BEST course of action from a governance perspective.
Strategic Analysis of a Sample Question
Let's dissect a typical scenario-based question you might encounter, emphasizing the managerial mindset.
Scenario: A rapidly growing financial services company plans to expand its operations into the European Union. The Chief Information Security Officer (CISO) is tasked with developing an information security program that aligns with business goals and meets regulatory demands, such as GDPR. Which of the following should be the CISO's FIRST step?
A. Implement an intrusion detection system (IDS). B. Conduct a quantitative risk analysis on all assets. C. Develop a security policy based on a recognized framework. D. Mandate annual security awareness training for all employees.
Analysis & Breakdown:
The core challenge of this question is to identify the most foundational and strategic action. While options A, B, and D are all valid and necessary security activities, they are tactical implementations rather than strategic starting points for building an entire security program.
- Option A (Implement an IDS): This is a technical control, a reactive measure. Deploying technology without a guiding policy, defined risks, and clear objectives is premature and inefficient. It's like buying an expensive alarm system before you've decided what you're trying to protect and why.
- Option B (Conduct a quantitative risk analysis): Risk analysis is indeed crucial. However, the scope and parameters of a risk analysis should be guided by an overarching governance structure. Attempting a comprehensive quantitative analysis without a foundational policy or framework can be disorganized, incomplete, and may not fully address the new regulatory context (EU expansion). A framework provides the structure for how and what risks to analyze.
- Option D (Mandate annual security awareness training): Training is absolutely essential for employee behavior. However, employees must be trained on what to do and why. This "what" and "why" comes directly from established policies and procedures. You cannot effectively train employees on rules that haven't been formally defined and approved.
Correct Answer: C. Developing a security policy based on a recognized framework (e.g., ISO 27001, NIST Cybersecurity Framework) provides the essential governance structure. This strategic document outlines the organization's security philosophy, objectives, and high-level rules, which then guides all subsequent security decisions, including risk analysis, control selection and implementation, and training initiatives. It's the blueprint before construction begins.
Actionable Takeaways & Study Tips
This type of question powerfully illustrates the CISSP's emphasis on a top-down, governance-first approach to security. Policy and strategy always precede technical implementation.
- Reflection Prompt: Consider your own organization. Does security implementation often lead strategy, or is it firmly rooted in overarching policies and risk assessments? How might this impact effectiveness?
- A thorough understanding of information security frameworks like ISO 27001 certification is paramount for mastering this domain. These frameworks provide the structure for establishing, implementing, maintaining, and continually improving an information security management system (ISMS).
- When studying, focus on the purpose and scope of different frameworks and how they help organizations manage risk systematically and achieve compliance (e.g., GDPR, HIPAA, PCI DSS).
- Connect to Other Certifications: Principles from Domain 1 are also vital for certifications like the PMP (Project Management Professional), where risk management is a core component, or any cloud security certification (e.g., AWS Certified Security - Specialty, Azure Security Engineer Associate) where understanding shared responsibility models and compliance in the cloud is critical.
The infographic below illustrates a simplified decision process for selecting a foundational security framework, a common scenario in Domain 1 questions.
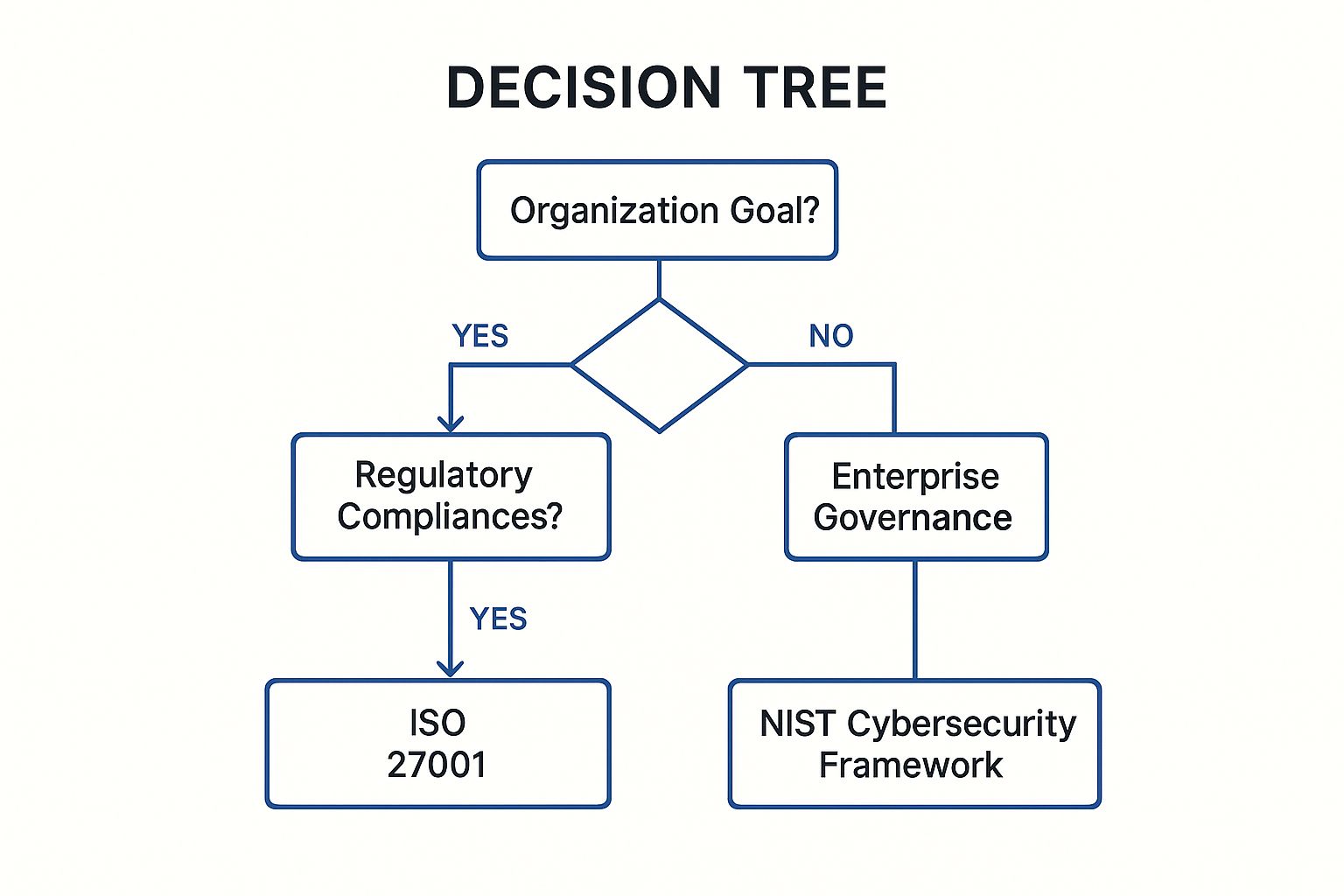 This decision tree guides you through selecting the most appropriate foundational security framework based on an organization's primary drivers, whether regulatory compliance, industry best practices, or broader enterprise governance. Mastering this strategic mindset, which prioritizes aligning security with business objectives, is crucial for the CISSP exam.
This decision tree guides you through selecting the most appropriate foundational security framework based on an organization's primary drivers, whether regulatory compliance, industry best practices, or broader enterprise governance. Mastering this strategic mindset, which prioritizes aligning security with business objectives, is crucial for the CISSP exam.
2. CISSP Domain 2: Asset Security Sample Question
Domain 2, Asset Security, delves into the critical lifecycle management of information and the assets (systems, hardware, software) that process, store, and transmit it. This domain covers everything from data classification, ownership, and handling to secure retention and eventual disposal. For IT professionals, understanding asset security means knowing how to identify valuable information, classify it appropriately, and apply the correct protection mechanisms based on its sensitivity, criticality, and regulatory requirements. You will frequently encounter scenarios requiring you to make informed decisions about data labeling, retention periods, and the secure destruction of various media types.
Strategic Analysis of a Sample Question
Let's break down a typical Domain 2 scenario question focusing on data lifecycle management.
Scenario: A healthcare organization is updating its data handling policy for patient records, which are classified as "Confidential" and fall under HIPAA regulations. The Chief Privacy Officer (CPO) wants to ensure that physical documents containing this data are disposed of securely at the end of their legally mandated retention period. Which of the following disposal methods is the MOST appropriate for this data classification?
A. Placing the documents in a standard office recycling bin. B. Storing the documents indefinitely in a secure off-site facility. C. Shredding the documents using a cross-cut shredder. D. Erasing the documents with a standard office degausser.
Analysis & Breakdown:
This question requires you to logically link a specific, highly sensitive data classification ("Confidential" patient records under HIPAA) to the most robust and appropriate physical disposal method. You must evaluate each option based on established security best practices for protecting confidentiality during end-of-life processing.
- Option A (Placing in a standard office recycling bin): This option offers absolutely no security. It's equivalent to publicly displaying the information and would constitute a severe data breach, completely violating patient privacy and HIPAA mandates. This is never an appropriate method for sensitive data.
- Option B (Storing indefinitely in a secure off-site facility): While secure storage is important, indefinite storage violates the fundamental principle of data retention – information should only be kept for as long as it is legally required or operationally necessary. Indefinite storage increases risk (more data, more opportunities for breach) and incurs unnecessary costs without justification. Data minimization is a key principle.
- Option D (Erasing documents with a standard office degausser): Degaussing is a method used to destroy data on magnetic storage media (like hard drives, tapes, or floppy disks) by neutralizing the magnetic fields. It is entirely ineffective and irrelevant for physical paper documents. This option tests your knowledge of disposal methods specific to media types.
Correct Answer: C. Shredding paper documents with a cross-cut shredder is a widely accepted, highly effective, and auditable method for securely destroying sensitive physical information. A cross-cut shredder cuts paper into small, confetti-like pieces, making reconstruction extremely difficult and significantly reducing the risk of unauthorized disclosure. This directly addresses the need to protect the confidentiality of patient records during disposal, aligning with HIPAA's security requirements.
Actionable Takeaways & Study Tips
This question underscores the direct and critical link between data classification and the required security controls throughout the entire information lifecycle, from creation to destruction. The higher the classification (e.g., Confidential, Restricted), the more robust and stringent the handling, storage, and disposal requirements become.
- Reflection Prompt: How do your organization's data handling policies specifically address different data classifications? Are there clear procedures for disposal of both digital and physical sensitive assets?
- For Domain 2, it's crucial to memorize common data classification schemes (e.g., Public, Internal, Confidential, Restricted, Top Secret) and the corresponding controls for labeling, handling, storage, and destruction.
- Also, extensively study data retention concepts, understanding that data should not be kept forever. Learn about the importance of having a formal, auditable retention schedule that balances legal/regulatory requirements with business needs.
- Finally, understand the purpose and applicability of different destruction techniques: shredding (paper), pulverizing/incineration (various media), degaussing (magnetic media), cryptographic erasure (digital media), and physical destruction (hard drives, flash drives). Knowing which technique applies to which type of media is essential for CISSP exam success.
3. CISSP Domain 3: Security Architecture and Engineering Sample Question
Domain 3, Security Architecture and Engineering, delves into the technical and theoretical core of cybersecurity. It tests your deep understanding of security models, cryptographic principles, system components, and secure design principles. For IT architects and engineers, this domain is about building security into systems from the ground up, rather than adding it as an afterthought. Questions from this domain often require you to move beyond policy and apply complex engineering concepts to solve security problems, making it one of the more technically demanding but ultimately rewarding areas of the CISSP exam. You'll need to demonstrate knowledge of secure system design, secure software development, and the application of security principles to various technologies.
 This diagram visually represents a multi-layered secure system architecture, highlighting how different components like firewalls, servers, and encryption work together. Understanding the interplay of these elements is fundamental to mastering Domain 3 and designing resilient, secure systems.
This diagram visually represents a multi-layered secure system architecture, highlighting how different components like firewalls, servers, and encryption work together. Understanding the interplay of these elements is fundamental to mastering Domain 3 and designing resilient, secure systems.
Strategic Analysis of a Sample Question
Let's break down a typical question that assesses your understanding of fundamental security architecture principles during the design phase.
Scenario: A software development team is building a new financial application that will handle sensitive customer data, including personally identifiable information (PII) and transaction details. A security architect has been tasked with ensuring the system is designed with a "secure-by-default" posture to minimize potential vulnerabilities from its inception. Which of the following design principles is MOST effective for minimizing the potential attack surface from the outset?
A. Defense in Depth B. Fail-Secure C. Economy of Mechanism D. Least Privilege
Analysis & Breakdown:
This question asks for the security principle most foundational and effective for proactively minimizing the system's attack surface during the initial design phase. While all options are crucial security principles, one directly relates to reducing complexity and potential vulnerabilities from the start.
- Option A (Defense in Depth): This principle involves layering multiple, independent security controls to protect assets (e.g., firewall, IDS, antivirus, strong authentication). While vital for a robust security posture, it is a reactive strategy to protect an existing attack surface, rather than minimizing the attack surface itself from the beginning. It assumes an attack surface exists and adds layers around it.
- Option B (Fail-Secure): This principle ensures that if a system component fails, it does so in a way that defaults to a secure, restricted, or safe state (e.g., a firewall blocking all traffic if it crashes, a door locking if power fails). This is critical for system resilience and availability, but it's a response to failure, not a primary mechanism to reduce the initial attack surface by simplifying the design.
- Option D (Least Privilege): This principle dictates that users, processes, or systems should be granted only the minimum necessary permissions to perform their authorized functions. While it significantly reduces the impact of a compromise, it doesn't directly shrink the system's overall attack surface (the sum of all potential entry points, exposed functions, and code paths). It limits what can be done if an attack surface is exploited, but not the size of that surface.
Correct Answer: C. Economy of Mechanism, also known as Simplicity in Design, dictates that security designs should be kept as simple, small, and streamlined as possible. A less complex system has fewer components, less code, fewer interdependencies, and therefore fewer potential vulnerabilities, misconfigurations, or hidden flaws. By minimizing complexity from the initial design phase, this principle directly and proactively minimizes the attack surface, making the system inherently more secure from its foundation.
Actionable Takeaways & Study Tips
This type of CISSP exam sample question highlights the importance of not just knowing security principles but understanding their specific application, hierarchy, and when they are most effective in the system development lifecycle.
- Reflection Prompt: Think about a system you've worked on. Can you identify areas where "Economy of Mechanism" could have been better applied to reduce complexity and potential vulnerabilities?
- For Domain 3, focus on the "why" behind each principle. Economy of Mechanism is a proactive design choice that prevents vulnerabilities by reducing the attack surface. In contrast, principles like Defense in Depth and Fail-Secure are often implemented to manage risk in a system that is already built or facing potential failure.
- When studying, create a matrix that maps security principles to specific goals, such as "Attack Surface Reduction," "Breach Containment," "System Resilience," or "Confidentiality/Integrity/Availability." This structured approach will help you differentiate between closely related concepts and choose the MOST appropriate answer in a scenario.
- Connect to Other Certifications: Principles of secure design, like Economy of Mechanism and Least Privilege, are fundamental to any secure development certification (e.g., CompTIA CySA+, Certified Secure Software Lifecycle Professional - CSSLP) and cloud architecture certifications (e.g., AWS Certified Solutions Architect - Professional, Microsoft Certified: Azure Solutions Architect Expert) where designing resilient and secure cloud-native applications is paramount.
4. CISSP Domain 4: Communication and Network Security Sample Question
Domain 4, Communication and Network Security, dives deep into the architecture, protocols, and secure design of network systems. It covers the vast landscape from foundational models like OSI and TCP/IP to modern wireless, cellular, and cloud networking paradigms. For IT professionals, mastering this domain means not only understanding how networks function but, more importantly, how to secure data in transit and protect network infrastructure from evolving threats. Questions in this domain often test your ability to apply security principles to various network designs, select appropriate controls to mitigate communication-based vulnerabilities, and understand the trade-offs involved in different networking technologies.
Strategic Analysis of a Sample Question
Let's break down a typical scenario-based question you might see from this domain, focusing on choosing the most current and robust network security solution.
Scenario: A company is implementing a new wireless network across its corporate office. The network will be primarily used by employees to access sensitive internal company resources, and also offer a separate segment for guests to access the internet. The security architect has been asked to select the MOST secure protocol to protect the employee wireless network, ensuring strong encryption and authentication against modern attack vectors. Which of the following should be chosen?
A. WPA with TKIP B. WPA2 using a pre-shared key (PSK) C. WPA3 with Simultaneous Authentication of Equals (SAE) D. WEP with 128-bit encryption
Analysis & Breakdown:
The core of this question is identifying the strongest, most current, and resilient wireless security protocol available for protecting sensitive enterprise data. The mention of both employee and guest access provides context, but the primary focus is on securing the employee network with the absolute best available option to withstand modern attacks.
- Option A (WPA with TKIP): WPA (Wi-Fi Protected Access) was an interim solution developed to address the severe flaws in WEP. It uses Temporal Key Integrity Protocol (TKIP), which introduced per-packet key mixing. However, WPA with TKIP has known vulnerabilities (e.g., related to the Michael Message Integrity Code) and is now considered deprecated and insecure for protecting sensitive data.
- Option B (WPA2 using a pre-shared key (PSK)): WPA2 (Wi-Fi Protected Access II) has been the de facto standard for many years, offering robust AES-based encryption. However, when used with a pre-shared key (PSK) in WPA2-Personal mode, it remains vulnerable to offline dictionary attacks if an attacker captures the four-way handshake. A weak PSK can be brute-forced relatively easily, compromising the network. While significantly better than WPA or WEP, it's not the most secure option available today, especially for sensitive corporate resources.
- Option D (WEP with 128-bit encryption): WEP (Wired Equivalent Privacy) is a completely broken and obsolete protocol with severe cryptographic vulnerabilities (e.g., weak initialization vector usage, key reuse) that can be exploited by readily available tools in minutes, regardless of key length. It provides virtually no meaningful security and should never be used in any environment.
Correct Answer: C. WPA3 (Wi-Fi Protected Access 3) is the latest and most secure wireless protocol, designed to address the shortcomings of WPA2. Its most significant improvement, especially relevant for personal/enterprise use without 802.1X, is the use of Simultaneous Authentication of Equals (SAE) handshake. SAE provides robust protection against offline dictionary attacks and mitigates key reinstallation attacks, even with relatively simple passwords. It establishes forward secrecy and makes eavesdropping on encrypted traffic much harder, making it superior to WPA2-PSK and the MOST secure choice for an employee network handling sensitive data.
Actionable Takeaways & Study Tips
This question demonstrates that CISSP candidates must remain current with network security standards and understand the incremental improvements in security protocols. Simply knowing that WPA2 is better than WEP is insufficient; you must grasp why WPA3 offers superior protection.
- Reflection Prompt: How up-to-date is your organization's wireless network security? What challenges might you face in upgrading to WPA3, and what are the security benefits?
- A deep understanding of the OSI model and how different security protocols operate at each layer (e.g., MACsec at Layer 2, IPsec at Layer 3, SSL/TLS at Layer 4/7) is critical for Domain 4.
- When studying, focus on the "why" behind each protocol's development. For instance, why was WPA3 developed? What specific vulnerabilities in WPA2 does it aim to address (e.g., KRACK attacks, offline dictionary attacks on PSK)? This level of comprehension is far more valuable than simply memorizing acronyms and will help you analyze complex CISSP exam sample questions effectively.
- Concentrate on the security benefits and weaknesses of various network protocols (e.g., VPNs, DNSSEC, secure remote access methods) and secure network configurations (e.g., network segmentation, firewall rules, intrusion prevention systems).
5. CISSP Domain 5: Identity and Access Management Sample Question
Domain 5, Identity and Access Management (IAM), is a fundamental and critical area of cybersecurity. It focuses on ensuring that the right individuals have the right level of access to the right resources at the right time, and are held accountable for their actions. For IT professionals, mastering IAM involves understanding a spectrum of technologies and principles, from robust authentication methods and sophisticated access control models to the entire identity lifecycle (provisioning, deprovisioning, review). Expect scenarios that require you to apply IAM principles to solve complex organizational security challenges, such as integrating new systems, managing privileged users, or complying with regulatory mandates like HIPAA or GDPR, where data access is paramount.
Strategic Analysis of a Sample Question
Let's break down a typical scenario-based IAM question that tests your understanding of access control models in a high-security context.
Scenario: A financial institution is implementing a new privileged access management (PAM) solution to secure its critical infrastructure, including database servers and network devices. The primary goal is to enforce the principle of least privilege for system administrators, ensuring they only have temporary, elevated access precisely when needed for specific tasks. Which of the following access control models is BEST suited for this purpose, given the need for centralized policy enforcement and auditing?
A. Discretionary Access Control (DAC) B. Role-Based Access Control (RBAC) C. Mandatory Access Control (MAC) D. Attribute-Based Access Control (ABAC)
Analysis & Breakdown:
This question requires you to identify the access control model that most effectively enforces centrally managed, strict security policies, which is the core requirement for privileged access and the principle of least privilege in an enterprise environment. The emphasis is on centralized management and task-based access.
- Option A (DAC - Discretionary Access Control): DAC allows the data owner (or resource owner) to grant or revoke access to their resources. This model is highly flexible but is decentralized and does not enforce least privilege from a central authority. It's too permissive and inconsistent for securing critical infrastructure where system administrators require strictly controlled access based on their job function.
- Option C (MAC - Mandatory Access Control): MAC is a highly restrictive model based on security labels (e.g., "Top Secret" clearance for users, "Secret" classification for data). It's primarily used in highly sensitive environments like military or government systems, where secrecy is paramount. While very secure, MAC is rigid, complex to implement, and typically overkill for a typical corporate PAM solution, which needs to align access with dynamic job functions rather than static security classifications.
- Option D (ABAC - Attribute-Based Access Control): ABAC is a powerful and flexible model that grants access based on a combination of attributes of the user (e.g., department, role, security clearance), the resource (e.g., sensitivity, owner), and the environment (e.g., time of day, location, device security posture). While ABAC can certainly enforce least privilege and dynamic access, it is generally more complex to design and implement than RBAC. For the specific purpose of defining access based on job function and ensuring consistent, centralized control over system administrator roles, RBAC is often the more direct, commonly implemented, and practical solution in many corporate PAM contexts.
Correct Answer: B. Role-Based Access Control (RBAC) is the ideal model for this scenario. RBAC assigns permissions to roles (e.g., "Database Administrator," "Network Engineer," "Level 2 Support") rather than directly to individual users. Users are then assigned to one or more roles. This simplifies administration, ensures consistency across a group of users performing similar tasks, and directly enforces the principle of least privilege by granting access only necessary for a specific job function or task. When combined with a PAM solution, RBAC ensures that administrators can only assume privileged roles temporarily, providing tight control, auditing capabilities, and strict adherence to least privilege.
Actionable Takeaways & Study Tips
This type of CISSP exam sample question emphasizes the practical application of different access control models. Memorizing definitions is not enough; you must understand the "why" and "when" behind each model's suitability for specific organizational and security requirements.
- Reflection Prompt: How is access currently managed for privileged users in your environment? What challenges exist, and could a different access control model or PAM solution improve security and compliance?
- When studying, focus on creating a mental map of which model to use in specific scenarios:
- DAC: Best for flexible, user-controlled environments (e.g., personal files).
- RBAC: Ideal for corporate environments where access aligns with job functions and roles, promoting centralized management and least privilege.
- MAC: Reserved for highly sensitive, classified data environments (e.g., military).
- ABAC: Powerful for dynamic, context-aware access decisions, especially in complex, distributed, or cloud-native environments, but often with higher implementation complexity.
- Connect to Other Certifications: IAM principles are central to virtually every IT certification focused on security or cloud computing, including AWS (IAM service), Azure (Azure AD, RBAC), CompTIA Security+, and GIAC certifications. Understanding the concepts here will provide a solid foundation for managing identities and access across any platform.
6. CISSP Domain 6: Security Assessment and Testing Sample Question
Domain 6, Security Assessment and Testing, covers the crucial tools, techniques, and methodologies used to evaluate the security posture of an organization's assets. This domain is absolutely critical for validating the effectiveness of implemented security controls, identifying vulnerabilities before malicious actors can exploit them, and ensuring ongoing compliance. For IT professionals, mastering this domain means knowing when and how to deploy various testing types – from vulnerability scanning to penetration testing – and how to interpret their results. Questions from this domain often require you to differentiate between assessment methodologies and choose the most appropriate test for a given security objective.
Strategic Analysis of a Sample Question
Let's dissect a common scenario you might face in these CISSP exam sample questions, focusing on the most realistic testing method.
Scenario: An organization wants to test its incident response team's effectiveness and its technical defenses (e.g., SIEM alerts, firewall rules) against a sophisticated, targeted attack. The test should accurately simulate a real-world adversary's tactics, techniques, and procedures (TTPs), with minimal prior knowledge provided to the defenders or SOC team. The objective is to evaluate both the preventative controls and the detection-and-response capabilities under realistic pressure. Which of the following is the MOST appropriate type of penetration test?
A. White-box test B. Double-blind test C. Gray-box test D. Internal security audit
Analysis & Breakdown:
The key to this question lies in understanding the explicit objectives: testing both the incident response team (often called the "blue team") and the technical controls against a realistic threat actor. The prompt's crucial clue is "minimal prior knowledge provided to the defenders," indicating a desire for a surprise element to truly gauge detection and response.
- Option A (White-box test): This involves providing the testers with full knowledge of the target environment, including network diagrams, source code, and credentials. It is extremely useful for a deep technical review and identifying obscure vulnerabilities, but it does not realistically test the response team's detection and reaction capabilities under surprise conditions because they know the test is happening and often its scope.
- Option C (Gray-box test): This approach provides testers with partial knowledge of the environment, such as user-level credentials or some system documentation. While more realistic than white-box, it still gives the "red team" (attackers) an advantage that a true external adversary might not initially possess, and crucially, the blue team might still be aware of the test.
- Option D (Internal security audit): An audit is a compliance-focused review, typically against a set of standards, policies, or regulations. It assesses adherence to established controls and identifies gaps. It is not a simulated, active attack designed to test the real-time defensive and response capabilities of a security team.
Correct Answer: B. A double-blind test (often a component of a "red team" exercise), also known as a full "black-box" test where the security team (blue team) is also unaware of the test, is the most suitable option. In this scenario, the attackers (red team) have no internal knowledge, mimicking an external adversary, and critically, the defenders (blue team, SOC, incident response team) are not forewarned of the test. This setup provides the most realistic simulation of an actual targeted attack, effectively evaluating both technical preventative/detective controls and the human response procedures, communication, and decision-making under genuine pressure.
Actionable Takeaways & Study Tips
This question highlights the importance of matching the security assessment methodology to the specific security objective. Simply knowing the definitions of white, gray, and black box testing is not enough; you must understand their strategic purpose and the conditions under which each is most effective.
- Reflection Prompt: When was the last time your organization performed a security assessment that genuinely surprised your defensive teams? What were the key takeaways, and how did it improve your posture?
- When studying for Domain 6, create a chart comparing different assessment types (e.g., vulnerability scans vs. penetration tests vs. red teaming vs. audits vs. bug bounties) and their respective goals, scope, prerequisites, and expected outcomes.
- Focus on the "why" behind each test. A white-box test is for thoroughness and deep technical dives. A black-box test is for simulating external adversaries without internal knowledge. A double-blind test is for realism and validating the complete defensive and response capabilities of the human element. Understanding this distinction is key to correctly answering many scenario-based CISSP exam sample questions in this domain.
- To deepen your understanding, you can explore resources that detail how to manage a bug bounty program, which often involves similar principles of testing and vulnerability discovery, but with external researchers.
7. CISSP Domain 7: Security Operations Sample Question
Domain 7, Security Operations, is the domain that encapsulates the day-to-day, hands-on work of information security professionals. It covers the practical application of security principles to protect assets and respond effectively when security events and incidents occur. This includes critical functions like incident response, disaster recovery, logging and monitoring, vulnerability management, patch management, and managing security controls in an operational environment. For IT professionals, mastering Domain 7 means understanding how to maintain the confidentiality, integrity, and availability (CIA) of systems and data through continuous vigilance and rapid, coordinated response. The CISSP exam sample questions from this domain will test your understanding of established procedures and best practices for managing security incidents.
Strategic Analysis of a Sample Question
Let’s analyze a typical question that reflects the operational, procedural nature of this domain, focusing on immediate incident handling.
Scenario: A Security Operations Center (SOC) analyst receives an alert from the Security Information and Event Management (SIEM) system. The alert indicates multiple failed login attempts for a highly privileged administrator account from an unfamiliar external IP address, immediately followed by a single successful login from the same suspicious IP. Which of the following is the MOST appropriate immediate action for the analyst to take, following established incident response protocols?
A. Immediately block the source IP address at the perimeter firewall. B. Begin a full forensic investigation of the affected server. C. Escalate the incident to the Computer Incident Response Team (CIRT). D. Shut down the compromised server to prevent further damage.
Analysis & Breakdown:
This question requires you to apply a logical, procedural approach to the initial phase of incident handling, specifically focusing on the immediate appropriate action. Each option represents a possible action, but only one aligns with the established hierarchy and goals of incident response.
- Option A (Immediately block the source IP address): While blocking the malicious IP is a valid containment step, it might be premature as the immediate first action for an SOC analyst. Blocking the IP might alert the attacker that their presence has been detected, potentially causing them to escalate their activities or pivot to other systems. Furthermore, an SOC analyst might not have the authority or a pre-approved procedure to unilaterally block an external IP at the firewall without coordination. The absolute first step is often identification and escalation.
- Option B (Begin a full forensic investigation): A full forensic investigation is a later, resource-intensive phase in the incident response process (Eradication/Recovery/Post-Incident Analysis). Kicking it off immediately is premature before the incident has been properly identified, triaged, contained, and authorized by the appropriate teams (CIRT/management). Starting forensics too early can also disrupt volatile evidence.
- Option D (Shut down the server): Shutting down a server is a drastic containment measure that could cause significant business disruption, lead to data loss, and destroy volatile evidence crucial for investigation (e.g., memory contents, active network connections). It's a measure typically reserved for confirmed, high-impact compromises where the risk of continued operation outweighs the cost of downtime, and it must be a coordinated decision made by the CIRT or management, not an immediate unilateral action by an SOC analyst.
Correct Answer: C. The SOC analyst's primary role in this situation (Identification phase of incident response) is to triage the event, confirm it's a legitimate incident (not a false positive), and then escalate it according to the incident response plan. Escalating to the Computer Incident Response Team (CIRT) ensures that a dedicated team with the necessary authority, expertise, and resources can take over. The CIRT is responsible for coordinating the comprehensive response, making informed decisions about containment, eradication, recovery, and communication, ensuring the incident is handled systematically and effectively while minimizing business impact. This step formalizes the incident handling process.
Actionable Takeaways & Study Tips
This question powerfully underscores the importance of understanding formal incident response procedures and the roles within a security team. Memorizing the phases of incident response (Preparation, Identification, Containment, Eradication, Recovery, and Lessons Learned - "PICERL") is essential.
- Reflection Prompt: Review your organization's incident response plan. Are the immediate steps for an SOC analyst clearly defined? What are the escalation paths for different incident severities?
- Focus on the specific actions and goals of each phase. For instance, Identification and Triage happen before deep analysis or drastic containment measures. The SOC analyst is primarily an "identifier" and "escalator" in complex situations.
- Your study should emphasize the operational roles and responsibilities within a security team (e.g., SOC analyst, incident responder, forensic investigator, CISO). Knowing who does what, and when, is a common theme in Security Operations questions.
- Developing a strong foundational knowledge of operational security can be structured similarly to how one might prepare for other high-stakes certifications, where process, procedure, and a structured approach to problem-solving are just as important as raw technical knowledge.
8. CISSP Domain 8: Software Development Security Sample Question
Domain 8, Software Development Security, is a crucial area that focuses on integrating security throughout the entire Software Development Lifecycle (SDLC). For IT professionals involved in development, architecture, or security assurance, this domain emphasizes that security is not an afterthought but an intrinsic part of software creation from requirements gathering to deployment and maintenance. It tests your understanding of secure coding principles, application vulnerability assessments, and how to effectively embed security controls and testing methods at each stage of development. Questions often present scenarios where you must choose the most effective security control, testing method, or design principle at a specific stage of the SDLC to mitigate common application vulnerabilities.
 This image represents the iterative nature of integrating security throughout the Software Development Lifecycle (SDLC). From initial design to testing and deployment, security considerations must be woven into every phase to build resilient and trustworthy applications, a core concept in CISSP Domain 8.
This image represents the iterative nature of integrating security throughout the Software Development Lifecycle (SDLC). From initial design to testing and deployment, security considerations must be woven into every phase to build resilient and trustworthy applications, a core concept in CISSP Domain 8.
Strategic Analysis of a Sample Question
Let’s examine a common type of question you'll see from this domain, focusing on matching the right testing method to specific constraints.
Scenario: During the formal testing phase of a web application's SDLC, a quality assurance (QA) team is tasked with identifying security vulnerabilities that could result from insecure coding practices, such as SQL injection, cross-site scripting (XSS), and broken authentication. A key constraint is that the QA team does not have access to the application's source code and needs to test the application as an end-user or external attacker would. Which of the following testing methods should be performed?
A. Static Application Security Testing (SAST) B. Dynamic Application Security Testing (DAST) C. Code review D. Unit testing
Analysis & Breakdown:
This question requires you to know the fundamental differences between major application security testing types and, crucially, their prerequisites and perspectives. The key constraints are the "testing phase" (implying the application is runnable) and the critical detail of "no access to the source code."
- Option A (SAST - Static Application Security Testing): SAST is a "white-box" testing method. It analyzes an application's source code, byte code, or binary code without executing it, looking for patterns that indicate security vulnerabilities (e.g., insecure functions, unhandled inputs). It cannot be performed without direct access to the application's source code. Therefore, it's unsuitable given the scenario's constraint.
- Option C (Code review): Similar to SAST, a manual or automated code review is a "white-box" technique that requires direct examination of the source code. Security experts or tools scrutinize the code line by line to identify flaws. This also requires source code access, making it incorrect for this scenario.
- Option D (Unit testing): Unit testing is a white-box testing method typically performed by developers during the coding phase. It focuses on testing individual components or "units" of source code to ensure they function as expected. While developers might include security checks in unit tests, it's primarily a functional test and not a comprehensive security vulnerability assessment like the one described, and it absolutely requires code access.
Correct Answer: B. Dynamic Application Security Testing (DAST) is a "black-box" testing method that analyzes a running application from the outside, without requiring access to its internal source code. It simulates external attacks (like an end-user or malicious actor would) by sending various inputs to the application's exposed interfaces (e.g., web requests, APIs) and observing its behavior for vulnerabilities like SQL injection, XSS, broken authentication, and improper error handling. DAST is the perfect choice for this scenario because it aligns with the "no source code access" constraint and effectively identifies runtime vulnerabilities that an external attacker could exploit.
Actionable Takeaways & Study Tips
Understanding the "when" (SDLC phase) and "why" (objective) of different security testing methodologies is critical for success in Domain 8.
- Reflection Prompt: How are application security tests integrated into your team's SDLC? Do you use a mix of SAST and DAST, and at what points in the development process?
- Memorize which methods are "white-box" (e.g., SAST, code review), "black-box" (e.g., DAST, traditional penetration testing), or "grey-box" (a hybrid approach with partial knowledge).
- Focus on the OWASP Top 10 vulnerabilities (e.g., injection, broken authentication, sensitive data exposure, XSS), as they are frequently referenced and tested in these types of CISSP exam sample questions.
- The ability to apply the right test to the right SDLC phase and understand its specific benefits and limitations is a core competency. Approaching these questions with a calm and structured mindset is essential; you can find helpful strategies to overcome exam anxiety and boost your confidence to ensure you perform your best on test day.
CISSP Domain Sample Questions Comparison
| Domain Title | Implementation Complexity 🔄 | Resource Requirements ⚡ | Expected Outcomes 📊 | Ideal Use Cases 💡 | Key Advantages ⭐ |
|---|---|---|---|---|---|
| CISSP Domain 1: Security and Risk Management | Moderate to High | Extensive knowledge of frameworks | Strong foundation in security governance | Risk management and security policy development | Applies to diverse regulatory & business needs |
| CISSP Domain 2: Asset Security | Moderate | Knowledge of privacy laws and data handling | Effective data classification and protection | Data governance and regulatory compliance | Supports data loss prevention programs |
| CISSP Domain 3: Security Architecture and Engineering | High | Deep technical expertise | Robust security architectures and defense in depth | Designing secure systems and cloud migrations | Covers fundamental and timeless security models |
| CISSP Domain 4: Communication and Network Security | Moderate to High | Understanding of evolving network tech | Secure network architectures and protocol selection | Network design, remote access, cloud security | Balances offensive and defensive security |
| CISSP Domain 5: Identity and Access Management | Moderate | Knowledge of diverse authentication tech | Strong IAM frameworks and access control systems | User authentication, federation, privileged access | Balances user experience with security |
| CISSP Domain 6: Security Assessment and Testing | Moderate to High | Familiarity with testing tools and methods | Improved security posture through assessments | Vulnerability management and security auditing | Covers manual & automated testing approaches |
| CISSP Domain 7: Security Operations | Moderate | Operational tools & incident handling | Effective incident response and continuous monitoring | Daily security management and SOC operations | Practical, real-world security application |
| CISSP Domain 8: Software Development Security | Moderate to High | Understanding of development & security | Secure SDLC and mitigated application vulnerabilities | Secure coding, DevSecOps, application security | Addresses modern development security challenges |
Turn These Examples into Exam Success
Navigating the extensive depths of the eight CISSP domains can feel like a monumental task, but the sample questions we've meticulously dissected in this article are your essential compass. They reveal a critical truth about the exam: it’s less about rote memorization and more about adopting a specific, strategic, and managerial mindset. The ultimate goal isn't just to know an answer; it's to deeply understand the why behind the best choice, always from a holistic risk management and governance perspective.
Throughout our detailed analysis, you've seen how the CISSP exam consistently prioritizes business objectives, comprehensive risk mitigation, and strategic governance over purely technical, in-the-weeds solutions. This is the core principle that consistently separates passing candidates from those who struggle. By working through these CISSP exam sample questions, you’re not merely practicing; you are actively retraining your brain to think and respond like a seasoned security professional operating at an executive level.
Key Strategic Takeaways to Carry Forward
To transform this acquired knowledge into a definitive passing score, it is crucial to internalize these core strategies. These are the patterns that successful test-takers recognize, apply, and rely upon on exam day.
- Managerial Mindset First: Always ask yourself, "What is the primary concern for senior management or the CISO in this situation?" This perspective will consistently point you toward solutions that address overarching risk, compliance, business continuity, and strategic objectives, rather than simply the most technically elegant or immediate fix.
- Process Over Product: The CISSP exam heavily values well-defined processes, robust policies, and established procedures. When presented with a choice between implementing a specific technology and establishing a foundational governance process (like a comprehensive risk assessment, a formal data classification policy, or a structured incident response plan), the process is almost always the more strategic, and therefore correct, answer.
- The "Most" Correct Answer: Be acutely aware that many CISSP questions will feature multiple plausible or even technically correct options. Your task is to identify the most encompassing, most effective, or highest-level answer that holistically addresses the scenario. Look for the choice that tackles the root cause of the problem, not just a symptom.
- Human Safety is Paramount: In any scenario involving physical security, disaster recovery, emergency response, or business continuity, the preservation of human life and safety always takes unequivocal precedence over protecting assets, maintaining operations, or minimizing financial loss. This is a non-negotiable ethical and professional principle.
Your Actionable Path to Certification
Simply reading through these examples is not enough for true mastery. Real, lasting comprehension and skill come from active, engaged study. Here is your clear roadmap to build upon what you've learned today and achieve your certification goal.
- Deconstruct, Don't Just Answer: For every practice question you encounter, resist the urge to stop at merely selecting the right answer. Force yourself to articulate precisely why each of the other three options is incorrect or, more subtly, why it is less correct or less appropriate in the given context. This deepens your comprehension of the nuances and reinforces the CISSP mindset.
- Create Your Own Scenarios: Take a key concept, like the Biba Integrity Model, the phases of the Incident Response lifecycle, or a specific security principle (e.g., separation of duties), and write your own challenging sample question. This exercise forces you to think like the exam creators, anticipate common distractors, and profoundly solidifies the material in your mind.
- Systematize Your Review: Passive review leads to forgotten information. To ensure you're retaining these complex topics over time, you need a structured, active approach. Learn how to make study guides that actually work by incorporating active recall, spaced repetition, and mnemonic devices, transforming your notes from a simple reference into a powerful, dynamic learning tool.
- Connect the Dots Between Domains: The CISSP domains are not isolated silos; they are deeply interconnected. A concept from Domain 3 (Security Architecture) will inevitably impact Domain 7 (Security Operations), and risk assessments from Domain 1 underpin decisions across all others. As you study, constantly look for these interconnections and relationships to build a truly holistic and integrated understanding of information security.
Ultimately, these CISSP exam sample questions are not just practice material; they are a vital tool. They are meticulously designed to sharpen your analytical skills, refine your test-taking strategy, and build the unwavering confidence needed to walk into the testing center fully prepared. Embrace the challenge, focus on internalizing the underlying principles, and you will be exceptionally well-equipped to earn one of the most respected and valuable credentials in the industry.
For a structured approach to your preparation, explore our CompTIA Security+ Study Guide.
Ready to move beyond static questions and into a dynamic, adaptive learning environment that truly optimizes your study time? MindMesh Academy offers a comprehensive CISSP preparation platform built on evidence-based techniques like Spaced Repetition and active recall to help you master complex concepts efficiently and effectively. Transform your study sessions and track your progress toward certification with our expert-curated materials and innovative tools. Explore how we can empower your journey at MindMesh Academy.

Written by
Alvin Varughese
Founder, MindMesh Academy
Alvin Varughese is the founder of MindMesh Academy and holds 15 professional certifications including AWS Solutions Architect Professional, Azure DevOps Engineer Expert, and ITIL 4. He's held senior engineering and architecture roles at Humana (Fortune 50) and GE Appliances. He built MindMesh Academy to share the study methods and first-principles approach that helped him pass each exam.