
CCNA Exam Preparation Questions: 8 Key Tips for 2025
CCNA Exam Preparation Questions: 8 Essential Strategies for IT Professionals in 2025
The Cisco Certified Network Associate (CCNA) exam serves as a crucial launchpad for a thriving career in network engineering. It demands more than just memorizing facts; it requires a deep, practical understanding of the foundational concepts that underpin modern IT infrastructure. For IT professionals aiming to solidify their networking expertise and earn this vital certification, mastering the types of questions that assess real-world application is paramount.
This guide goes beyond simple question dumps, offering a strategic breakdown of eight critical topic areas, complete with insights into the kind of CCNA exam preparation questions you must conquer. We'll explore practical scenarios, provide clear explanations, and share actionable tips to help you command the material. From the fundamental OSI model to advanced routing protocols and robust network security, consider this your comprehensive roadmap to not just passing, but truly excelling.
At MindMesh Academy, we believe in building true competency. Our approach helps you understand the why behind each configuration and protocol, preparing you for the exam's performance-based questions and the daily challenges of a real networking environment. By focusing on critical thinking and application, you’ll be ready to analyze problems and select the best solutions under pressure. To effectively cover all necessary concepts and maximize your study time, explore actionable strategies to study smarter, not harder. Let's dive into the essential CCNA exam preparation questions and topics you must master.
1. OSI Model and TCP/IP Model Layers
Understanding the OSI and TCP/IP models is fundamental for any IT professional, especially those serious about passing the CCNA exam. These layered frameworks are the bedrock of networking, meticulously explaining how data traverses from an application on one device, across various network segments, to an application on another. The CCNA exam heavily tests your ability to correctly map protocols, hardware, and functions to their respective layers, making this a critical area of study.
The OSI model, with its seven layers, offers a granular, theoretical blueprint, while the more pragmatic four-layer TCP/IP model reflects how real-world networks are typically implemented. A key skill is comprehending how these layers interact, a process known as encapsulation and de-encapsulation. Imagine data as a letter: as it moves down the stack, each layer adds its own "envelope" (header or trailer) with specific instructions. As it moves up the stack at the destination, each layer "unwraps" its envelope, processing the instructions within.
Why This Concept is Crucial
A strong grasp of these models empowers you to think like a network engineer or a system administrator. When troubleshooting connectivity issues, you can apply a systematic, layered approach, much like a detective. For instance, you might start at the Physical layer (Layer 1) by asking: "Is the cable plugged in?" or "Is the link light on?" and progressively move upwards. This structured methodology is essential for efficiently diagnosing and resolving complex network problems, a skill frequently tested in CCNA exam preparation questions and indispensable in roles across IT, including those requiring ITIL service operation principles.
Pro Tip: Don't just memorize the layers. Focus intently on the function and purpose of each layer. For example, understand that the Network Layer (Layer 3) is responsible for logical addressing (IP addresses) and path determination (routing), which is precisely why routers operate at this layer.
Actionable Study Tips
- Mnemonic Devices: Utilize classic mnemonics like "Please Do Not Throw Sausage Pizza Away" to recall the OSI layers from bottom (Physical) to top (Application). Create your own for the TCP/IP model if it helps.
- Protocol Mapping: Design flashcards or a digital spreadsheet that rigorously maps common protocols (e.g., HTTP, HTTPS, FTP, TCP, UDP, IP, ARP, Ethernet) to their corresponding OSI and TCP/IP layers.
- Visualize the Flow: Sketch diagrams tracing a simple network interaction, such as a web browser requesting a page. Illustrate how data is encapsulated at the source (from Application down to Physical) and then de-encapsulated at the destination, highlighting what happens at each step.
- Practical Analysis: Use a packet analyzer tool like Wireshark to capture and inspect real network traffic. Examining live packets will profoundly solidify your understanding of how headers and trailers are added and processed at each layer.
The following concept map illustrates the direct relationship between the functional layers of the TCP/IP model and their corresponding OSI model layers.
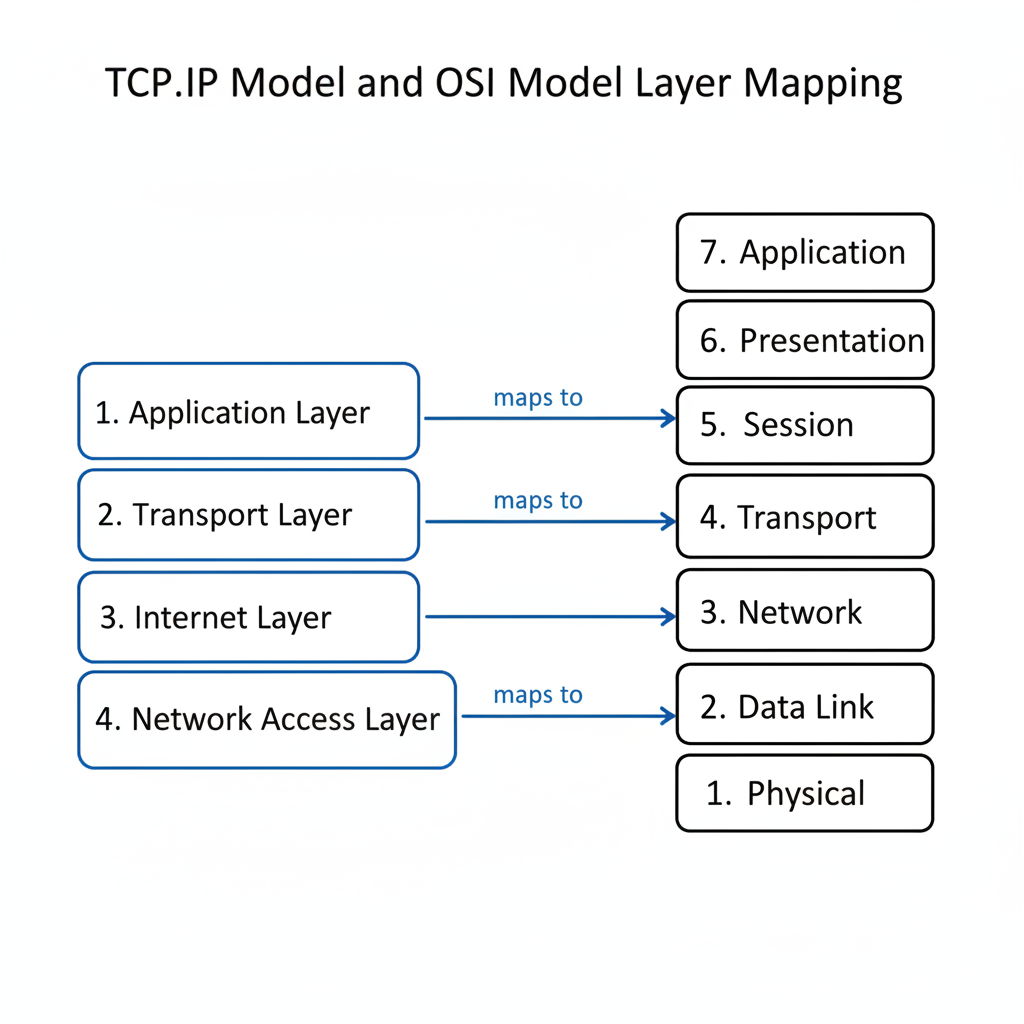 Figure 1: Relationship between the OSI and TCP/IP Model Layers. This visualization clarifies how the TCP/IP model's Network Access layer consolidates functions of the OSI model's lower layers.
Figure 1: Relationship between the OSI and TCP/IP Model Layers. This visualization clarifies how the TCP/IP model's Network Access layer consolidates functions of the OSI model's lower layers.
Reflection Prompt: How might a misunderstanding of layer functions lead to incorrect troubleshooting steps in a real-world network outage?
2. Subnetting and VLSM (Variable Length Subnet Masking)
Mastering IPv4 subnetting and Variable Length Subnet Masking (VLSM) is arguably one of the most critical skills for the CCNA exam. This concept involves the strategic division of a larger IP network into smaller, more manageable sub-networks, or subnets. The ability to perform these calculations swiftly and accurately is a frequent focus of CCNA exam preparation questions, as it directly demonstrates a core understanding of IP addressing efficiency and network design.
 Figure 2: Subnetting and VLSM Illustration. This infographic demonstrates how a larger network is efficiently divided into smaller, optimized subnets.
Figure 2: Subnetting and VLSM Illustration. This infographic demonstrates how a larger network is efficiently divided into smaller, optimized subnets.
Subnetting facilitates superior network management, enhances security through traffic segmentation, and significantly reduces broadcast traffic. VLSM takes this efficiency a step further by allowing you to employ different subnet masks for different subnets, drastically minimizing wasted IP addresses. For example, you could assign a /26 mask (providing 62 usable hosts) to a department with 50 users, and a /29 mask (yielding 6 usable hosts) for a point-to-point link between two routers, all from the same original network block. This principle is also crucial in cloud environments, like segmenting subnets within an AWS VPC or an Azure VNet.
Why This Concept is Crucial
Subnetting isn't merely a theoretical exercise; it's a fundamental, daily task for any network engineer involved in designing, implementing, or troubleshooting a network. A solid grasp of subnetting is indispensable for configuring routers, creating Access Control Lists (ACLs), and implementing routing protocols. The CCNA exam tests this skill relentlessly through multiple-choice questions, drag-and-drop scenarios, and even simulation labs where you might need to design an efficient IP addressing scheme. It’s a foundational skill for managing network resources effectively.
Pro Tip: Prioritize speed and accuracy in your calculations. During the exam, you won't have the luxury of second-guessing your answers. The "magic number" method is a popular shortcut: for a given subnet mask, find the last "interesting" octet (the one that's not 255 or 0) and subtract its value from 256. The result is your network increment or block size.
Actionable Study Tips
- Memorize Powers of Two: Quickly recall the powers of 2 (2, 4, 8, 16, 32, 64, 128). This foundational knowledge is essential for rapidly calculating network ranges, host counts, and subnet masks.
- Daily Practice: Dedicate 10-15 minutes every single day to solving subnetting problems. Consistent practice builds the mental muscle memory necessary for exam success. Focus on common CIDR masks like /24 through /30.
- Create a Reference Chart: During your studies, construct a detailed chart listing CIDR notations (e.g., /25, /26), their corresponding subnet masks, the number of subnets each allows, and the number of usable hosts per subnet. This visual aid can accelerate your understanding.
- Use VLSM Scenarios: Practice designing network schemes for varied requirements, such as "a network needs subnets for 50, 25, and 10 hosts." Always begin by addressing the largest host requirement first to optimize address allocation.
- Verify with Calculators: After manually completing subnetting problems, use an online subnet calculator to check your work. This helps identify and correct any recurring mistakes in your process.
To gain a better feel for the types of problems you will face, you should engage with a variety of practice questions. Seek out top CCNA practice test questions and resources to test your subnetting skills.
3. Spanning Tree Protocol (STP) Operations
Understanding the Spanning Tree Protocol (STP) is essential for mastering Layer 2 networking, a core component of the CCNA curriculum. STP's primary function is to prevent catastrophic broadcast storms and MAC address table instability by creating a loop-free logical topology in networks that feature redundant physical links. The CCNA exam will challenge your knowledge of how STP achieves this through a carefully orchestrated process of root bridge election, port role assignment, and port state transitions.
Exam questions often present a network diagram and require you to determine which switch will become the root bridge, which ports will be designated as root ports or designated ports, and critically, which ports are ultimately placed into a blocking state to logically break any loops. This requires a solid grasp of fundamental concepts such as the Bridge ID (composed of Bridge Priority + MAC address) and the nuances of path cost calculation.
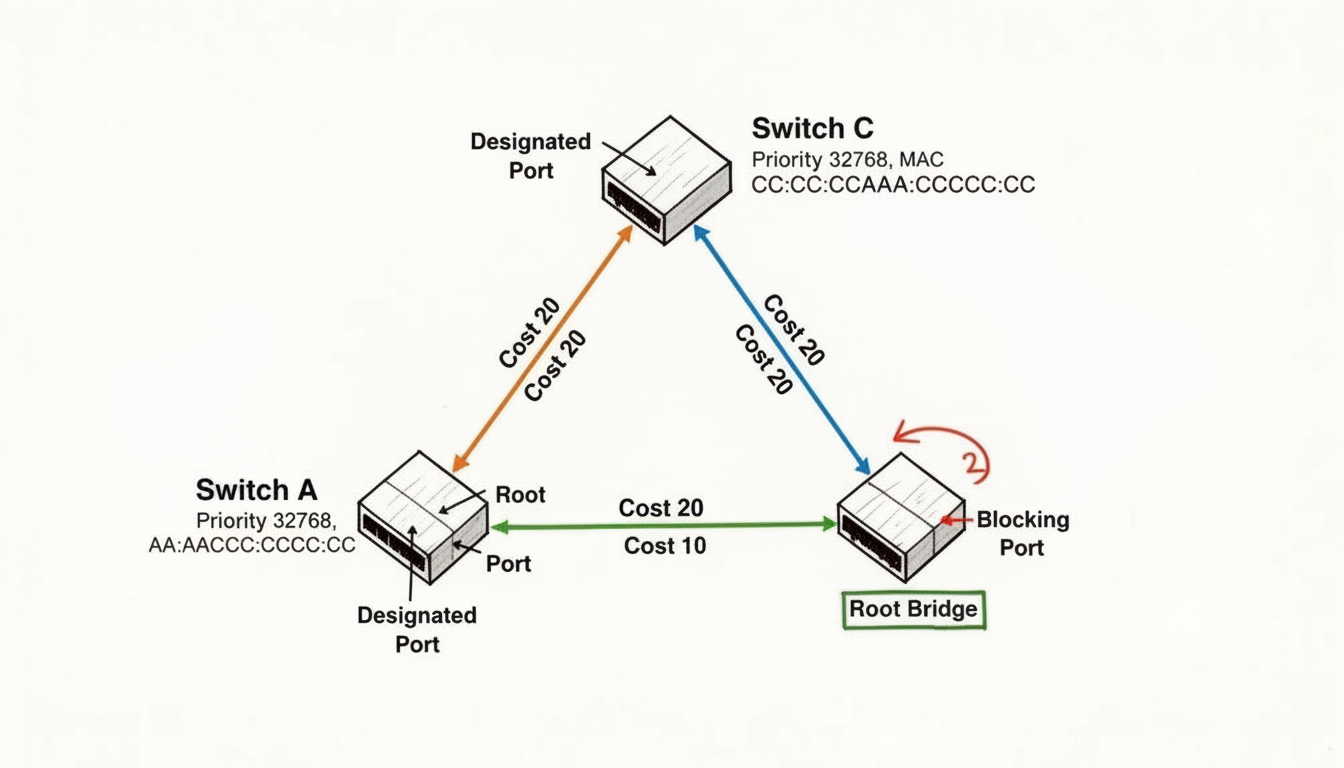 Figure 3: Spanning Tree Protocol (STP) Operation. This diagram illustrates how STP prevents network loops by designating port roles and blocking redundant paths.
Figure 3: Spanning Tree Protocol (STP) Operation. This diagram illustrates how STP prevents network loops by designating port roles and blocking redundant paths.
Why This Concept is Crucial
Without STP, even a simple redundant connection between two switches could create a broadcast storm that rapidly brings an entire network down in seconds. A deep understanding of STP operations enables you to design, implement, and troubleshoot resilient switched networks, a critical skill in enterprise environments and for architects aiming for high availability, similar to how redundancy is managed in AWS or Azure fault-tolerant designs. Many CCNA exam preparation questions focus on troubleshooting scenarios where a misconfigured STP setup is causing insidious connectivity issues, making this a highly practical, real-world skill that is heavily tested.
Pro Tip: Remember the election criteria for the root bridge in strict order: The switch with the lowest Bridge Priority becomes the root. If priorities are identical, the switch with the lowest MAC address wins. All other decisions, such as root port and designated port selection, are consistently based on the lowest cumulative cost to reach that root bridge.
Actionable Study Tips
- Diagram and Calculate: When studying any network topology, always draw it out meticulously. Manually trace the paths, calculate the root path cost from each non-root switch, and precisely determine the port roles (Root, Designated, Blocking).
- Memorize Path Costs: Commit the default STP path costs to memory for different link speeds: 10 Gbps = 2, 1 Gbps = 4, 100 Mbps = 19, 10 Mbps = 100. This is non-negotiable for quickly solving exam problems.
- Know the Flavors: Clearly differentiate between the original STP (802.1D) and its faster successor, Rapid STP (802.1w or RSTP). Understand RSTP’s streamlined port states (Discarding, Learning, Forwarding) and its significantly faster convergence time.
- Practice Command Output: Become an expert at interpreting the output of the
show spanning-treecommand. You should be able to instantly identify the root bridge, local switch priority, port costs, states, and roles purely from the command output.
Reflection Prompt: If a network experiences a broadcast storm after a new switch is added, what are your immediate STP-related troubleshooting steps?
4. VLAN Configuration and Trunking
Virtual LANs (VLANs) are a fundamental technology for segmenting a physical network into multiple logical broadcast domains. Mastering VLAN configuration and the trunking mechanisms that allow them to span across multiple switches is a cornerstone of the CCNA curriculum. The CCNA exam will rigorously test your ability to create, assign, and troubleshoot VLANs, as well as configure trunk links using the industry-standard 802.1Q tagging protocol.
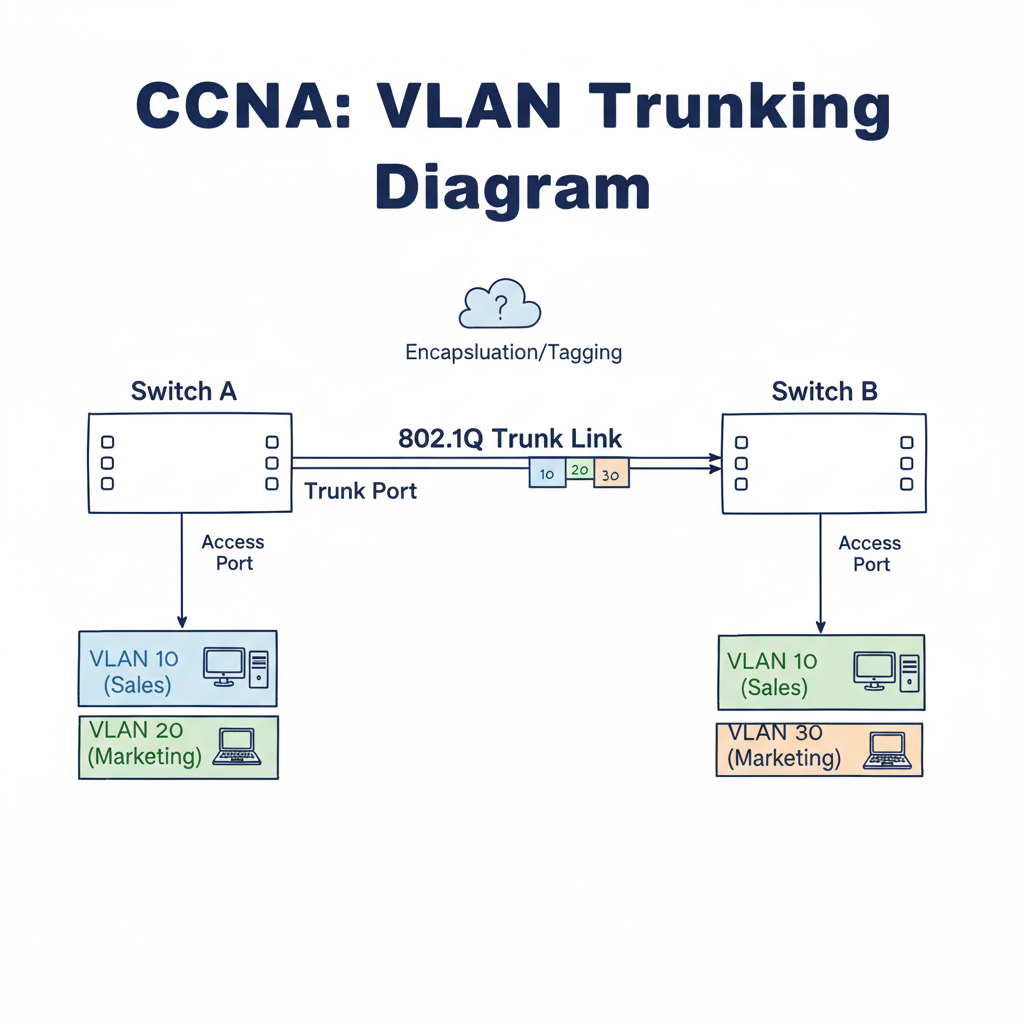 Figure 4: VLAN Configuration and Trunking. This diagram illustrates how VLANs logically segment a physical network and how trunking allows multiple VLANs to traverse a single link.
Figure 4: VLAN Configuration and Trunking. This diagram illustrates how VLANs logically segment a physical network and how trunking allows multiple VLANs to traverse a single link.
Understanding this topic necessitates knowing the clear distinction between an access port (which belongs exclusively to a single VLAN) and a trunk port (which carries traffic for multiple VLANs, often tagged). You must also grasp the concept of a native VLAN, where traffic is sent untagged across a trunk link, and the methods for routing between different VLANs, such as employing a "router-on-a-stick" configuration. These segmentation principles are also vital for securing environments like Azure VNets or AWS VPCs.
Why This Concept is Crucial
VLANs are indispensable for modern network design, delivering significant security, flexibility, and performance enhancements by isolating traffic and reducing the size of broadcast domains. CCNA exam preparation questions frequently present scenarios where you must diagnose connectivity issues directly caused by incorrect VLAN assignments, native VLAN mismatches on trunks, or misconfigured trunk links. A deep understanding of VLANs unequivocally demonstrates your readiness to manage and secure a sophisticated switched network environment.
Pro Tip: Always meticulously verify your trunk configurations. A prevalent mistake is a native VLAN mismatch between two switches connected by a trunk. Use the
show interfaces trunkcommand to confirm that the native VLAN and the allowed VLANs are consistent and correctly configured on both ends of a trunk link.
Actionable Study Tips
- Command Line Practice: Gain extensive hands-on experience in a lab environment (e.g., Cisco Packet Tracer, GNS3, or real hardware) with essential commands like
vlan 10,name Sales,interface FastEthernet0/1,switchport mode access,switchport access vlan 10,switchport mode trunk, andswitchport trunk allowed vlan add 20,30. - Router-on-a-Stick: Practice the router-on-a-stick inter-VLAN routing configuration repeatedly. Remember the precise syntax for creating subinterfaces (
interface GigabitEthernet0/0.10) and assigning an IP address along with the encapsulation command (encapsulation dot1q 10). - Troubleshooting Scenarios: Actively create your own troubleshooting labs. For example, intentionally configure a native VLAN mismatch or prune a necessary VLAN from a trunk, and then systematically work through the steps to identify and rectify the problem.
- VTP Concepts: While less emphasized on current exams, understand the roles of VTP (VLAN Trunking Protocol): Server, Client, and Transparent. Know that VTP Transparent mode switches do not participate in the VTP domain but will still forward VTP advertisements.
Reflection Prompt: Consider an organization with multiple departments. How do VLANs contribute to both security and performance within their network?
5. Routing Protocols: OSPF and EIGRP Configuration
Dynamic routing protocols are the strategic heart of any scalable network, automating the processes of route discovery and maintenance. The CCNA exam places a significant emphasis on your ability to configure, verify, and troubleshoot two of the most prevalent interior gateway protocols: OSPF (Open Shortest Path First) and EIGRP (Enhanced Interior Gateway Routing Protocol). Your understanding must extend beyond basic commands to encompass the underlying theory of their operation, such as how they form neighbor adjacencies, calculate metrics, and advertise routes.
Questions in this domain test practical skills like applying network commands with correct wildcard masks or identifying subtle misconfigurations that prevent neighbor relationships from forming. You'll need to know the specific operational details of both protocols, from OSPF's Designated Router (DR) and Backup Designated Router (BDR) election process on multi-access networks to EIGRP's sophisticated use of a composite metric (which considers bandwidth, delay, reliability, and load). Mastering these protocols is essential for anyone tackling modern CCNA exam preparation questions and managing complex network topologies, including hybrid cloud connectivity scenarios involving AWS Direct Connect or Azure ExpressRoute.
Why This Concept is Crucial
A deep understanding of OSPF and EIGRP is fundamental to building and managing robust, enterprise-grade networks. In real-world scenarios, static routing is impractical and inefficient for all but the smallest or simplest environments. Knowing how to correctly implement dynamic routing allows you to create networks that can automatically adapt to topology changes, such as a link failure, ensuring continuous connectivity and high availability. The CCNA exam tests this knowledge to ensure you possess the core competency required of a network associate responsible for maintaining network connectivity and efficiency.
Pro Tip: When troubleshooting routing protocol issues, always begin with the basics. Use the
show ip protocolscommand first to obtain a high-level summary of your routing protocol configurations, including which networks are being advertised and which interfaces are actively participating. This provides an excellent starting point for diagnosis.
Actionable Study Tips
- Memorize OSPF States: Use a mnemonic like "Down In 2 Exchange Lanes Forever" to remember the OSPF neighbor states: Down → Init → 2-Way → Exstart → Exchange → Loading → Full. Knowing this precise sequence helps you pinpoint exactly where the adjacency process is failing.
- Understand Wildcard Masks: Practice converting subnet masks to wildcard masks and vice-versa. Remember, a wildcard mask is the inverse of a subnet mask (e.g., a 255.255.255.0 subnet mask corresponds to a 0.0.0.255 wildcard mask). This is crucial for correctly defining networks in routing protocols and ACLs.
- Lab Everything: There is absolutely no substitute for hands-on practice. Utilize a simulator like Cisco Packet Tracer or an emulator like GNS3 to build various network topologies and configure both OSPF and EIGRP from scratch. Intentionally "break" configurations to learn how to systematically identify and fix them.
- Master Verification Commands: Repeatedly use commands like
show ip ospf neighbor,show ip eigrp neighbors,show ip route ospf, andshow ip route eigrpto become fluent in interpreting their output and rapidly identifying issues.
Reflection Prompt: How do dynamic routing protocols like OSPF and EIGRP address the scalability challenges that would arise from using static routes in a large enterprise network?
6. Access Control Lists (ACLs) - Standard and Extended
Access Control Lists (ACLs) are a fundamental security tool in networking, functioning as programmable filters to control which traffic is permitted or denied access to specific parts of a network. The CCNA exam requires a deep understanding of how to configure, apply, and troubleshoot both standard and extended ACLs. These meticulously crafted rulesets are critical for implementing robust security policies and effectively managing network traffic flow.
Standard ACLs are the simpler of the two, filtering traffic based solely on the source IP address. In contrast, extended ACLs provide far more granular control by evaluating a broader range of criteria, including source and destination IP addresses, specific protocols (such as TCP or UDP), and even particular port numbers (like port 80 for HTTP or port 443 for HTTPS). Mastering their syntax and application logic is essential for any aspiring network engineer, and understanding their function can be mapped to concepts like AWS Security Groups or Azure Network Security Groups.
Why This Concept is Crucial
ACLs serve as the front-line defense for network security directly on a router or switch. They are instrumental in protecting sensitive internal resources, controlling access to and from the internet, and mitigating certain types of network attacks. Questions on the CCNA exam will test your ability to not only write precise ACL statements but also to strategically place them on the correct interface in the optimal direction (inbound or outbound) to achieve a desired security outcome. This knowledge is immediately applicable in real-world security roles.
Pro Tip: Remember the crucial logic of ACL placement. Standard ACLs, which only filter by source IP, should ideally be placed as close to the destination as possible. Extended ACLs, which are far more specific, should be placed as close to the source of the traffic as possible to filter unwanted traffic early in its path, conserving network resources.
Actionable Study Tips
- Rule of Thumb: Always internalize the implicit
deny any anystatement that is automatically appended to the end of every ACL. If traffic does not explicitly match apermitstatement earlier in the list, it will be silently dropped by this implicit rule. - Order Matters: ACLs are processed sequentially from top to bottom. The very first matching rule is applied, and no further rules in that ACL are checked. Therefore, always place your most specific rules at the very top of the list to ensure they are evaluated first.
- Named vs. Numbered: While numbered ACLs are functional, become comfortable with named ACLs. They are inherently more descriptive, making them easier to read and troubleshoot. Crucially, named ACLs allow you to edit and resequence individual lines without needing to delete and recreate the entire list.
- Verification Commands: Practice using
show access-liststo view your configured ACLs andshow ip interface [interface_name]to verify which ACL is applied to a specific interface and in which direction (inbound or outbound). - Wildcard Masks: Master the use of wildcard masks, which are the inverse of subnet masks. For example, to specify a single host like
192.168.1.10, you can efficiently use thehostkeyword or the wildcard mask0.0.0.0.
Reflection Prompt: How do ACLs on a router complement or differ from firewall rules in an organization's overall security strategy?
7. NAT and PAT Configuration (Network/Port Address Translation)
Network Address Translation (NAT) is a fundamental technology for conserving IPv4 addresses and enhancing the security of private networks, making it a guaranteed topic on the CCNA exam. NAT translates private IP addresses, which are explicitly not routable on the public internet, into public IP addresses. The exam will test your hands-on ability to configure, verify, and troubleshoot different NAT types, including static NAT, dynamic NAT, and Port Address Translation (PAT), often referred to as NAT overload.
Understanding the various NAT types and their specific use cases is crucial. Static NAT provides a one-to-one mapping between a private and a public IP address, ideal for publicly accessible servers. Dynamic NAT maps a private IP to an available IP from a predefined pool of public addresses. PAT, the most common and powerful type, maps multiple private IPs to a single public IP by utilizing unique source port numbers, thereby enabling thousands of internal hosts to simultaneously access the internet using a very limited number of public IPs. This is akin to how AWS NAT Gateways or Azure NAT Gateways provide outbound internet access for resources in private subnets.
Why This Concept is Crucial
In the real world, virtually every small to large enterprise network extensively uses NAT. A firm grasp of its configuration is essential for providing internet access to internal users and for securely publishing internal resources to the outside world. The CCNA exam preparation questions in this area are meticulously designed to test your practical skills in setting up these translations and ensuring they function correctly, directly reflecting the daily tasks of a network administrator.
Pro Tip: Memorize the precise NAT terminology: Inside Local (the private IP of an internal host), Inside Global (the public IP address representing the internal host to the outside world), Outside Local (the actual private IP address of an external host as seen by the internal host), and Outside Global (the actual public IP address of the external host). Questions will often use this specific language to test your understanding.
Actionable Study Tips
- Define Translation Sources: Before configuring dynamic NAT or PAT, always first create a standard Access Control List (ACL) to explicitly specify which internal private IP addresses are permitted to be translated. This ensures only authorized traffic undergoes translation.
- Interface Designation: A common and critical mistake is forgetting to designate the
ip nat insideandip nat outsideinterfaces. The NAT translation will not function without these commands, so make them an integral part of your standard configuration checklist. - Master Verification Commands: Practice extensively using
show ip nat translationsto view active translations in real-time andshow ip nat statisticsto check for configuration errors, monitor pool usage, and observe translation hits or misses. - Practice PAT Overload: For PAT, remember to add the
overloadkeyword at the very end of your NAT pool configuration statement. This single keyword is what enables the powerful many-to-one translation that makes PAT so efficient and widely used.
Reflection Prompt: Given the global push towards IPv6, why is understanding and configuring IPv4 NAT/PAT still a critical skill for networking professionals?
8. Network Device Security and Management
Securing network devices is a fundamental responsibility of any IT professional and a core component of the CCNA curriculum. This area covers the essential configurations required to protect Cisco routers and switches from unauthorized access, configuration tampering, and malicious activity. The CCNA exam will test your ability to implement security best practices, ranging from basic password protection and secure remote access to port-level security and centralized device management.
Questions in this domain focus heavily on hands-on configuration skills. You'll be expected to know the exact commands for setting up strong, encrypted passwords, configuring SSH to replace the insecure Telnet, locking down console and virtual terminal (VTY) lines, and leveraging protocols like NTP (Network Time Protocol) and Syslog for accurate event logging and proactive monitoring. Mastery of these skills demonstrates that you can establish a secure and manageable network foundation, crucial for adhering to compliance standards like ISO 27001 or CIS Benchmarks.
Why This Concept is Crucial
A misconfigured network device is akin to an open door for attackers, potentially leading to unauthorized configuration changes, reconnaissance attacks, data breaches, and significant network downtime. A strong understanding of device hardening practices prevents these vulnerabilities. CCNA exam preparation questions often present scenarios where you must identify and rectify security flaws, reinforcing the idea that security is not an afterthought but an integral and continuous part of network administration. This knowledge is immediately applicable in any real-world networking role.
Pro Tip: Always prioritize SSH over Telnet for remote management. Telnet transmits all data, including sensitive login credentials, in clear text, making it a significant security risk. Use the
transport input sshcommand on VTY lines to explicitly disable Telnet and only permit secure, encrypted connections.
Actionable Study Tips
- Prioritize Strong Passwords: Always use the
enable secretcommand instead ofenable password. Theenable secretcommand uses a strong MD5 hash (Type 5 encryption), whileenable passworduses a weak, easily reversible encryption (Type 7). - Secure Remote Access: Practice the full SSH configuration process repeatedly: set a hostname, set a domain name, generate RSA crypto keys (e.g.,
crypto key generate rsa modulus 2048), create a local user database, and applylogin localandtransport input sshto the VTY lines. - Implement Port Security: Memorize the commands to configure port security on a switch interface, including setting the maximum number of allowed MAC addresses and defining the violation mode (
protect,restrict, orshutdown). - Centralize Logging: Configure devices to send their logs to a remote Syslog server. This ensures log data is preserved even if the device itself is compromised. Similarly, use NTP to synchronize device clocks for accurate timestamping, which is crucial for correlating security events across the network. Understanding centralized logging is also key in cloud environments, like utilizing services such as CloudWatch and CloudTrail.
- Disable Unnecessary Services: Routinely turn off any services that are not explicitly required to reduce the device's attack surface. For example, use
no cdp runglobally to disable Cisco Discovery Protocol if it isn't needed, especially on internet-facing interfaces.
Reflection Prompt: Beyond technical configurations, what organizational policies (e.g., password rotation, access reviews) complement device security configurations?
CCNA Exam Prep: Key Topic Comparison
| Topic | Implementation Complexity 🔄 | Resource Requirements ⚡ | Expected Outcomes 📊 | Ideal Use Cases 💡 | Key Advantages ⭐ |
|---|---|---|---|---|---|
| OSI Model and TCP/IP Model Layers | Moderate - requires memorization and layered understanding | Low - mainly theoretical study resources | Strong foundational knowledge and troubleshooting skills | Network troubleshooting, certification exams | Universal networking foundation, systematic approach |
| Subnetting and VLSM | High - involves complex calculations and binary conversions | Moderate - practice tools and dedicated time | Efficient IP address allocation and network design | IP address planning, network segmentation | Precise address allocation, exam-relevant skill |
| Spanning Tree Protocol (STP) | Moderate to high - understanding theory and CLI commands | Moderate - lab access recommended | Prevention of Layer 2 loops, network stability | Switch network design, loop avoidance | Loop prevention, network reliability |
| VLAN Configuration and Trunking | Moderate - requires configuration commands and conceptual clarity | Moderate - lab/simulators ideal | Network segmentation and traffic management | Enterprise LAN segmentation, security | Network segmentation, improved security |
| Routing Protocols (OSPF & EIGRP) | High - complex concepts and multiple commands | Moderate - emulators, labs beneficial | Dynamic routing efficiency and scalable networks | Enterprise WAN routing, dynamic route management | Efficient routing, real-world protocol knowledge |
| Access Control Lists (ACLs) | Moderate - command syntax and logic order important | Low - mostly configuration based | Enhanced network security through traffic filtering | Traffic control, security enforcement | Flexible security enforcement, broad applicability |
| NAT and PAT Configuration | Moderate - understanding translation types and configurations | Low to moderate - lab practice helpful | Network connectivity with IP conservation | Internet access for private networks | Enables private-public IP mapping, scalability |
| Network Device Security & Management | Moderate to high - multiple features and security layers | Moderate - requires secure practice setups | Strong device security and controlled management | Secure device access, compliance | Essential security hardening, quick impact |
From Practice to Performance: Your Next Steps
You've just navigated a comprehensive collection of CCNA exam preparation questions, covering the core pillars of modern networking from the OSI model to robust device security. This journey through practice questions is far more than a mere academic exercise; it's a strategic diagnostic of your readiness. Each question you've considered, whether answered correctly or incorrectly, has illuminated your strengths and, more importantly, pinpointed your specific areas for improvement. The ultimate goal isn't simply to memorize answers, but to deeply internalize the why behind each configuration, protocol, and command.
Think of the topics we've covered as interconnected building blocks in a complex network architecture. A solid understanding of Subnetting and VLSM forms the bedrock upon which effective ACLs are designed. Similarly, troubleshooting a failed OSPF adjacency might require you to trace the problem all the way down to a misconfigured VLAN or trunking port. True CCNA exam success lies in discerning these intricate connections and moving fluidly between concepts.
Synthesizing Knowledge into Action
The key takeaway from this extensive guide is that passive reading alone is insufficient. Active, hands-on practice is the only reliable path to certification mastery. The difference between a candidate who passes the CCNA exam and one who falls short often comes down to the muscle memory developed in a command-line interface (CLI) and the unwavering confidence that comes from intentionally breaking and then systematically fixing a network hundreds of times in a lab environment.
To transform this knowledge into tangible, job-ready skills, your next steps should be deliberate and structured:
- Identify Your Weakest Links: Rigorously review your performance on practice questions and self-assessments. Did you struggle with wildcard masks in ACLs? Were the nuances of Spanning Tree Protocol port states confusing? Isolate these specific topics for intensive, targeted review.
- Build It, Break It, Fix It: Launch a network simulator like Cisco Packet Tracer or an emulator like GNS3. For every topic discussed in this guide, create a dedicated lab scenario. Configure OSPF, then intentionally shut down an interface to observe the convergence process. Implement a standard ACL, then test it with pings and other traffic to witness its filtering action. This practical application is non-negotiable for true understanding.
- Master the
showCommands: Your most powerful troubleshooting and verification tool on the exam and in the real world is theshowcommand family. Become profoundly comfortable with commands likeshow ip route,show interfaces trunk,show spanning-tree,show access-lists, andshow ip protocols. Knowing precisely what command to use to verify a configuration or diagnose a problem will save you critical time and boost your confidence.
The True Value of CCNA Mastery
Pursuing the CCNA is about far more than just passing an exam. It’s about building a foundational understanding of how digital information traverses the globe, the internet, and complex enterprise networks. Mastering these topics equips you with the essential skills to design, implement, and secure the networks that power businesses, connect communities, and enable innovation across every industry.
When you can confidently subnet a network, you are demonstrating efficiency and meticulous resource management. When you can secure a router with hardened configurations and precise ACLs, you are actively protecting valuable digital assets. This certification is a powerful signal to employers that you possess the practical, in-demand skills required to be a valuable and effective member of any IT team. Let these CCNA exam preparation questions be the catalyst that propels you from simply studying networking concepts to truly understanding and implementing them. Your persistence, coupled with hands-on practice, are the final ingredients needed to turn your certification goal into a career-defining achievement.
Ready to transform your weak areas into strengths with a guided, intelligent study plan? MindMesh Academy offers adaptive learning paths that analyze your performance on CCNA exam preparation questions and create a personalized curriculum just for you. Stop wasting time on concepts you've already mastered and start focusing on what you truly need to learn to pass your certification by visiting MindMesh Academy.
Ready to Get Certified?
Prepare with expert-curated study guides, practice exams, and spaced repetition flashcards at MindMesh Academy:

Written by
Alvin Varughese
Founder, MindMesh Academy
Alvin Varughese is the founder of MindMesh Academy and holds 15 professional certifications including AWS Solutions Architect Professional, Azure DevOps Engineer Expert, and ITIL 4. He's held senior engineering and architecture roles at Humana (Fortune 50) and GE Appliances. He built MindMesh Academy to share the study methods and first-principles approach that helped him pass each exam.