7 Sample CISSP Test Questions to Ace the Exam in 2025
7 Sample CISSP Test Questions to Ace the Exam in 2025
For IT professionals aiming for the Certified Information Systems Security Professional (CISSP) certification, true mastery goes beyond rote memorization. The CISSP exam challenges you to think critically, applying security concepts as a strategic leader, not just a technical expert. This "think like a manager, not a technician" philosophy, embedded by (ISC)², is crucial for success.
This article offers a curated sample CISSP test experience, meticulously designed by MindMesh Academy to bridge the gap between theoretical knowledge and practical application. We'll delve into realistic practice questions across the core domains, moving beyond simple right-or-wrong answers to dissect the underlying logic and decision-making processes required.
Each question in this guide comes with a comprehensive explanation, detailing not only why the correct answer is the optimal choice but also why the other options fall short. This strategic breakdown is vital for developing the critical thinking skills demanded by the exam. You'll gain insight into how questions are structured, learn to identify common distractors, and master the art of focusing on keywords that reveal the examiner's true intent. By engaging with these examples, you'll not only assess your current readiness but also refine your test-taking strategy, ensuring you're thoroughly prepared for the unique challenge of the CISSP exam. Let's begin our deep dive.
1. Security and Risk Management Domain Question
The Security and Risk Management domain forms the absolute bedrock of the CISSP exam, consistently representing the largest portion of the test. For IT professionals, this domain isn't just about security; it's about understanding how security integrates with and supports core business objectives. Questions here assess your ability to operate as a security manager or executive, focusing on the establishment, governance, and continuous improvement of an organization's information security program.
This domain demands that you move beyond purely technical solutions. Instead, it requires a deep understanding of governance principles, widely recognized risk management frameworks (like NIST or ISO 27005), and the critical alignment of security initiatives with broader business goals. A typical question in a sample CISSP test for this domain might present a scenario where you must choose the most appropriate risk response strategy, contribute to developing a robust security policy, or ensure unwavering regulatory compliance. This perspective is vital, echoing the strategic thinking required in roles like Project Manager (PMP) when assessing project risks or IT Service Managers (ITIL) establishing governance frameworks.
Example Question and Analysis
Question: An organization has identified a risk to an asset valued at $10,000. The potential loss from a single occurrence of the risk is estimated to be $4,000, and this event is expected to happen once every five years. The cost to implement a countermeasure is $1,000 annually. Which is the MOST appropriate risk response?
- A) Risk Mitigation
- B) Risk Acceptance
- C) Risk Transfer
- D) Risk Avoidance
Strategic Breakdown:
- Analyze the Core Conflict: This scenario presents a classic managerial dilemma: whether to invest in a security control or accept the potential financial impact of a risk. The key is to determine which approach is more economically sound for the business. This isn't about technical perfection but financial prudence.
- Calculate the Numbers: We need to compare the cost of the countermeasure with the expected annual cost of the risk.
- Single Loss Expectancy (SLE): $4,000 (potential loss from one event).
- Annualized Rate of Occurrence (ARO): 1 event every 5 years = 1/5 = 0.2.
- Annualized Loss Expectancy (ALE): SLE × ARO = $4,000 × 0.2 = $800.
- Compare Costs: The countermeasure costs $1,000 per year, while the risk's expected annual financial impact (ALE) is $800. Implementing the control would cost the organization more annually than the average financial loss it's designed to prevent.
Correct Answer: B) Risk Acceptance. From a business and financial perspective, it is not prudent to spend $1,000 annually to prevent an average expected loss of $800. In this specific scenario, accepting the risk is the most cost-effective and business-savvy decision, aligning with the "think like a manager" principle.
Actionable Takeaways
To truly master this domain, you must consistently adopt a managerial mindset. Every security decision should be evaluated based on how it supports the business's mission, its financial health, and its overall risk appetite. For instance, an AWS Security Specialty professional often faces similar trade-offs when designing cloud security controls. Robust security programs are not just about firewalls; they are about establishing policies, conducting thorough risk analyses, and ensuring effective security education and awareness.
Reflection Prompt: Consider a security control you recently encountered. If you were the security manager, what factors beyond its technical effectiveness would you consider before approving its implementation? (e.g., cost, operational impact, regulatory requirements, user experience).
Remember to prioritize decisions based on a thorough, business-aligned risk analysis rather than purely technical perfection. You can review an ultimate guide to compliance and privacy training to further delve into the foundational aspects of security and risk.
2. Asset Security Domain Question
The Asset Security domain rigorously tests your understanding of the entire lifecycle of information and the assets that process it. For any IT professional, this means recognizing that data, regardless of where it lives (on-premises or in the cloud, like in an Azure environment), is an organization's most critical asset. Questions in this domain focus on the classification, ownership, and protection of data, ensuring that appropriate controls are applied from its creation through to its eventual destruction. This is particularly relevant for roles dealing with data governance, privacy compliance (e.g., GDPR, HIPAA), or cloud architects designing secure data storage solutions.
A key part of any sample CISSP test will involve scenarios probing your knowledge of data states (at rest, in transit, in use), the various data roles (owner, custodian, user), and, crucially, secure data disposal methods. These questions demand knowledge of both specific technical methods and the overarching policies that govern them, making it a critical area for demonstrating practical security acumen.
 Caption: Effective Asset Security spans the entire data lifecycle, from classification to secure disposal.
Caption: Effective Asset Security spans the entire data lifecycle, from classification to secure disposal.
Example Question and Analysis
Question: A company is decommissioning several solid-state drives (SSDs) that contained highly sensitive proprietary research data. The drives must be reused by another department that handles public-facing marketing materials. Which data sanitization method is MOST appropriate to ensure no data remanence?
- A) Degaussing
- B) Overwriting with a single pass of zeros
- C) Cryptographic Erase (Crypto Shredding)
- D) Physical destruction
Strategic Breakdown:
- Analyze the Core Conflict: The primary goal is to securely sanitize SSDs to eliminate data remanence, but with an important secondary constraint: the drives need to be reused. This immediately rules out methods that render the drive unusable. The crucial element here is understanding the unique characteristics of SSDs compared to traditional HDDs.
- Evaluate the Options:
- A) Degaussing: This method uses strong magnetic fields to scramble data on magnetic media (HDDs, tapes). SSDs are flash-based and do not rely on magnetism, so degaussing is ineffective and can even damage them.
- B) Overwriting with a single pass of zeros: While effective for HDDs, a single-pass overwrite is unreliable on SSDs. Due to wear-leveling algorithms and over-provisioning, data blocks are moved around, and not all data on an SSD is guaranteed to be overwritten or accessible through the logical block addressing.
- D) Physical destruction: This is highly effective at preventing data recovery but makes the drive unusable, contradicting the reuse requirement.
- Identify the Best Fit: Cryptographic Erase, often referred to as Crypto Shredding, is the industry-standard method for securely sanitizing modern SSDs that leverage built-in encryption. It involves deleting the media encryption key (MEK) used to encrypt all data on the drive. Once this key is deleted, all encrypted data on the drive is instantly rendered irretrievable without destroying the physical media, thus allowing for reuse.
Correct Answer: C) Cryptographic Erase (Crypto Shredding). This is the most effective and efficient method for sanitizing modern SSDs when they are to be reused. It leverages the drive's built-in encryption capabilities to make data recovery infeasible without destroying the physical media, perfectly balancing security and operational needs.
Actionable Takeaways
To excel in this domain, you must not only understand but also internalize the specifics of data handling across various media types. Always consider two critical factors: the classification of the data (e.g., public, confidential, secret) and the type of media it's stored on (e.g., HDD, SSD, tape, cloud object storage). For your exam preparation and practical application, consider creating a comprehensive chart comparing different data sanitization methods (clearing, purging, destroying) against various media types, noting their suitability and limitations.
Reflection Prompt: How might a company's data retention policy influence the choice of data sanitization methods, especially when considering compliance with regulations like GDPR or HIPAA?
A firm grasp of these technical details, combined with a policy-driven mindset, is essential for any sample CISSP test you encounter and for real-world secure data management.
3. Security Architecture and Engineering Question
The Security Architecture and Engineering domain is often considered one of the most technical and intellectually demanding areas covered in the CISSP exam. It delves deeply into the concepts, principles, and standards used to design, implement, and integrate secure systems from their inception. For IT professionals, this means understanding how to build security into solutions, rather than bolting it on as an afterthought. This domain is particularly relevant for roles like Solution Architects (e.g., AWS Solutions Architect, Azure Solutions Architect) or Security Engineers, who are tasked with designing resilient and secure infrastructures.
Questions from this domain test your understanding of foundational security models (like Bell-LaPadula or Biba), cryptographic systems, and the secure engineering processes used to build resilient systems from the ground up. These scenarios often require you to apply core security principles such as defense in depth, least privilege, or secure failure modes to complex system designs. A common question you might find in a sample CISSP test for this domain involves selecting the correct cryptographic tool or approach for a specific job, a critical skill for any security professional involved in system design.
 Caption: Security Architecture and Engineering focuses on building robust, resilient systems with security principles integrated from design through implementation.
Caption: Security Architecture and Engineering focuses on building robust, resilient systems with security principles integrated from design through implementation.
Example Question and Analysis
Question: A software developer needs to send a large, encrypted data file to a colleague. To ensure both confidentiality and the integrity of the sender's identity, which of the following combinations of cryptographic primitives should be used?
- A) The file is encrypted with the sender's private key, and a hash is created using the recipient's public key.
- B) The file is encrypted with a symmetric key, and the symmetric key is then encrypted with the recipient's public key. A hash of the file is created and then signed with the sender's private key.
- C) The file is encrypted with the recipient's public key, and a hash of the file is signed with a symmetric key.
- D) The file is encrypted with a symmetric key, and the symmetric key is then signed with the sender's private key.
Strategic Breakdown:
- Analyze the Core Conflict: This scenario has two distinct and crucial requirements:
- Confidentiality: Only the intended recipient should be able to read the file.
- Integrity & Non-Repudiation: The recipient must be assured that the file has not been altered in transit and that it genuinely came from the claimed sender. The key is applying the correct cryptographic tools for each specific need.
- Deconstruct the Process (Hybrid Cryptography):
- Large Files and Symmetric Keys: Asymmetric encryption (public/private keys) is computationally intensive and too slow for encrypting large files directly. Therefore, a hybrid approach is standard: a fast symmetric key (also called a session key) is used for bulk data encryption.
- Confidentiality for the Symmetric Key: To ensure only the recipient can decrypt the symmetric key (and thus the file), that symmetric key itself must be encrypted using the recipient's public key. Only the recipient's corresponding private key can then decrypt the symmetric key.
- Integrity and Non-Repudiation (Digital Signature): To prove the sender's identity and ensure the file's integrity, a digital signature is used. This involves creating a hash (a unique fingerprint) of the original file. This hash is then encrypted (signed) using the sender's private key. The recipient can then verify this signature using the sender's public key.
- Evaluate the Options:
- A) Incorrect. Encrypting with the sender's private key means anyone with the sender's public key can decrypt it, violating confidentiality.
- C) Incorrect. Encrypting with the recipient's public key for a large file is inefficient. Signing a hash with a symmetric key doesn't provide non-repudiation (multiple parties could share the symmetric key).
- D) Incorrect. Signing the symmetric key with the sender's private key doesn't ensure confidentiality for the data itself, nor does it guarantee the integrity of the entire file.
- B) This option correctly combines symmetric encryption for the large file (for speed), asymmetric encryption for the symmetric key (for confidential key exchange), and a digital signature (hash signed with sender's private key) for integrity and non-repudiation.
Correct Answer: B) This method provides comprehensive security. Confidentiality is ensured because only the recipient's private key can decrypt the symmetric key needed to open the file. Integrity and non-repudiation are provided because only the sender's private key could have created the unique signature for the file's hash, which can then be verified by the recipient.
Actionable Takeaways
To truly succeed in this domain, you must move beyond simply memorizing cryptographic algorithms and deeply understand their practical applications and limitations. Grasp the fundamental differences between symmetric and asymmetric cryptography, hashing, and digital signatures. Focus on the "why" behind each tool: symmetric for speed (confidentiality of bulk data), asymmetric for secure key exchange, authentication, and non-repudiation (digital signatures), and hashing for integrity verification. This conceptual understanding is critical for securely designing systems, a skill paramount for DevSecOps professionals and anyone building secure applications.
Reflection Prompt: How is this hybrid encryption approach reflected in common security protocols you use daily (e.g., HTTPS, secure email)? What are the advantages of combining these methods?
A firm grasp of these core concepts is essential for answering the technical, application-focused questions found in any quality sample CISSP test.
4. Communication and Network Security Question
The Communication and Network Security domain is a cornerstone of the CISSP exam, assessing your understanding of how to design, build, and protect network infrastructures. For IT professionals, a secure network is the backbone of all operations, whether on-premises, in the cloud, or in hybrid environments. Questions in this area span a vast range, from the foundational OSI and TCP/IP models to modern concepts like Zero Trust Architecture, Software-Defined Networking (SDN), and secure cloud connectivity. This knowledge is invaluable for Network Engineers, Cloud Architects (e.g., those pursuing the AWS Certified Advanced Networking - Specialty certification), and anyone responsible for securing data in transit.
A question in a sample CISSP test for this domain will often test your ability to apply security principles to network protocols, transmission methods, and hardware devices. You will be expected to identify vulnerabilities in diverse network designs and select the appropriate controls, such as next-generation firewalls, Intrusion Prevention Systems (IPS), secure VPN protocols, or micro-segmentation strategies, to effectively mitigate identified threats.
Example Question and Analysis
Question: An attacker is attempting to disrupt a TLS session by inserting themselves between a client and a server. They are capturing the initial handshake packets and replaying them to both parties, hoping to manipulate the cryptographic negotiation. At which layer of the OSI model is this attack primarily occurring?
- A) Layer 2 (Data Link)
- B) Layer 4 (Transport)
- C) Layer 5 (Session)
- D) Layer 7 (Application)
Strategic Breakdown:
- Analyze the Core Conflict: The attack specifically targets the establishment and maintenance of a secure communication channel, focusing on the Transport Layer Security (TLS) handshake process. The key is to correctly identify where session management and the negotiation of a secure channel occur within the OSI model's layered architecture.
- Identify Key Protocols and Their Purpose: Transport Layer Security (TLS) and its predecessor, Secure Sockets Layer (SSL), are protocols designed to establish secure communication sessions over a network. Their primary function is to manage the state of a connection between two endpoints, handling the setup, encryption, maintenance, and eventual teardown of that secure session.
- Map to the OSI Model:
- While TLS provides encryption that ultimately protects data exchanged at the Application Layer (Layer 7) and operates over the Transport Layer (Layer 4) TCP connection, the TLS handshake itself is concerned with initiating, managing, and terminating a session between the client and server.
- The Session Layer (Layer 5) is explicitly responsible for establishing, managing, and terminating the connections (sessions) between applications. It handles dialogue control and synchronization. Manipulating the handshake to disrupt or hijack the secure communication falls squarely within the responsibilities of this layer.
*Caption: A detailed explanation of the OSI Model and its layers, crucial for understanding network security concepts.*Correct Answer: C) Layer 5 (Session). The attack specifically targets the TLS handshake, which is a session-level process dedicated to establishing and maintaining a secure communication channel between two parties. While TLS secures application-layer data and relies on transport-layer services, the attack against the handshake itself is a manipulation of the session establishment process.
Actionable Takeaways
To succeed in this domain, you must possess a rock-solid understanding of both the OSI and TCP/IP models. Don't simply memorize the layers; strive to understand the function of each layer, the key protocols that operate at that layer, and the types of devices or attacks relevant to it. This foundational knowledge is crucial for diagnosing network attacks, identifying vulnerabilities, and selecting the correct security controls (e.g., knowing a WAF operates at Layer 7 while a traditional firewall primarily works at Layers 3-4).
Reflection Prompt: How does understanding the OSI model help you diagnose where a network attack (e.g., a SYN flood, a SQL injection) might be occurring and what security controls would be most effective?
Always think in layers when analyzing a network security problem on a sample CISSP test or in a real-world scenario. For a deeper dive into practical implementations, explore various network security controls and their implementation.
5. Identity and Access Management (IAM) Question
The Identity and Access Management (IAM) domain is absolutely critical for any modern organization, ensuring that the right individuals and services access the right resources, at the right times, and for the right reasons. For IT professionals, particularly those managing cloud environments like AWS IAM or Azure Active Directory, IAM is the gatekeeper of the entire digital infrastructure. Questions from this domain on a sample CISSP test rigorously evaluate your knowledge of authentication (verifying identity), authorization (granting permissions), and accountability (logging actions). They cover the entire identity lifecycle, from initial provisioning and role assignment to regular review and eventual deprovisioning, and test your understanding of various access control models (e.g., RBAC, ABAC) and identity technologies (e.g., SSO, federation, biometrics).
These questions often present complex scenarios requiring you to select the appropriate access control model, analyze the effectiveness and trade-offs of an authentication system, or design an identity federation solution for hybrid environments. Success in this domain hinges on knowing how to implement foundational security principles like least privilege (granting only necessary permissions) and separation of duties (preventing a single individual from controlling critical processes end-to-end) within increasingly complex IT landscapes.
 Caption: IAM systems are central to granting and managing digital identities, ensuring only authorized access to critical resources.
Caption: IAM systems are central to granting and managing digital identities, ensuring only authorized access to critical resources.
Example Question and Analysis
Question: A security manager is evaluating two biometric systems. System A has a False Rejection Rate (FRR) of 4% and a False Acceptance Rate (FAR) of 2%. System B has an FRR of 2% and a FAR of 4%. The system will be used to control access to a highly sensitive data center. Which system should be chosen and why?
- A) System A, because a lower FAR is more important for security.
- B) System B, because a lower FRR provides better usability for authorized personnel.
- C) Either system is acceptable as their Crossover Error Rate (CER) is likely similar.
- D) System A, because a higher FRR indicates stricter matching criteria.
Strategic Breakdown:
- Analyze the Core Conflict: This question presents a classic security versus usability dilemma, forcing a choice between preventing unauthorized access (security) and ensuring legitimate users aren't inconvenienced (usability). The critical factor is the context provided in the scenario.
- Evaluate the Context: The system is intended to protect a "highly sensitive data center." This context is paramount. In high-security environments, the absolute top priority is to prevent any unauthorized access (false positives), even if it means legitimate users might experience occasional inconveniences (false negatives).
- Define and Compare the Metrics:
- False Acceptance Rate (FAR): The rate at which an unauthorized user is incorrectly granted access. A lower FAR means higher security against intruders.
- False Rejection Rate (FRR): The rate at which an authorized user is incorrectly denied access. A lower FRR means better usability for legitimate users.
- System A: FAR of 2%, FRR of 4%. (More secure, less usable)
- System B: FAR of 4%, FRR of 2%. (Less secure, more usable)
- Prioritize Based on Context: For a "highly sensitive data center," preventing an unauthorized person from gaining entry is far more critical than ensuring authorized personnel never experience a failed scan. Therefore, the system with the lower FAR is the superior choice.
Correct Answer: A) System A, because a lower FAR is more important for security. In a high-security environment, the primary goal is to prevent unauthorized entry. A lower False Acceptance Rate directly supports this objective, making System A the superior choice despite its slightly higher inconvenience (FRR) for legitimate users.
Actionable Takeaways
To master IAM questions, always consider the context of the scenario. The trade-off between security and usability is a recurring theme, and the specific environment (e.g., a data center vs. an employee time clock) will dictate the optimal choice. Memorize the definitions of FAR, FRR, and Crossover Error Rate (CER - where FAR and FRR are equal, indicating overall accuracy). Understand that while a lower CER generally indicates a more accurate system, the priority of a low FAR or FRR depends entirely on the scenario's security requirements. When security is the absolute priority, always favor the option with the lower FAR.
Reflection Prompt: How might a hybrid access control system (e.g., multi-factor authentication combined with biometrics) help mitigate the inherent trade-offs between FAR and FRR?
To build a stronger foundation in this area, you can gain a deeper understanding with this IAM deep dive. Always link your choice back to core security principles like least privilege and defense-in-depth, and consider the business impact of each decision.
6. Security Assessment and Testing Domain Question
The Security Assessment and Testing domain is crucial for any IT professional focused on maintaining a robust security posture. It challenges your understanding of the tools, techniques, and structured processes used to verify and validate an organization's defenses proactively. Questions in this area assess your knowledge of vulnerability assessments, penetration tests, comprehensive security audits, and the ongoing monitoring required to maintain effective security controls in dynamic environments. This domain is particularly relevant for security analysts, auditors (like those preparing for the CISA certification), and QA professionals integrating security into the development lifecycle.
These questions require you to differentiate between various testing methodologies and accurately know when to apply them based on specific objectives and available information. A typical question on a sample CISSP test might ask you to choose the correct testing approach based on provided context, interpret the results of a security scan, or understand the responsibilities involved in a formal security audit. Understanding these distinctions is fundamental to building a proactive and effective security program.
Example Question and Analysis
Question: A security team is hired to perform a penetration test on a new web application before it goes live. The client provides the testing team with full access to application architecture diagrams, source code, and user credentials for various roles. Which type of testing methodology is being employed?
- A) Black-Box Testing
- B) Gray-Box Testing
- C) White-Box Testing
- D) Double-Blind Testing
Strategic Breakdown:
- Analyze the Core Conflict: The question hinges entirely on the level of information provided to the penetration testing team. Each answer choice represents a different degree of knowledge granted to the testers, from none (simulating an external attacker) to complete (simulating an insider with full system knowledge).
- Identify Key Information: The critical phrase is "full access to application architecture diagrams, source code, and user credentials for various roles." This signifies comprehensive and total transparency from the client to the testing team, effectively giving them an "insider's view."
- Match Information to Methodology:
- A) Black-Box Testing: Testers have zero prior knowledge of the system's internal workings. It simulates an external attacker.
- B) Gray-Box Testing: Testers have partial knowledge, such as user-level credentials or some network diagrams, but not full internal access. It simulates a user with some elevated privileges or a targeted attacker with reconnaissance.
- C) White-Box Testing: Also known as crystal-box testing, this approach provides testers with complete internal knowledge of the system, including source code, architecture, and potentially administrative access. This matches the scenario perfectly.
- D) Double-Blind Testing: Neither the testers nor the target organization's staff (except perhaps a single point of contact) are aware that a test is taking place. This tests the organization's incident response capabilities.
- Conclusion: Given the complete transparency and access provided, white-box testing is the only appropriate classification.
Correct Answer: C) White-Box Testing. This approach provides the testers with comprehensive internal knowledge of the target system, including source code and architecture. It is the most thorough and time-efficient method for identifying deep-seated vulnerabilities within the application's code and design, particularly effective before deployment.
Actionable Takeaways
To succeed in this domain, you must clearly distinguish between the goals and methodologies of different security tests. Understand that a vulnerability scan identifies known weaknesses, whereas a penetration test actively exploits vulnerabilities to assess impact. Know the specific circumstances that call for a white-box, gray-box, or black-box approach. Focus on the why behind a test, not just the what. For instance, a white-box test is ideal for an internal development team trying to secure code pre-release or for highly critical systems, while a black-box test better simulates an external attacker with no prior knowledge, assessing external defenses.
Reflection Prompt: When would a company choose a gray-box penetration test over a white-box or black-box approach, and what specific types of vulnerabilities might it uncover more effectively?
This strategic thinking, grounded in practical application, is key to passing your CISSP exam and effectively managing an organization's security assessments.
7. Security Operations Question
The Security Operations domain covers the critical day-to-day activities that ensure an organization's continuous security posture. For IT professionals, this is the frontline of defense, where theory meets reality in managing ongoing threats and incidents. Questions in this domain test your understanding of incident response lifecycles, disaster recovery planning, business continuity, comprehensive logging and monitoring, forensic investigations, and the protection of operational resources. It's a highly practical domain focused on real-world events and the established processes used to handle them effectively. This domain is essential for roles like Incident Responders, SOC Analysts, and Security Analysts who are directly involved in defending an organization's digital assets.
A question from this domain on a sample CISSP test will often present a scenario involving a security event or an operational failure. You will be expected to know the correct procedures, from identifying an incident to containing the threat, collecting forensic evidence, and restoring normal operations, all while following established best practices like those found in NIST SP 800-61 (the guide for Computer Security Incident Handling).
Example Question and Analysis
Question: An analyst is collecting digital evidence from a compromised system that is still running. According to the order of volatility, which of the following should be collected FIRST?
- A) Hard drive image
- B) RAM and cache contents
- C) Archived backup tapes
- D) Network traffic logs from the firewall
Strategic Breakdown:
- Analyze the Core Conflict: The question is about the preservation of digital evidence in a forensic investigation, specifically concerning a running system. The core principle here is the "order of volatility," which dictates that the most ephemeral data – data most likely to be lost or altered – must be collected first.
- Evaluate Volatility: We need to rank the listed items from most to least volatile:
- RAM and cache contents: These are extremely volatile. They exist only while the system is powered on and actively running processes. Any power loss or system shutdown will instantly destroy this data.
- Network traffic logs (from the firewall): While important, these are typically stored on a separate, dedicated logging device and are less volatile than live system memory. They are persistent on the logging system.
- Hard drive image: This is a persistent storage medium. While it can be altered, the data on it is not immediately lost upon system shutdown in the same way RAM is.
- Archived backup tapes: These are offline, long-term storage and are the least volatile, often immutable, representing a historical snapshot.
- Prioritize Collection: Based on the principle of volatility, the contents of RAM and CPU cache are the most ephemeral and crucial to capture immediately from a live system, as they hold critical evidence like running processes, open network connections, and decrypted data that might not be found elsewhere.
Correct Answer: B) RAM and cache contents. This data is transient and will be destroyed if the machine loses power or is restarted. Therefore, capturing the live memory is the critical first step in a forensic investigation of a running compromised system, as it contains invaluable insights into the attacker's activities.
Actionable Takeaways
To succeed in this domain, you must not only memorize key processes like the incident response lifecycle (Preparation, Detection & Analysis, Containment, Eradication, Recovery, Post-Incident Activity) but also understand the practical implications of concepts like the order of volatility. This principle is fundamental for any IT professional involved in incident handling, whether in an AWS cloud environment or on-premises.
The following infographic outlines the initial, critical phases of incident response, emphasizing how actions are taken in a logical, effective order to minimize damage and preserve evidence.
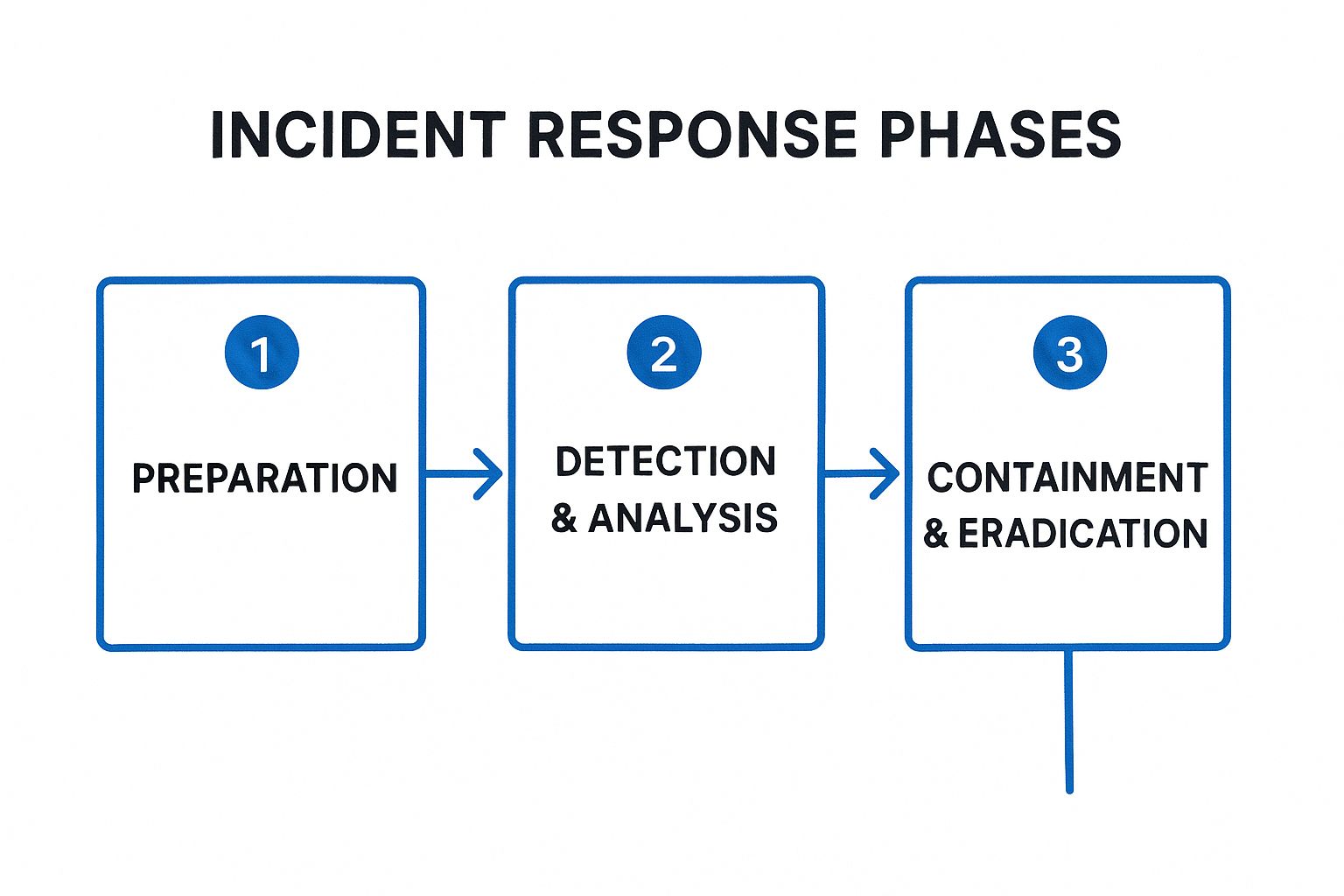 Caption: The initial phases of incident response, a crucial framework for any security operations team.
Caption: The initial phases of incident response, a crucial framework for any security operations team.
Reflection Prompt: Beyond collecting RAM, what other highly volatile data sources might you prioritize in a live system forensic investigation, and why? (e.g., running processes, network connections, command history).
For more detail on logging, monitoring, and the incident response framework, you can learn more about the 5 phases of incident response. Also, understanding a guide to remote cyber security can provide context for how these operations adapt to distributed environments.
7-Domain CISSP Question Comparison
| Domain / Question Type | Implementation Complexity 🔄 | Resource Requirements ⚡ | Expected Outcomes 📊 | Ideal Use Cases 💡 | Key Advantages ⭐ |
|---|---|---|---|---|---|
| Security and Risk Management | High - strategic thinking needed 🔄 | Moderate - knowledge of frameworks & laws ⚡ | Strong understanding of governance, compliance, risk | Executive security decision making, policy setting | Foundational for all domains; aligns security & business ⭐ |
| Asset Security | Medium - technical but straightforward 🔄 | Moderate - familiarity with privacy laws & data handling ⚡ | Effective data protection across lifecycle | Daily security operations, breach prevention | Practical with clear answers; data-focused ⭐ |
| Security Architecture and Engineering | High - very technical 🔄 | High - deep cryptographic & system design knowledge ⚡ | Robust secure system designs & cryptography understanding | Secure system engineering, vulnerability assessment | Well-documented standards; foundation for controls ⭐ |
| Communication and Network Security | Medium-High - technical but practical 🔄 | Moderate - networking protocols & devices ⚡ | Secure network design and defense against attacks | Network infrastructure security, cloud & wireless security | Builds on common networking knowledge; testable concepts ⭐ |
| Identity and Access Management (IAM) | Medium - conceptual & some technical 🔄 | Moderate - understanding complex models & biometrics ⚡ | Strong identity protection and access control | User authentication/authorization, lifecycle management | Relevant across technologies; clear frameworks ⭐ |
| Security Assessment and Testing | Medium - practical understanding 🔄 | Moderate - knowledge of testing tools & frameworks ⚡ | Measurable validation of security controls & vulnerabilities | Security audits, penetration testing, compliance | Practical & standardized methodologies ⭐ |
| Security Operations | Medium - procedural knowledge 🔄 | Moderate - procedural and technical knowledge ⚡ | Effective incident response and continuous security ops | Incident handling, disaster recovery, forensics | Real-world scenarios; well-established procedures ⭐ |
Final Thoughts
Navigating the extensive landscape of the CISSP certification exam is a journey of strategic learning, not just rote memorization. The sample CISSP test questions we've dissected throughout this article are more than just practice exercises; they are a vital blueprint for understanding the exam's core philosophy and the managerial mindset it seeks to evaluate. By moving beyond simply knowing the right answer, you cultivate the ability to identify the best answer from the critical perspective of a security manager or risk advisor.
Each domain, from the foundational Security and Risk Management to the practical realm of Security Operations, requires you to adopt a specific strategic mindset. The questions are meticulously designed to test your judgment and decision-making abilities within realistic, complex business contexts. As we've seen, the correct choice often hinges on principles like due care, due diligence, prioritizing risk mitigation, and ensuring strict alignment with broader organizational goals and regulatory requirements.
Key Strategies for CISSP Success: Insights from Our Analysis
To truly prepare for the CISSP, internalize these critical strategies that our detailed question breakdowns have revealed:
- Embrace the Managerial Mindset: The CISSP is fundamentally a management-level exam. Your primary lens should always be business-oriented, focusing on risk posture, cost-effectiveness, and the broader organizational impact of security decisions. Technical solutions are often secondary to establishing robust policies, processes, and governance.
- Deconstruct Each Question Meticulously: Pay obsessive attention to keywords like "first," "best," "most," "least," and phrases that describe criticality (e.g., "highly sensitive"). These words are crucial signals that frame the scenario and guide you toward the most appropriate answer, often helping to eliminate options that are technically correct but strategically inferior for the given context.
- (ISC)²'s Ethical Hierarchy is Paramount: When faced with difficult choices, always prioritize security decisions in the following order: first, safeguard human life and safety; second, ensure adherence to organizational policies and procedures; third, protect sensitive data and assets. This ethical hierarchy is a powerful tool for eliminating distractors in ambiguous or complex scenarios.
- Connect the Domains: Real-world security problems rarely fit neatly into a single domain. Practice thinking about how concepts from different CISSP domains interrelate. For example, a risk management decision (Domain 1) might impact asset security (Domain 2), which then influences the architecture of a solution (Domain 3) and its operational monitoring (Domain 7).
Your Actionable Path Forward
Mastering the CISSP is an iterative process that demands continuous engagement and critical reflection. The immense value of a sample CISSP test lies in its ability to expose your weak areas and refine your analytical skills. Don't just aim for a high score on practice exams; aim for a deep, intuitive understanding of why each correct answer is optimal and, just as importantly, why each incorrect answer is wrong. This level of granular analysis is what builds the critical thinking muscles essential for success on exam day and in your professional career.
Use the detailed explanations from these practice questions to create a robust feedback loop for your study. If you struggled with a question on Security Architecture and Engineering, for instance, revisit the fundamental security models, cryptographic principles, and secure development lifecycles within that domain. This targeted approach ensures your study time is both efficient and profoundly effective.
Ultimately, preparing for the CISSP exam is a significant investment in your professional future. Earning this prestigious certification not only validates your expertise and commitment to information security but also unlocks significant career opportunities and positions you as a leader in the field. By embracing the strategic mindset required and utilizing practice questions as a potent diagnostic tool, you are not just preparing to pass a test; you are actively preparing to become a highly competent and respected cybersecurity leader.
Ready to elevate your preparation with comprehensive resources and structured learning pathways? Explore the full suite of CISSP training materials at MindMesh Academy, where our expertly crafted practice exams, in-depth courses, and tailored study guides are designed to transform your certification goals into a tangible reality. Visit MindMesh Academy to discover how we can help you achieve your cybersecurity aspirations.

Written by
Alvin Varughese
Founder, MindMesh Academy
Alvin Varughese is the founder of MindMesh Academy and holds 15 professional certifications including AWS Solutions Architect Professional, Azure DevOps Engineer Expert, and ITIL 4. He's held senior engineering and architecture roles at Humana (Fortune 50) and GE Appliances. He built MindMesh Academy to share the study methods and first-principles approach that helped him pass each exam.